What is the reason for the “reject_size” action shown in the message processing result?
You are using Smart Search within the PPS Admin UI to investigate the final disposition of a message. Smart Search shows the message is Quarantined/Discard to adqueue. How do you trace the message?
What is the purpose of roles when assigning administrative access to Proofpoint Protection Server?
Pick the 2 correct responses below.
You log into the Protection Server and a rule you created yesterday is no longer enabled. Where can you find out what happened to the rule you created?
Which application do you use to update the SSO configuration for Federated Authentication for your Proofpoint Cloud Services, including TAP, Cloud Admin, and NPRE?
Smart Search has returned 13 results for a specific recipient address. You click on one of the messages in the Results list. Which of the following information is available for that message?
If an email is incorrectly filtered as spam, what should an administrator do first when reviewing the filter logs?
Review the filter log exhibit.
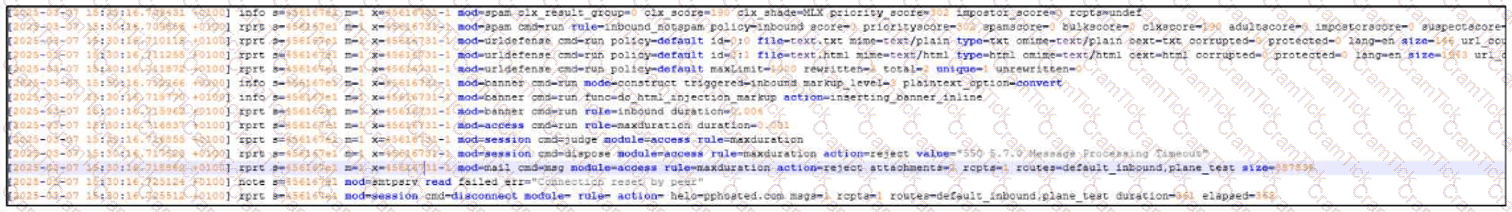
What two actions have taken place in the filter logs for this message?
What the exhibit shows clearly:
- URL Defense processing is present in the log
- A spam-related action/flag is present
When accessing Threat Response/TRAP, you are unable to edit workflows. What is the first thing you should do?
Which of the following are true regarding Spam Detection?
Pick the 3 correct responses below.
If one of your corporate email accounts is sending excessive outbound emails, the Outbound Throttle feature can help. Which of the following is true regarding Outbound Throttle?
What are the three default methods available in Recipient Verification to verify that a recipient mailbox exists?
Pick the 3 correct responses below.
You are configuring Proofpoint’s URL Rewrite feature for incoming emails. What is the primary purpose of this feature?
An inbound message matches the inbound_protected policy route and also the default spam policy. Which policy will be applied?


