Which of the following is MOST important to consider when determining key performance indicators (KPIs) for a process?
Which of the following is the GREATEST concern associated with the use of artificial intelligence (AI) language models?
Which organization is implementing a project to automate the purchasing process, including the modification of approval controls. Which of the following tasks is lie responsibility of the risk practitioner*?
Which of the following is MOST important to address for an organization looking to improve its IT asset management processes?
Which of the following is the MOST important consideration when prioritizing risk response?
Which of the following would MOST effectively reduce the potential for inappropriate exposure of vulnerabilities documented in an organization ' s risk register?
Which of the following controls are BEST strengthened by a clear organizational code of ethics?
During a post-implementation review for a new system, users voiced concerns about missing functionality. Which of the following is the BEST way for the organization to avoid this situation in the future?
A zero-day vulnerability has been discovered in a globally used brand of hardware server that allows hackers to gain
access to affected IT systems. Which of the following is MOST likely to change as a result of this situation?
Digital signatures are an effective control method for information exchange over an insecure network because they:
Which of the following is the BEST way to assess the effectiveness of an access management process?
When defining thresholds for control key performance indicators (KPIs). it is MOST helpful to align:
Which of the following is MOST important information to review when developing plans for using emerging technologies?
A risk practitioner is organizing risk awareness training for senior management. Which of the following is the MOST important topic to cover in the training session?
Where should a risk practitioner document the current state and desired future state of organizational risk?
Which of the following should be of MOST concern to a risk practitioner reviewing an organization risk register after the completion of a series of risk assessments?
An organization plans to implement a new Software as a Service (SaaS) speech-to-text solution Which of the following is MOST important to mitigate risk associated with data privacy?
An organization is planning to engage a cloud-based service provider for some of its data-intensive business processes. Which of the following is MOST important to help define the IT risk associated with this outsourcing activity?
An organization wants to grant remote access to a system containing sensitive data to an overseas third party. Which of the following should be of GREATEST concern to management?
Which of the following is the MOST important data attribute of key risk indicators (KRIs)?
An application development team has a backlog of user requirements for a new system that will process insurance claim payments for customers. Which of the following should be the MOST important consideration for a risk-based review of the user requirements?
Participants in a risk workshop have become focused on the financial cost to mitigate risk rather than choosing the most appropriate response. Which of the following is the BEST way to address this type of issue in the long term?
A control owner responsible for the access management process has developed a machine learning model to automatically identify excessive access privileges. What is the risk practitioner ' s BEST course of action?
An IT risk practitioner has been tasked to engage key stakeholders to assess risk for key IT risk scenarios. Which of the following is the PRIMARY benefit of this activity?
Senior management has requested a risk practitioner ' s guidance on whether
a new technical control requested by a business unit is worth the investment.
Which of the following should be the MOST important consideration before
providing input?
What is the BEST course of action when the business impact of a risk event is rated high, but the likelihood of risk materialization has decreased?
Which of the following is the MOST important key performance indicator (KPI) to establish in the service level agreement (SLA) for an outsourced data center?
A new policy has been published to forbid copying of data onto removable media. Which type of control has been implemented?
A business manager wants to leverage an existing approved vendor solution from another area within the organization. Which of the following is the risk practitioner ' s BEST course of action?
Which of the following is the GREATEST benefit when enterprise risk management (ERM) provides oversight of IT risk management?
Which of the following provides the MOST useful information when measuring the progress of risk response action plans?
Which of the following would provide the BEST guidance when selecting an appropriate risk treatment plan?
Which of the following is the PRIMARY reason for logging in a production database environment?
A service organization is preparing to adopt an IT control framework to comply with the contractual requirements of a new client. Which of the following would be MOST helpful to the risk practitioner?
Which of the following would BEST enable a risk-based decision when considering the use of an emerging technology for data processing?
After migrating a key financial system to a new provider, it was discovered that a developer could gain access to the production environment. Which of the following is the BEST way to mitigate the risk in this situation?
A penetration test reveals several vulnerabilities in a web-facing application. Which of the following should be the FIRST step in selecting a risk response?
An organization has allowed several employees to retire early in order to avoid layoffs Many of these employees have been subject matter experts for critical assets Which type of risk is MOST likely to materialize?
The MOST important reason to monitor key risk indicators (KRIs) is to help management:
Which of the following is the PRIMARY purpose of periodically reviewing an organization ' s risk profile?
Which of the following is MOST helpful in verifying that the implementation of a risk mitigation control has been completed as intended?
During a recent security framework review, it was discovered that the marketing department implemented a non-fungible token asset program. This was done without following established risk procedures. Which of the following should the risk practitioner do FIRST?
