Refer to the exhibit.
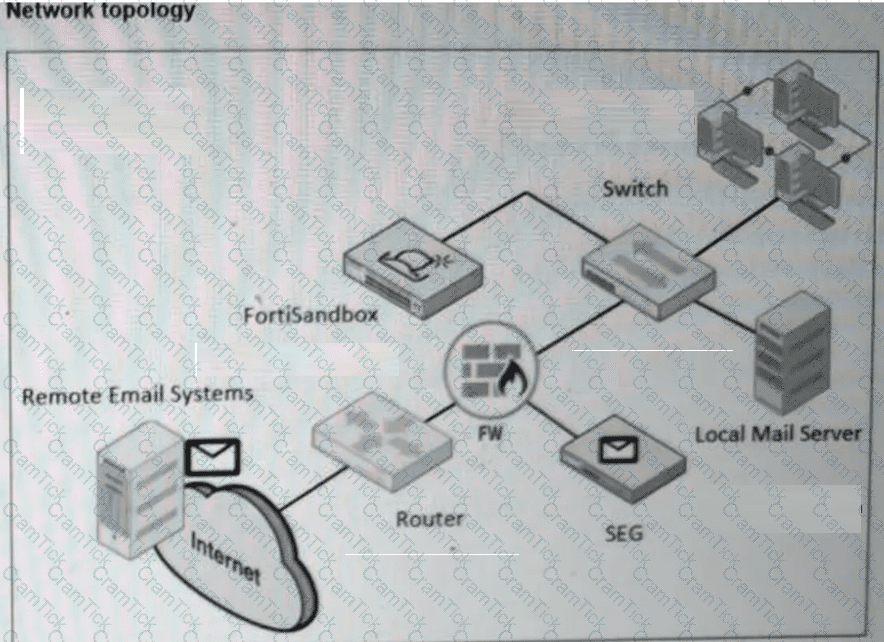
A network topology is shown. Which two important steps must you take before you enable a BCC adapter on FortiSandbox? (Choose two answers)
Refer to the exhibit.

As a best practice, where must you rank the FortiClient inputs when configuring the job queue priority on FortiSandbox? (Choose one answer)
You are asked to configure FortiSandbox to use one VM instance for multiple sequential scan jobs without shutting down the instance between each scan job submission. Which scan profile setting must you enable to achieve this? (Choose one answer)
A FortiSandbox HA cluster is configured with the MTA adapter. What does the primary node do when it receives MTA jobs? (Choose one answer)
A FortiSandbox VM has been deployed and has been functioning correctly for several months. Suddenly, the system begins rejecting file submissions with an error message indicating a licensing problem. How can you determine, using the CLI, if the license is still valid? (Choose one answer)
Refer to the CLI configuration below.
set device-authorization -a
How will FortiSandbox authorize new FortiClient devices after this command? (Choose one answer)
You determine that there are a large number of samples on FortiSandbox that are obsolete and no longer needed for future analysis. Which CLI tool must you use to remediate this issue? (Choose one answer)
A security analyst is reviewing a scan job report that indicates a true positive match. The job report displays that the malware attempts to replace vital system executables. Which type of malware is the analyst observing? (Choose one answer)
You notice a recent file downloaded by some end stations is exhibiting malware behavior, however, on the sandbox the file is rated clean. After further investigation you determine that only end stations using the Opera browser are being affected. What must you do to prevent these infections? (Choose one answer)


