Which of the following can be implemented with PAM to detect and block dictionary attacks?
A systems administrator is helping to secure a new web application. During the tests, the administrator obtains the following output to validate the application:
SSL connection using TLSv1.2 / ECDHE-RSA-AES256-GCM-SHA384
ALPN, server accepted to use http/1.1
Server certificate:
subject: CN=*.newapp.comptia.org
start date: Jan 17 00:00:00 2024 GMT
expire date: Feb 16 23:59:59 2034 GMT
issuer: C=US; O=Comptia; OU=IT Security; CN=ca1.comptia.org
SSL certificate verify result: unable to get local issuer certificate (20), continuing anyway.
Which of the following explains the validation results?
A user reports Issues v/hen trying to connect to one ot the Linux servers. The server administrator reviews the following outputs:
Output 1:
Kernel panic not syncing: Fatal Machine check
Fid: 0, comm; swapper Tainted: G M ------------------ 4.18.0-553.8.1.cl8_10.x86_64 #1
Call Trace:
< #mc > [rrrrrrrrs:4er..i4i] ? panic+ox7n/oxi43
[] ? mcc_panic+0x21f/0x240
[] ? do_machine_check+0xal8/0xae0
[] ? intel idie+0xbi/0xi70
[] ? machino_check+0xlc/0x30
[] ? intel_idle+0xbl/0xl70
«EOE» [] ? hrtimer 8tart+0xlB/0x20
[] ? cpuidle_idle_cail+0xa7/0xl40
I| ? cpu_idle+0xbfc/0xll0
[] ? Start_secondary+0x202/0x245
Output 2:
[325926.243631] mce: [Error] : CPU 22: Machine Check Exception: 7 Bank 0: bd80000000000134
1325926.247004| nice: (Error): Machine check events logged
[325991.358038] race: [Error] : KIP 10: < ffffffff83584719* (copy user enhanced fast strir.q+0x9/0x20)
[325991.358038] mce: [Error] : tsc 31ea89256a735 ADDR 3cdl889000 MISC 8c
[325991.350033] mce: [Error] : PROCESSOR 0:50657 TIME 15945B1695 SOCKET 0 APTC 16 microcode rrrrtrrr
[325991.358038] mce: [Error] : Run the above through ' rr.ccloq —ascii*
[325991.358038] mce: [Error] : Machine check: Action required: unknown MCACOD
[325991.3511038] Kernel panic not syncing: Fatal machine check
Which of the following statements describes the cause and resolution for this issue?
A Linux administrator needs to compare two files and provide the output in the following format:
2,3d1
< Line 2
< Line 3
4a3
Line 5
Which of the following commands should the administrator use to perform the task?
Which of the following describes how a user ' s public key is used during SSH authentication?
A small group of remote users needs permission to run some administrative commands on a Linux server. Which of the following approaches is the best way to address this request?
Which of the following commands sets all the directories ' permissions recursively in the user ' s home directory and makes them accessible only to the user?
A systems administrator receives reports from users who are having issues while trying to modify newly created files in a shared directory. The administrator sees the following outputs:
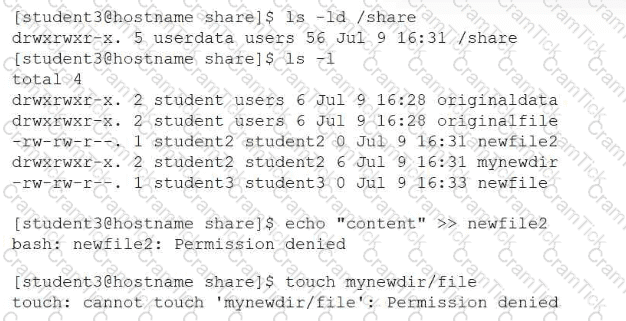
Which of the following provides the best resolution to this issue?
Which of the following is the main reason for setting up password expiry policies?
Which of the following is a reason multiple password changes on the same day are not allowed?