When presenting risk, the BEST method to ensure that the risk is measurable against the organization ' s risk appetite is through the use of a:
An IT organization is replacing the customer relationship management (CRM) system. Who should own the risk associated with customer data leakage caused by insufficient IT security controls for the new system?
Which of the following is the PRIMARY reason for a risk practitioner to use global standards related to risk management?
When of the following standard operating procedure (SOP) statements BEST illustrates appropriate risk register maintenance?
Which of the following is the PRIMARY objective of providing an aggregated view of IT risk to business management?
Which of the following provides The MOST useful information when determining a risk management program ' s maturity level?
Which of the following will BEST ensure that controls adequately support business goals and objectives?
Which of the following is MOST important to determine when assessing the potential risk exposure of a loss event involving personal data?
From a risk management perspective, which of the following is the PRIMARY purpose of conducting a root cause analysis following an incident?
Which of the following is the GREATEST impact of implementing a risk mitigation strategy?
When reviewing a report on the performance of control processes, it is MOST important to verify whether the:
Which of the following is the ULTIMATE goal of conducting a privacy impact analysis (PIA)?
The BEST key performance indicator (KPI) to measure the effectiveness of a vendor risk management program is the percentage of:
Which of the following activities is PRIMARILY the responsibility of senior management?
A risk practitioner shares the results of a vulnerability assessment for a critical business application with the business manager. Which of the following is the NEXT step?
Which of the following is the BEST approach for selecting controls to minimize risk?
When creating a program to manage data privacy risk, which of the following is MOST important to ensure that the program is successful?
Which types of controls are BEST used to minimize the risk associated with a vulnerability?
Which of the following is the PRIMARY benefit of integrating risk and security requirements in an organization ' s enterprise architecture (EA)?
Which of the following is the MOST relevant information to include in a risk management strategy?
What are the MOST important criteria to consider when developing a data classification scheme to facilitate risk assessment and the prioritization of risk mitigation activities?
Which of the following BEST enables an organization to determine whether risk management is aligned with its goals and objectives?
The PRIMARY reason for tracking the status of risk mitigation plans is to ensure:
During a risk assessment, what should an assessor do after identifying threats to organizational assets?
An organization’s board of directors is concerned about recent data breaches in the news and wants to assess its exposure to similar scenarios. Which of the following is the BEST course of action?
An organization automatically approves exceptions to security policies on a recurring basis. This practice is MOST likely the result of:
Which key performance indicator (KPI) BEST measures the effectiveness of an organization ' s disaster recovery program?
An organization has experienced a cyber-attack that exposed customer personally identifiable information (Pll) and caused extended outages of network services. Which of the following stakeholders are MOST important to include in the cyber response team to determine response actions?
Who should be accountable for monitoring the control environment to ensure controls are effective?
An organization has outsourced a critical process involving highly regulated data to a third party with servers located in a foreign country. Who is accountable for the confidentiality of this data?
What is the BEST information to present to business control owners when justifying costs related to controls?
Which of the following provides the MOST useful information when developing a risk profile for management approval?
An organization is implementing Internet of Things (IoT) technology to control temperature and lighting in its headquarters. Which of the following should be of GREATEST concern?
Which of the following would be the result of a significant increase in the motivation of a malicious threat actor?
Management has noticed storage costs have increased exponentially over the last 10 years because most users do not delete their emails. Which of the following can BEST alleviate this issue while not sacrificing security?
A risk practitioner has observed that risk owners have approved a high number of exceptions to the information security policy. Which of the following should be the risk practitioner ' s GREATEST concern?
The PRIMARY objective of collecting information and reviewing documentation when performing periodic risk analysis should be to:
Which of the following is MOST likely to be identified from an information systems audit report?
An organization is developing a plan to address new information security risks emerging from business changes. Which of the following BEST enables stakeholders to make decisions impacting organizational strategy?
Which of the following would be the BEST key performance indicator (KPI) for monitoring the effectiveness of the IT asset management process?
Which of the following should a risk practitioner do NEXT after learning that Internet of Things (IoT) devices installed in the production environment lack appropriate security controls for sensitive data?
Which of the following is MOST important when considering risk in an enterprise risk management (ERM) process?
Which of the following is the MOST important reason to restrict access to the risk register on a need-to-know basis?
Which of the following is the BEST method to ensure a terminated employee ' s access to IT systems is revoked upon departure from the organization?
Which of the following is the PRIMARY advantage of aligning generic risk scenarios with business objectives?
An organization’s expense claim system allows users to split large transactions into smaller ones to bypass limits. What should the risk practitioner do?
An organization moved its payroll system to a Software as a Service (SaaS) application. A new data privacy regulation stipulates that data can only be processed within the countrywhere it is collected. Which of the following should be done FIRST when addressing this situation?
