Which of the following is the core component of an operating system that manages resources, implements security policies, and provides the interface between hardware and software?
What is the GREATEST security concern associated with virtual (nation technology?
A penetration tester has been hired and given access to all code, diagrams,and documentation. Which type oftesting is being conducted?
Analyze the file titled pcap_artifact5.txt on the AnalystDesktop.
Decode the contents of the file and save the output in atext file with a filename of pcap_artifact5_decoded.txton the Analyst Desktop.
Your enterprise SIEM system is configured to collect andanalyze log data from various sources. Beginning at12:00 AM on December 4, 2024, until 1:00 AM(Absolute), several instances of PowerShell arediscovered executing malicious commands andaccessing systems outside of their normal workinghours.
What is the physical address of the web server that wastargeted with malicious PowerShell commands?
Which of the following is a security feature provided by the WS-Security extension in the Simple Object Access Protocol (SOAP)?
Analyze the file titled pcap_artifact5.txt on the AnalystDesktop.
Decode the C2 host of the attack. Enter your responsebelow.
The enterprise is reviewing its security posture byreviewing unencrypted web traffic in the SIEM.
How many logs are associated with well knownunencrypted web traffic for the month of December2023 (Absolute)? Note: Security Onion refers to logsas documents.
Which of the following security practices is MOST effective in reducing system risk through system hardening?
On the Analyst Desktop is a Malware Samples folderwith a file titled Malscript.viruz.txt.
What is the name of the service that the malware attempts to install?
The network team has provided a PCAP file withsuspicious activity located in the Investigations folderon the Desktop titled, investigation22.pcap.
What is the filename of the webshell used to control thehost 10.10.44.200? Your response must include the fileextension.
Before performing a penetration test for a client, it is MOST crucial to ensure:
In which phase of the Cyber Kill Chain" would a red team run a network and port scan with Nmap?
Which type of security model leverages the use of data science and machine learning (ML) to further enhance threat intelligence?
Which of the following cyber crime tactics involves targets being contacted via text message by an attacker posing as a legitimate entity?
Your enterprise has received an alert bulletin fromnational authorities that the network has beencompromised at approximately 11:00 PM (Absolute) onAugust 19, 2024. The alert is located in the alerts folderwith filename, alert_33.pdf.
Use the IOCs to find the compromised host. Enter thehost name identified in the keyword agent.name fieldbelow.
An employee has been terminated for policy violations.Security logs from win-webserver01 have been collectedand located in the Investigations folder on theDesktop as win-webserver01_logs.zip.
Generate a SHA256 digest of the System-logs.evtx filewithin the win-webserver01_logs.zip file and providethe output below.
Which of the following is the PRIMARY benefit of implementing logical access controls on a need-to-know basis?
Which of the following is the PRIMARY benefit of using software-defined networking for network security?
Which of the following should be considered FIRST when determining how to protect an organization's information assets?
Following a ransomware incident, the network teamprovided a PCAP file, titled ransom.pcap, located in theInvestigations folder on the Desktop.
What is the full User-Agent value associated with theransomware demand file download. Enter your responsein the field below.
Which of the following is the MOST common output of a vulnerability assessment?
The user of the Accounting workstation reported thattheir calculator repeatedly opens without their input.
Perform a query of startup items for the agent.nameaccounting-pc in the SIEM for the last 24 hours. Identifythe file name that triggered RuleName SuspiciousPowerShell. Enter your response below. Your responsemust include the file extension.
On the Analyst Desktop is a Malware Samples folderwith a file titled Malscript.viruz.txt.
Based on the contents of the malscript.viruz.txt, whichthreat actor group is the malware associated with?
For this question you must log into GreenboneVulnerability Manager using Firefox. The URL is:https://10.10.55.4:9392 and credentials are:
Username:admin
Password:Secure-gvm!
A colleague performed a vulnerability scan but did notreview prior to leaving for a family emergency. It hasbeen determined that a threat actor is using CVE-2021-22145 in the wild. What is the host IP of the machinethat is vulnerable to this CVE?
The CISO has received a bulletin from law enforcementauthorities warning that the enterprise may be at risk ofattack from a specific threat actor. Review the bulletin
named CCOA Threat Bulletin.pdf on the Desktop.
Which of the following domain name(s) from the CCOAThreat Bulletin.pdf was contacted between 12:10 AMto 12:12 AM (Absolute) on August 17, 2024?
Cyber Analyst Password:
For questions that require use of the SIEM, pleasereference the information below:
https://10.10.55.2
Security-Analyst!
CYB3R-4n4ly$t!
Email Address:
ccoatest@isaca.org
Password:Security-Analyst!
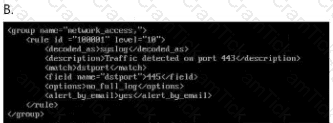
The enterprise has been receiving a large amount offalse positive alerts for the eternalblue vulnerability. TheSIEM rulesets are located in
/home/administrator/hids/ruleset/rules.
What is the name of the file containing the ruleset foreternalblue connections? Your response must includethe file extension.
A bank employee is found to beexfiltrationsensitive information by uploading it via email. Which of the following security measures would be MOST effective in detecting this type of insider threat?
Which of the following is the MOST effective approach for tracking vulnerabilities in an organization's systems and applications?
The network team has provided a PCAP file withsuspicious activity located in the Investigations folderon the Desktop titled, investigation22.pcap.
What date was the webshell accessed? Enter the formatas YYYY-MM-DD.
The user of the Accounting workstation reported thattheir calculator repeatedly opens without their input.
The following credentials are used for thisquestion.
Username:Accounting
Password:1x-4cc0unt1NG-x1
Using the provided credentials, SSH to the Accountingworkstation and generate a SHA256 checksum of the filethat triggered RuleName Suspicious PowerShell usingeither certutil or Get-FileHash of the file causing theissue. Copy the hash and paste it below.
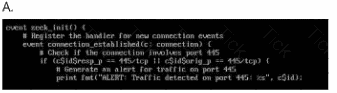
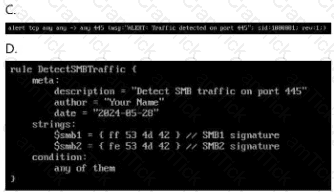
Which ruleset can be applied in the
/home/administrator/hids/ruleset/rules directory?
Double-click each image to view it larger.
The enterprise is reviewing its security posture byreviewing unencrypted web traffic in the SIEM.
How many unique IPs have received well knownunencrypted web connections from the beginning of2022 to the end of 2023 (Absolute)?
Your enterprise has received an alert bulletin fromnational authorities that the network has beencompromised at approximately 11:00 PM (Absolute) onAugust 19, 2024. The alert is located in the alerts folderwith filename, alert_33.pdf.
What is the name of the suspected malicious filecaptured by keyword process.executable at 11:04 PM?


