For which two reasons should organizations customize their incident response plans based on NIST SP 800-61 or another incident response standard? (Select two.)
What is the primary function of the People Page in the Threat Protection Workbench and TAP Dashboard?
Which two factors make Business Email Compromise (BEC) attacks difficult to detect? (Select two.)
An analyst wants to use the Threats page in TAP Dashboard to review all messages related to a phishing campaign that contain an attachment. What is the correct method to filter these messages?
Which two threat protection capabilities are available as part of Proofpoint’s Targeted Attack Protection (TAP)? (Select two.)
The Attack Index is a calculation of the overall threat burden for a particular user. Which listed factor contributes to this calculation?
A college student receives the email shown in the exhibit.
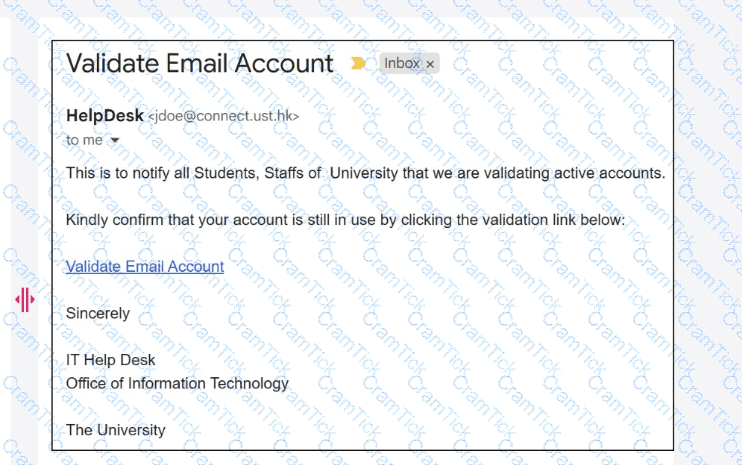
What type of attack is being performed?
Which two items should be included in an incident report to be discussed during a post-incident debrief? (Select two.)