Which of the following would BEST mitigate the risk associated with reputational damage from inappropriate use of social media sites by employees?
Which of the following elements of a risk register is MOST likely to change as a result of change in management ' s risk appetite?
A risk practitioner is MOST likely to use a SWOT analysis to assist with which risk process?
Which of the following emerging technologies is frequently used for botnet distributed denial of service (DDoS) attacks?
An organization has used generic risk scenarios to populate its risk register. Which of the following presents the GREATEST challenge to assigning of the associated risk entries?
During a control review, the control owner states that an existing control has deteriorated over time. What is the BEST recommendation to the control owner?
Which of the following provides the BEST assurance of the effectiveness of vendor security controls?
Which of the following is the MOST important objective of establishing an enterprise risk management (ERM) function within an organization?
The BEST way to test the operational effectiveness of a data backup procedure is to:
A risk practitioner is reviewing the status of an action plan to mitigate an emerging IT risk and finds the risk level has increased. The BEST course of action would be to:
Which of the following BEST informs decision-makers about the value of a notice and consent control for the collection of personal information?
Which of the following provides the MOST useful information for developing key risk indicators (KRIs)?
An organization has updated its acceptable use policy to mitigate the risk of employees disclosing confidential information. Which of the following is the BEST way to reinforce the effectiveness of this policy?
Which of the following would MOST effectively reduce risk associated with an increase of online transactions on a retailer website?
Which of the following is MOST important to consider when determining a recovery time objective (RTO)?
An organization ' s Internet-facing server was successfully attacked because the server did not have the latest security patches. The risk associated with poor patch management had been documented in the risk register and accepted. Who should be accountable for any related losses to the organization?
A risk practitioner is performing a risk assessment of recent external advancements in quantum computing. Which of the following would pose the GREATEST concern for the risk practitioner?
Which of the following is MOST important when developing key performance indicators (KPIs)?
Which of the following would offer the MOST insight with regard to an organization ' s risk culture?
During an IT risk scenario review session, business executives question why they have been assigned ownership of IT-related risk scenarios. They feel IT risk is technical in nature and therefore should be owned by IT. Which of the following is the BEST way for the risk practitioner to address these concerns?
An organization does not have a defined process to revoke IT access of staff members who have changed roles within the organization. Which of the following is the GREATEST concern associated with this deficiency?
Which of the following controls would BEST reduce the risk of account compromise?
Which of the following will MOST improve stakeholders ' understanding of the effect of a potential threat?
Which of the following is the MOST effective control to ensure user access is maintained on a least-privilege basis?
A PRIMARY advantage of involving business management in evaluating and managing risk is that management:
Which of the following would be of GREATEST assistance when justifying investment in risk response strategies?
Which of the following would BEST support the integrity of online financial transactions?
The MOST essential content to include in an IT risk awareness program is how to:
Which of the following is MOST important to the effectiveness of key performance indicators (KPIs)?
Which strategy employed by risk management would BEST help to prevent internal fraud?
External auditors have found that management has not effectively monitored key security technologies that support regulatory objectives. Which type of indicator would BEST enable the organization to identify and correct this situation?
After identifying new risk events during a project, the project manager s NEXT step should be to:
Which of the following is the PRIMARY risk management responsibility of the second line in the three lines model?
A risk practitioner is reviewing accountability assignments for data risk in the risk register. Which of the following would pose the GREATEST concern?
Which of the following is MOST important for an organization to update following a change in legislation requiring notification to individuals impacted by data breaches?
Which of the following should be the risk practitioner s FIRST course of action when an organization has decided to expand into new product areas?
Which of the following BEST indicates the effective implementation of a risk treatment plan?
Which of the following is MOST important to ensure when reviewing an organization ' s risk register?
Which of the following is the MOST effective way to mitigate identified risk scenarios?
What is the PRIMARY reason to periodically review key performance indicators (KPIs)?
A large organization needs to report risk at all levels for a new centralized visualization project to reduce cost and improve performance. Which of the following would MOST effectively represent the overall risk of the project to senior management?
An organization has decided to use an external auditor to review the control environment of an outsourced service provider. The BEST control criteria to evaluate the provider would be based on:
Which of the following is the MOST significant benefit of using quantitative risk analysis instead of qualitative risk analysis?
A risk practitioner ' s BEST guidance to help an organization develop relevant risk scenarios is to ensure the scenarios are:
Which of the following presents the GREATEST privacy risk related to personal data processing for a global organization?
When a high number of approved exceptions are observed during a review of a control procedure, an organization should FIRST initiate a review of the:
Which of the following would require updates to an organization ' s IT risk register?
Which of the following should be the PRIMARY consideration when assessing the automation of control monitoring?
Which of the following is MOST important to consider when determining the risk associated with re-identification of obfuscated personal data?