A Linux systems administrator makes updates to systemd-managed service configuration files. Which of the following commands should the administrator execute in order to implement the changes?
A Linux administrator attempts to log in to a server over SSH as root and receives the following error message: Permission denied, please try again. The administrator is able to log in to the console of the server directly with root and confirms the password is correct. The administrator reviews the configuration of the SSH service and gets the following output:
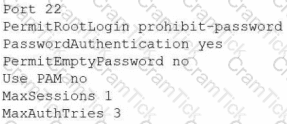
Based on the above output, which of the following will most likely allow the administrator to log in over SSH to the server?
A systems administrator is having issues with a third-party API endpoint. The administrator receives the following output:
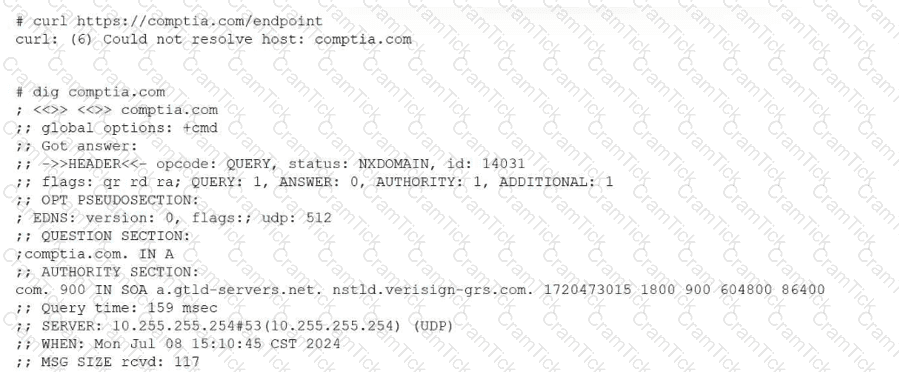
Which of the following actions should the administrator take to resolve the issue?
An administrator needs to remove the directory /home/user1/data and all of its contents. Which of the following commands should the administrator use?
The development team asks a Linux administrator to help diagnose a connectivity issue that is occurring with a newly developed software. The Linux administrator reviews the following output:
$ wget -vvv https://api.newapp.comptia.org/v2/health
Resolving proxy.comptia.org (proxy.comptia.org)... connected.
ERROR: The certificate of ' api.newapp.comptia.org ' is not trusted.
ERROR: The certificate of ' api.newapp.comptia.org ' does not have a known issuer.
Which of the following actions is the best way to resolve the issue?
A systems administrator receives reports about connection issues to a secure web server. Given the following firewall and web server outputs:
Firewall output:
Status: active
To Action From
443/tcp DENY Anywhere
443/tcp (v6) DENY Anywhere (v6)
Web server output:
tcp LISTEN 0 4096 *:443 :
Which of the following commands best resolves this issue?
A user states that an NFS share Is reporting random disconnections. The systems administrator obtains the following information
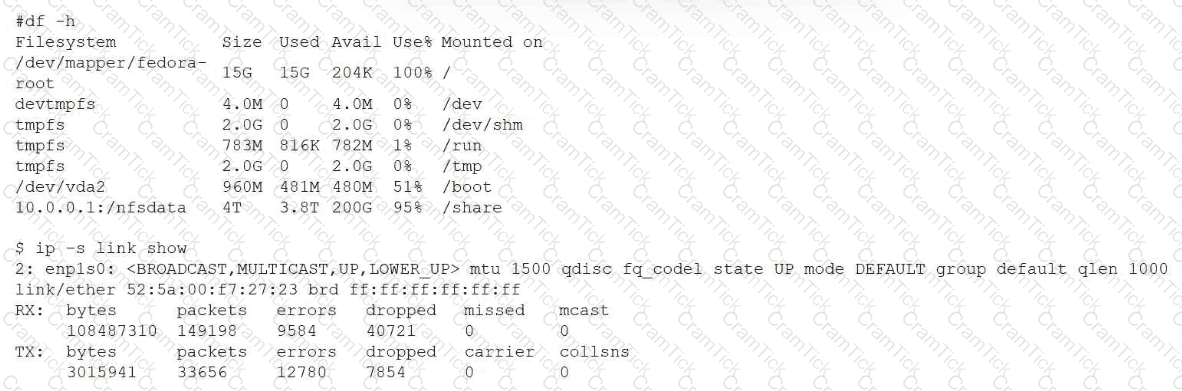
Which of the following best explains the symptoms that are being reported?
