An administrator has been tasked with upgrading the Nutanix cluster to a newer version of AOS. The cluster is running a mix of different versions across nodes... What is the recommended first step when upgrading a Nutanix cluster with different AOS versions across nodes?
An administrator notices that several VMs in a Nutanix AHV cluster are intermittently losing network connectivity. In Prism Central, a critical alert appears: "Network Function VM (NFVM) packet processing delays" What is the next step that the administrator should take for this issue?
An administrator is building a new VPC in Prism Central to isolate a test environment. The administrator plans to connect it to an external network later, but they want to complete the initial creation first. Which configuration items are the minimum required to successfully create the VPC?
An administrator is deploying a multi-tier (web, app, database) application on a Nutanix cluster using AHV. The administrator needs to allow internal communication between tiers and provide external access to the web tier. How should the administrator satisfy this requirement?
An administrator plans to upgrade a Nutanix cluster running AHV and Prism Central. The current cluster is on AOS 6.10, and the administrator wants to move to AOS 7.3 while ensuring all components remain compatible. What is the correct upgrade order to minimize downtime and maintain cluster functionality?
An administrator manages a four-node cluster Each node has a 4 available 10GB uplinks, and all four are configured as an Active/Active bundle. They want to use Flow Virtual Networking to provide networking to the VMs in the cluster with the following requirements: VMs should be in a single VPC. VMs should be reachable by their real IP addresses. The VPC should have access to the most north/south bandwidth possible. No changes can be made to the physical infrastructure. How can this best be achieved?
An enterprise has deployed a VPC called FinanceVPC using Nutanix Flow Virtual Networking. The Finance team needs the following connectivity: Internal servers in the VPC must reach an on-premises corporate data-center via a point-to-point encrypted link. Some servers in the VPC must also access the public internet with source NAT and receive inbound access via floating IPs. The corporate network uses overlapping IP space with other VPCs in the environment, so address translation is necessary for those workloads. The networking design must support routing via BGP for future site expansions and provide low-latency north-south connectivity. Which actions should the administrator take to satisfy this requirement?
An administrator creates a new VPC in No NAT mode to allow VMs in a web tier to reach an external firewall. After deployment... none of the VMs can reach external IP addresses... Which action should the administrator take to restore routed north-south connectivity from the VPC?
While configuring a new security policy in a Nutanix microsegmentation environment, an administrator wants the policy to remain flexible even if virtual machines change subnets or obtain new IP addresses. Which configuration approach should the administrator use when defining the policy scope?
Which prerequisite is required before enabling Flow Network Security Next-Gen micro segmentation?
An administrator has created a VPC with the following subnets: 10.1.1.0/24 10.1.2.0/24 10.1.3.0/24 What action must be taken for these networks to be externally routable?
An administrator needs to delegate the management of security policies to a dedicated SecOps team. To enforce the principle of least privilege, the administrator assigns the predefined Flow Policy Author role to a user on the team. The user confirms they can create, monitor, and enforce security policies. However, when attempting to build a new application security policy for a set of newly deployed VMs, the user reports they are unable to create a new category to group these VMs. The option is not available in the Prism Central UI. Which statement explains this behavior?
An administrator is deploying a new multi-tenant environment in Prism Central and has created a VPC named TenantVPC1. The administrator needs to enable external connectivity for this VPC so that some services inside the VPC can be accessed from the corporate network without NAT translation, while other services require Internet access through SNAT translation. The administrator plans to use an External Network(s) to provision this connectivity. Which configuration should the administrator apply to satisfy this requirement?
When configuring an Application policy, an administrator defines a VM Category Application:MySQL as a Secured Entity. The administrator wants to ensure that traffic between VMs in the Secured Entity is kept to only required replication traffic on the default mysql service port. How should the administrator best accomplish this?
An administrator needs to configure a security policy that controls VM-to-VM communication within a category defined as secured entity. Which configuration action should the administrator take to restrict all intra-tier communication between the VMs within a category defined as secured entity?
Before creating a new Application Security Policy in Prism Central, what prerequisite must exist?
An administrator has configured a VPC and associated a NAT external network. A virtual machine connected to a subnet within this VPC is required to be accessible externally. What action must the administrator take to accomplish this?
Refer to Exhibit:
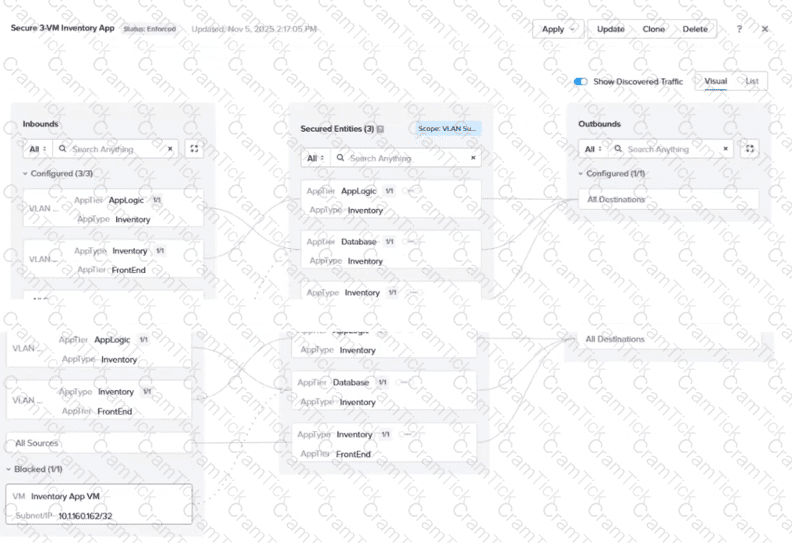
An administrator is reviewing an enforced security policy "Secure 3-VM Inventory App", as shown in the exhibit. The policy's inbound rules are configured to allow traffic from specific sources to each tier of the application. The visualization shows one blocked traffic flow. Based on the information presented in the exhibit, which statement best describes this behavior?
Which policy mode blocks all traffic that is not explicitly allowed by the policy?
When cloning a Flow Network Security policy, what should be verified before enabling Enforce mode?
A customer wants to extend a VLAN subnet to a remote data center using VTEP. The administrator configures a Subnet Extension which shows UP in the Prism Interface, yet traffic fails to pass. Which setting is most likely misconfigured?
A service-insertion firewall VM protects user VMs access to the internet. The virtual and physical switches, as well as all user VMs, currently use the default MTU size of 1500. Everything functions normally until a user VM is migrated to another host. After the migration, the user reports that some websites fail to load while ping to those same sites still succeeds. Routing and security policies appear normal. Which two configuration changes could resolve the issue? (Choose two.)
In Nutanix Flow, which action transitions a security policy from observing traffic to actively enforcing the rules?
An administrator has two user VPCs connected via a Transit VPC. Routing works for most subnets, but one overlay subnet cannot reach external networks. What is the most probable cause?
An administrator must delegate management of a single tenant VPC to a junior engineer. The engineer should be able to modify that VPC but must not see or change any other VPCs or networking configurations in Prism Central. The administrator wants to meet this requirement using RBAC. Which action should the administrator take to meet this requirement?
An administrator recently deployed a new set of virtual machines... 3-tier web application... restricted as follows: Only application VMs can talk to database VMs on port 3306 Frontend VMs should only communicate with application VMs on port 8080 Which action will correctly create and configure the Security Policies in Nutanix Flow to satisfy this task?
NCP-NS |