When preparing a risk status report for periodic review by senior management, it is MOST important to ensure the report includes
Which of the following BEST reduces the likelihood of fraudulent activity that occurs through use of a digital wallet?
Which of the following is the GREATEST concern when an organization uses a managed security service provider as a firewall administrator?
A business is conducting a proof of concept on a vendor ' s Al technology. Which of the following is the MOST important consideration for managing risk?
Which of the following is the MOST important course of action to foster an ethical, risk-aware culture?
Which of the following requirements is MOST important to include in an outsourcing contract to help ensure sensitive data stored with a service provider is secure?
Which of the following is the BEST way to incorporate continuous monitoring in IT risk policies?
Which of the following statements BEST illustrates the relationship between key performance indicators (KPIs) and key control indicators (KCIs)?
Which of the following BEST enables the timely detection of changes in the security control environment?
A recent risk workshop has identified risk owners and responses for newly identified risk scenarios. Which of the following should be the risk practitioner s NEXT step? r
An organization plans to migrate sensitive information to a public cloud infrastructure. Which of the following is the GREATEST security risk in this scenario?
Which of the following is MOST appropriate to prevent unauthorized retrieval of confidential information stored in a business application system?
Which of the following is the MOST appropriate action when a tolerance threshold is exceeded?
Which of the following is the MOST important characteristic of an effective risk management program?
Implementing which of the following controls would BEST reduce the impact of a vulnerability that has been exploited?
During the control evaluation phase of a risk assessment, it is noted that multiple controls are ineffective. Which of the following should be the risk practitioner ' s FIRST course of action?
Which of the following is the MOST important for an organization to have in place to ensure IT asset protection?
Which of the following is a drawback in the use of quantitative risk analysis?
Which of the following will be the GREATEST concern when assessing the risk profile of an organization?
Which of the following is a risk practitioner ' s BEST course of action after identifying risk scenarios related to noncompliance with new industry regulations?
Recent changes in an organization ' s business strategy requires an application to increase its recovery point objective (RPO). Which of the following MUST be updated?
Which of the following BEST indicates that an organizations risk management program is effective?
The implementation of a risk treatment plan will exceed the resources originally allocated for the risk response. Which of the following should be the risk owner ' s NEXT action?
Which of the following BEST enables an organization to address risk associated with technical complexity?
An organization mandates the escalation of a service ticket when a key application is offline for 5 minutes or more due to potential risk exposure. The risk practitioner has been asked by management to prepare a report of application offline times using both 3- and 5-minute thresholds. What does the 3-minute threshold represent?
Which of the following would be MOST beneficial as a key risk indicator (KRI)?
Which of the following is the FIRST step when identifying risk items related to a new IT project?
Which of the following is MOST helpful in identifying loss magnitude during risk analysis of a new system?
Which of the following is MOST likely to cause a key risk indicator (KRI) to exceed thresholds?
Which of the following is the MOST important reason to integrate IT risk management practices into the enterprise-wide operational risk management framework?
A recently purchased IT application does not meet project requirements. Of the following, who is accountable for the potential impact?
Which of the following should be the PRIMARY consideration when prioritizing limited resources needed to implement overdue corrective actions arising from a recent internal audit?
Establishing and organizational code of conduct is an example of which type of control?
Reviewing results from which of the following is the BEST way to identify information systems control deficiencies?
Which of the following is the FIRST step when conducting a business impact analysis (BIA)?
Which of the following data would be used when performing a business impact analysis (BIA)?
An organization recently experienced a cyber attack that resulted in the loss of confidential customer data. Which of the following is the risk practitioner ' s BEST recommendation after recovery steps have been completed?
An organization is subject to a new regulation that requires nearly real-time recovery of its services following a disruption. Which of the following is the BEST way to manage the risk in this situation?
IT management has asked for a consolidated view into the organization ' s risk profile to enable project prioritization and resource allocation. Which of the following materials would
be MOST helpful?
When creating a separate IT risk register for a large organization, which of the following is MOST important to consider with regard to the existing corporate risk ' register?
A risk practitioner has been asked to advise management on developing a log collection and correlation strategy. Which of the following should be the MOST important consideration when developing this strategy?
Which of the following provides the BEST evidence that robust risk management practices are in place within an organization?
Which of the following risk scenarios would be the GREATEST concern as a result of a single sign-on implementation?
Which of the following should be the PRIMARY focus of a disaster recovery management (DRM) framework and related processes?
The BEST key performance indicator (KPI) to measure the effectiveness of a vulnerability remediation program is the number of:
Which of the following is the MOST important consideration when identifying stakeholders to review risk scenarios developed by a risk analyst? The reviewers are:
Which of the following is the FIRST step when developing a business case to drive the adoption of a risk remediation project by senior management?