A systems administrator is reconfiguring existing user accounts in a Linux system. Which of the following commands should the administrator use to include " myuser " in the finance group?
An administrator wants to start an Ubuntu terminal in a container. Which of the following will allow the administrator to complete the task?
An administrator added a new disk to expand the current storage. Which of the following commands should the administrator run first to add the new disk to the LVM?
A Linux system displays the following error during operation:
Kernel panic - not syncing: Fatal Machine check
Pid: 0, comm: swapper Tainted: G M
Call Trace:
...
mce_panic
do_machine_check
Which of the following is the most likely cause of this issue?
A systems administrator needs to open the DNS TCP port on a Linux system from network 10.0.0.0/24. Which of the following commands should the administrator use for this task?
A Linux user runs the following command:
nohup ping comptia.com &
Which of the following commands should the user execute to attach the process to the current terminal?
A Linux administrator needs to create and then connect to the app-01-image container. Which of the following commands accomplishes this task?
Which of the following Ansible components is used to define groups and individual hosts and can include variables specific to each host or group?
Which of the following describes the method of consolidating system events to a single location?
Users report that a Linux system is unresponsive and simple commands take too long to complete. The Linux administrator logs in to the system and sees the following: Output 1:
10:06:29 up 235 day, 19:23, 2 users, load average: 8.71, 8.24, 7.71
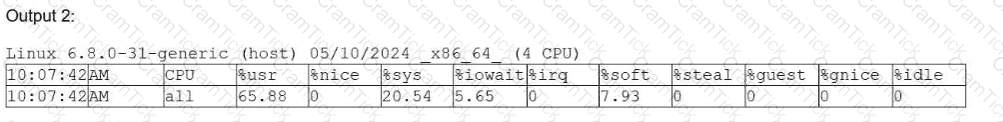
Which of the following is the system experiencing?
A systems administrator troubleshoots a connectivity issue and needs to determine whether port 449 is open locally. Which of the following commands should the administrator use?
An administrator is trying to terminate a process that is not responding. Which of the following commands should the administrator use in order to force the termination of the process?
A systems administrator wants to review the logs from an Apache 2 error.log file in real time and save the information to another file for later review. Which of the following commands should the administrator use?
A Linux administrator needs to add a new HTTP service on the server. Which of the following commands allows other systems to communicate with the service after the system is restarted?
A Linux user needs to download the latest Debian image from a Docker repository. Which of the following commands makes this task possible?
Which of the following commands is used to ensure a service starts automatically at boot on a system using systemd?
A Linux administrator installed a new program inside $HOME/.local/bin and is trying to execute it without using an absolute path. Which of the following should the administrator use for this task?
Which of the following commands should an administrator use to convert a KVM disk file to a different format?
A Linux systems administrator is running an important maintenance task that consumes a large amount of CPU, causing other applications to slow. Which of the following actions should the administrator take to help alleviate the issue?
A Linux administrator needs to create accounts for a list of new users. The user account names have been defined in the USER_LIST variable by executing the following:
USER_LIST= " alice bob charles "
Which of the following commands should the administrator use to successfully create the user accounts?
Which of the following best describes a use case for playbooks in a Linux system?
Which of the following is the location for built-in Linux executable files and utilities?
Due to application compatibility issues, the Python 3 OpenSSL library should not be upgraded. Which of the following commands should the systems administrator use to ensure the package stays at the current version?
Linux+ |