You are performing an advanced search of all detections in the last 90 days in your environment and want to group the detections via the FileName and CommandLine parameters for easier viewing. Which query will group the detections correctly?
You suspect that a user is abusing their admin privileges and you want to see the recent commands they have been utilizing. Which Investigate search will identify this?
A detection contains a suspicious process named "reallysus.exe". This process has a TargetProcessId of 123456789. Which query will return all of the events associated with this process?
Refer to the exhibit.
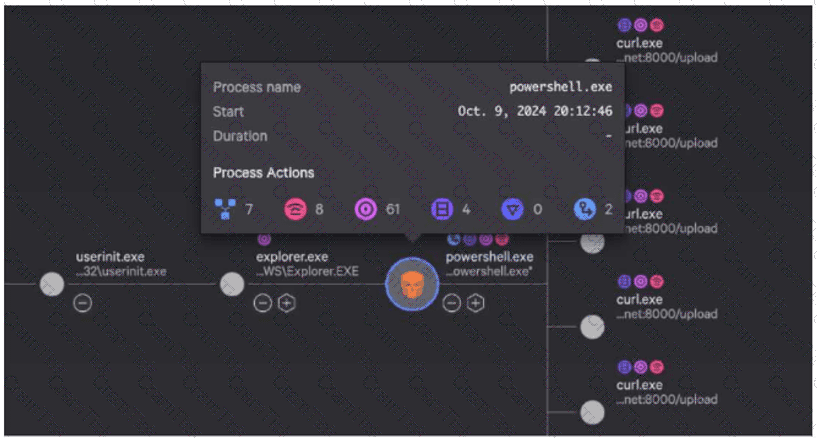
While investigating a process tree, you hover over a malicious powershell.exe process. What is the correct sequence of Process Actions?
Falcon Machine Learning has prevented and quarantined a file being written to disk that has VSCode as a parent process. This file was compiled by the system owner. What should the next steps be?
Refer to the image. Which query will show file execution from a suspicious directory across all hosts?
Where can you find details about key data fields to use in an advanced search query?
Which hunting query's results could indicate that an adversary is performing reconnaissance from a specific host?
Falcon is generating detections for a malicious file evil.exe with varying filepaths on several hosts as end users attempt to execute the file. Which query can be used to proactively hunt where the file exists prior to the user executing it?
Which statement will filter for all events that correspond to a new scheduled task registered by the user "Doris"?
Which CQL query would output relevant data in tracking USB storage device usage?
What can a hunter add at the end of a search string in Advanced Event Search to identify outliers when quantifying the results?
What would allow you to quickly generate a graphical view of Indicator of Compromise (IOC) relationships surrounding a malicious file that was seen being loaded?
Your organization has identified a malicious Scheduled task that executes every 5 minutes. Which LogScale event search function can be used to quickly identify and display the unique hosts affected by the malware?
CCFH |