Which of the following is the BEST indication of an enhanced risk-aware culture?
Which of the following is the PRIMARY reason to have the risk management process reviewed by a third party?
Following the implementation of an Internet of Things (loT) solution, a risk practitioner identifies new risk factors with impact to existing controls. Which of the following is MOST important to include in a report to stakeholders?
Which of these documents is MOST important to request from a cloud service
provider during a vendor risk assessment?
Which of the following information is MOST useful to a risk practitioner for developing IT risk scenarios?
Which of the following should be the PRIMARY driver for an organization on a multi-year cloud implementation to publish a cloud security policy?
Which of the following is the PRIMARY reason to conduct risk assessments at periodic intervals?
Which of the following would be MOST helpful in assessing the risk associated with data loss due to human vulnerabilities?
Which of the following is the PRIMARY reason that risk management is important in project management?
Which of the following BEST mitigates the risk of violating privacy laws when transferring personal information lo a supplier?
Which of the following will BEST help to ensure that information system controls are effective?
What would be a risk practitioner ' s BEST recommendation when several key performance indicators (KPIs) for a control process fail to meet service level agreements (SLAs)?
Which of the following is MOST helpful in aligning IT risk with business objectives?
Which of the following is the MOST likely reason an organization would engage an independent reviewer to assess its IT risk management program?
Which of the following is the MOST important consideration when selecting digital signature software?
Which of the following would be of GREATEST concern regarding an organization ' s asset management?
Which of the following is the PRIMARY reason for sharing risk assessment reports with senior stakeholders?
Which of the following BEST helps to identify significant events that could impact an organization?
Which of the following is MOST important for a multinational organization to consider when developing its security policies and standards?
Which of the following provides the MOST useful information when determining if a specific control should be implemented?
Which of the following is the MOST important factor affecting risk management in an organization?
Which of the following is the MOST important factor to consider when determining whether to approve a policy exception request?
An organization is increasingly concerned about loss of sensitive data and asks the risk practitioner to assess the current risk level. Which of the following should the risk practitioner do FIRST?
Which of the following is the MOST important reason for a risk practitioner to identify stakeholders for each IT risk scenario?
Which of the following is the MOST efficient method for monitoring control effectiveness?
Which of the following would BEST enable mitigation of newly identified risk factors related to internet of Things (loT)?
Which of the following is the BEST control to detect an advanced persistent threat (APT)?
A large organization is replacing its enterprise resource planning (ERP) system and has decided not to deploy the payroll module of the new system. Instead, the current payroll system will continue to be
used. Of the following, who should own the risk if the ERP and payroll system fail to operate as expected?
Which of the following management actions will MOST likely change the likelihood rating of a risk scenario related to remote network access?
During an acquisition, which of the following would provide the MOST useful input to the parent company ' s risk practitioner when developing risk scenarios for the post-acquisition phase?
Which of the following is the BEST way to maintain a current list of organizational risk scenarios?
An organization has decided to implement an emerging technology and incorporate the new capabilities into its strategic business plan. Business operations for the technology will be outsourced. What will be the risk practitioner ' s PRIMARY role during the change?
The MOST important reason for implementing change control procedures is to ensure:
Which of the following functions independently reviews and provides feedback regarding the achievement of organizational objectives?
A new regulator/ requirement imposes severe fines for data leakage involving customers ' personally identifiable information (Pll). The risk practitioner has recommended avoiding the risk. Which of the following actions would BEST align with this recommendation?
A newly incorporated enterprise needs to secure its information assets From a governance perspective which of the following should be done FIRST?
A risk practitioner can use an organization ' s problem management process to anticipate potential risk within IT systems by:
Which of the following is the MOST important topic to cover in a risk awareness training program for all staff?
What should be the PRIMARY objective of updating a risk awareness program in response to a steady rise in cybersecurity threats across the industry?
Which of the following BEST helps to mitigate risk associated with excessive access by authorized users?
An organization has engaged a third party to provide an Internet gateway encryption service that protects sensitive data uploaded to a cloud service. This is an example of risk:
Who is accountable for authorizing application access in a cloud Software as a Service (SaaS) solution?
During an organization ' s simulated phishing email campaign, which of the following is the BEST indicator of a mature security awareness program?
Which of the following is the MOST effective way to integrate business risk management with IT operations?
Within the three lines of defense model, the accountability for the system of internal control resides with:
A risk practitioner has been asked to assess the risk associated with a new critical application used by a financial process team that the risk practitioner was a member of two years ago. Which of the following is the GREATEST concern with this request?
Which of the following is the PRIMARY function of the first line in the three lines model?
Which of the following is the MAIN reason for documenting the performance of controls?
During an internal IT audit, an active network account belonging to a former employee was identified. Which of the following is the BEST way to prevent future occurrences?
An IT operations team implements disaster recovery controls based on decisions from application owners regarding the level of resiliency needed. Who is the risk owner in this scenario?
Which of the following is the MOST important consideration when establishing a recovery point objective (RPO)?
Which of the following is the BEST recommendation when a key risk indicator (KRI) is generating an excessive volume of events?
An organization is participating in an industry benchmarking study that involves providing customer transaction records for analysis Which of the following is the MOST important control to ensure the privacy of customer information?
Which of the following will BEST help in communicating strategic risk priorities?
Which of the following is the GREATEST concern if user acceptance testing (UAT) is not conducted when implementing a new application?
Which of the following is the MOST important reason for a risk practitioner to continuously monitor a critical security transformation program?
The PRIMARY reason for establishing various Threshold levels for a set of key risk indicators (KRIs) is to:
Which of the following should be of GREATEST concern to a risk practitioner when determining the effectiveness of IT controls?
Which of the following is a risk practitioner ' s MOST important action to reduce the likelihood of internal fraud?
Which of the following is the MOST important consideration when selecting key risk indicators (KRIs) to monitor risk trends over time?
Which of the following BEST supports the management of identified risk scenarios?
Which of the following is the GREATEST benefit of incorporating IT risk scenarios into the corporate risk register?
Which of the following is the BEST key performance indicator (KPI) to measure the effectiveness of an antivirus program?
An organization plans to provide specific cloud security training for the IT team to help manage risks associated with cloud technology. This response is considered risk:
During testing, a risk practitioner finds the IT department ' s recovery time objective (RTO) for a key system does not align with the enterprise ' s business continuity plan (BCP). Which of the following should be done NEXT?
Which of the following is MOST important for a project steering committee to consider when deciding to release a new system into production?
Which of the following is MOST critical to the design of relevant risk scenarios?
Which of the following provides the MOST up-to-date information about the effectiveness of an organization ' s overall IT control environment?
Which of the following is the BEST method for assessing control effectiveness?
Which of the following is the MAIN benefit to an organization using key risk indicators (KRIs)?
Which of the following is the MOST important reason for an organization to regularly assess the design of key risk indicators (KRIs)?
Which of the following scenarios presents the GREATEST risk for a global organization when implementing a data classification policy?
A risk practitioner observed Vial a high number of pokey exceptions were approved by senior management. Which of the following is the risk practitioner’s BEST course of action to determine root cause?
Which of the following is MOST helpful when determining whether a system security control is effective?
Which of the following is the BEST course of action for a system administrator who suspects a colleague may be intentionally weakening a system ' s validation controls in order to pass through fraudulent transactions?
Which of the following is the PRIMARY reason to use key control indicators (KCIs) to evaluate control operating effectiveness?
Which of the following could BEST detect an in-house developer inserting malicious functions into a web-based application?
Which of the following is MOST important to consider when determining the value of an asset during the risk identification process?
The risk to an organization ' s reputation due to a recent cybersecurity breach is PRIMARILY considered to be:
Which of the following BEST enables risk mitigation associated with software licensing noncompliance?
Which of the following should be the PRIMARY area of focus when reporting changes to an organization ' s risk profile to executive management?
Which of the following is the BEST way to determine the ongoing efficiency of control processes?
Which of the following BEST facilitates the identification of appropriate key performance indicators (KPIs) for a risk management program?
Winch of the following key control indicators (KCIs) BEST indicates whether security requirements are identified and managed throughout a project He cycle?
An organization has decided to commit to a business activity with the knowledge that the risk exposure is higher than the risk appetite. Which of the following is the risk practitioner ' s MOST important action related to this decision?
Which of the following is the BEST indication that key risk indicators (KRls) should be revised?
Which of the following is an IT business owner ' s BEST course of action following an unexpected increase in emergency changes?
A risk practitioner learns that the organization s industry is experiencing a trend of rising security incidents. Which of the following is the BEST course of action?
Which of the following is MOST important for developing effective key risk indicators (KRIs)?
The effectiveness of a control has decreased. What is the MOST likely effect on the associated risk?
An organization is implementing encryption for data at rest to reduce the risk associated with unauthorized access. Which of the following MUST be considered to assess the residual risk?
An organization ' s HR department has implemented a policy requiring staff members to take a minimum of five consecutive days leave per year to mitigate the risk of malicious insideractivities. Which of the following is the BEST key performance indicator (KPI) of the effectiveness of this policy?
Which of the following is the GREATEST risk associated with the misclassification of data?
Which of the following is MOST useful for measuring the existing risk management process against a desired state?
An organization ' s chief information officer (CIO) has proposed investing in a new. untested technology to take advantage of being first to market Senior management has concerns about the success of the project and has set a limit for expenditures before final approval. This conditional approval indicates the organization ' s risk:
Which of the following is the MOST important benefit of implementing a data classification program?
An organization is implementing data warehousing infrastructure. Senior management is concerned about safeguarding client data security in this new environment. Which of the following should the risk practitioner recommend be done NEXT?
An organization is developing a risk universe to create a holistic view of its overall risk profile. Which of the following is the GREATEST barrier to achieving the initiative ' s objectives?
A risk practitioner has identified that the agreed recovery time objective (RTO) with a Software as a Service (SaaS) provider is longer than the business expectation. Which ot the following is the risk practitioner ' s BEST course of action?
it was determined that replication of a critical database used by two business units failed. Which of the following should be of GREATEST concern1?
When establishing an enterprise IT risk management program, it is MOST important to:
During implementation of an intrusion detection system (IDS) to monitor network traffic, a high number of alerts is reported. The risk practitioner should recommend to:
When reporting to senior management on changes in trends related to IT risk, which of the following is MOST important?
A migration from an in-house developed system to an external cloud-based solution is affecting a previously rated key risk scenario related to payroll processing. Which part of the risk register should be updated FIRST?
Which of the following BEST enables a risk practitioner to focus on risk factors that could potentially affect the results of an IT initiative?
The risk associated with an asset before controls are applied can be expressed as:
The BEST way to justify the risk mitigation actions recommended in a risk assessment would be to:
Which of the following should be the GREATEST concern for an organization that uses open source software applications?
Which of the following deficiencies identified during a review of an organization ' s cybersecurity policy should be of MOST concern?
Which of the following issues should be of GREATEST concern when evaluating existing controls during a risk assessment?
When performing a risk assessment of a new service to support a core business process, which of the following should be done FIRST to ensure continuity of operations?
The BEST key performance indicator (KPI) for monitoring adherence to an organization ' s user accounts provisioning practices is the percentage of:
Which of the following scenarios is MOST likely to cause a risk practitioner to request a formal risk acceptance sign-off?
Which of the following is the BEST indication of an improved risk-aware culture following the implementation of a security awareness training program for all employees?
Which of the following would be a risk practitioner ' $ BEST recommendation to help ensure cyber risk is assessed and reflected in the enterprise-level risk profile?
Which of the following is the BEST approach to resolve a disagreement between stakeholders regarding the impact of a potential risk scenario?
A risk practitioner has learned that an effort to implement a risk mitigation action plan has stalled due to lack of funding. The risk practitioner should report that the associated risk has been:
Which of the following is the MOST effective way to reduce potential losses due to ongoing expense fraud?
An organization recently implemented an automated interface for uploading payment files to its banking system to replace manual processing. Which of the following elements of the risk register is MOST appropriate for the risk practitioner to update to reflect the improved control?
Which of the following is the BEST way to identify changes to the risk landscape?
Which of the following should be determined FIRST when a new security vulnerability is made public?
While evaluating control costs, management discovers that the annual cost exceeds the annual loss expectancy (ALE) of the risk. This indicates the:
Which of the following is the BEST key performance indicator (KPI) to measure the effectiveness of a disaster recovery test of critical business processes?
A control for mitigating risk in a key business area cannot be implemented immediately. Which of the following is the risk practitioner ' s BEST course of action when a compensating control needs to be applied?
Which of the following should be the PRIMARY input to determine risk tolerance?
A risk assessment has revealed that the probability of a successful cybersecurity attack is increasing. The potential loss could exceed the organization ' s risk appetite. Which of the following ould be the MOST effective course of action?
Which of the following will BEST help to ensure key risk indicators (KRIs) provide value to risk owners?
The PRIMARY benefit of conducting a risk workshop using a top-down approach instead of a bottom-up approach is the ability to:
Which of the following is the BEST way to detect zero-day malware on an end user ' s workstation?
Legal and regulatory risk associated with business conducted over the Internet is driven by:
A risk practitioner is evaluating policies defined by an organization as part of its IT security framework. Which of the following would be of GREATEST concern?
Which of the following will BEST help to ensure implementation of corrective action plans?
In order to determining a risk is under-controlled the risk practitioner will need to
An organization has allowed its cyber risk insurance to lapse while seeking a new insurance provider. The risk practitioner should report to management that the risk has been:
An external security audit has reported multiple findings related to control noncompliance. Which of the following would be MOST important for the risk practitioner to communicate to senior management?
Which of the following is MOST helpful to review when assessing the risk exposure associated with ransomware?
Which of the following findings of a security awareness program assessment would cause the GREATEST concern to a risk practitioner?
Which of the following is the BEST key performance indicator (KPI) for determining how well an IT policy is aligned to business requirements?
The BEST reason to classify IT assets during a risk assessment is to determine the:
An organization has decided to postpone the assessment and treatment of several risk scenarios because stakeholders are unavailable. As a result of this decision, the risk associated with these new entries has been;
Which of the following is the BEST method to maintain a common view of IT risk within an organization?
Which of the following is MOST important to communicate to senior management during the initial implementation of a risk management program?
Which of the following is the PRIMARY risk management responsibility of the third line of defense?
Which of the following conditions presents the GREATEST risk to an application?
During the creation of an organization ' s IT risk management program, the BEST time to identify key risk indicators (KRIs) is while:
When testing the security of an IT system, il is MOST important to ensure that;
Which of the following is the BEST way for a risk practitioner to help management prioritize risk response?
Which of the following BEST indicates the risk appetite and tolerance level (or the risk associated with business interruption caused by IT system failures?
A vendor ' s planned maintenance schedule will cause a critical application to temporarily lose failover capabilities. Of the following, who should approve this proposed schedule?
Which of the following will BEST help to ensure implementation of corrective action plans?
Which of the following management action will MOST likely change the likelihood rating of a risk scenario related to remote network access?
A hospital recently implemented a new technology to allow virtual patient appointments. Which of the following should be the risk practitioner ' s FIRST course of action?
Which of the following process controls BEST mitigates the risk of an employee issuing fraudulent payments to a vendor?
An enterprise has taken delivery of software patches that address vulnerabilities in its core business software. Prior to implementation, which of the following is the MOST important task to be performed?
Which of the following is the GREATEST concern when using artificial intelligence (AI) language models?
A segregation of duties control was found to be ineffective because it did not account for all applicable functions when evaluating access. Who is responsible for ensuring the control is designed to effectively address risk?
An organization has procured a managed hosting service and just discovered the location is likely to be flooded every 20 years. Of the following, who should be notified of this new information FIRST.
Which of the following is a specific concern related to machine learning algorithms?
While reviewing a contract of a cloud services vendor, it was discovered that the vendor refuses to accept liability for a sensitive data breach. Which of the following controls will BES reduce the risk associated with such a data breach?
A software developer has administrative access to a production application. Which of the following should be of GREATEST concern to a risk practitioner?
Which of the following BEST enables the recovery of data that has been encrypted by a ransomware attack?
Which of the following activities is a responsibility of the second line of defense?
Which of the following is the BEST control to minimize the risk associated with scope creep in software development?
When reviewing a business continuity plan (BCP). which of the following would be the MOST significant deficiency?
Which of the following is the MOST important reason to validate that risk responses have been executed as outlined in the risk response plan ' '
Which of the following would be MOST useful to management when allocating resources to mitigate risk to the organization?
Which of the following would BEST help to address the risk associated with malicious outsiders modifying application data?
What is the BEST approach for determining the inherent risk of a scenario when the actual likelihood of the risk is unknown?
An organization has introduced risk ownership to establish clear accountability for each process. To ensure effective risk ownership, it is MOST important that:
Which of the following is the BEST method for determining an enterprise ' s current appetite for risk?
When developing risk treatment alternatives for a Business case, it is MOST helpful to show risk reduction based on:
A risk practitioner wants to identify potential risk events that affect the continuity of a critical business process. Which of the following should the risk practitioner do FIRST?
Which of the following is the MOST important criteria for selecting key risk indicators (KRIs)?
Which of the following is the MOST important outcome of reviewing the risk management process?
Which of the following is the BEST key control indicator (KCI) for risk related to IT infrastructure failure?
Concerned about system load capabilities during the month-end close process, management requires monitoring of the average time to complete tasks and monthly reporting of the findings. What type of measure has been established?
Who should be responsible (of evaluating the residual risk after a compensating control has been
An organization has initiated a project to implement an IT risk management program for the first time. The BEST time for the risk practitioner to start populating the risk register is when:
Which of the following should be the starting point when performing a risk analysis for an asset?
Which of the following attributes of a key risk indicator (KRI) is MOST important?
An organization has implemented a policy requiring staff members to take a minimum of five consecutive days ' leave per year to mitigate the risk of malicious insider activities. Which of the following is the BEST key performance indicator (KPI) of the effectiveness of this policy?
Which of the following is the GREATEST benefit to an organization when updates to the risk register are made promptly after the completion of a risk assessment?
An organization has established workflows in its service desk to support employee reports of security-related concerns. Which of the following is the MOST efficient approach to analyze these concerns?
When reporting on the performance of an organization ' s control environment including which of the following would BEST inform stakeholders risk decision-making?
Which of the following is the MOST effective way to identify changes in the performance of the control environment?
An organization has an internal control that requires all access for employees be removed within 15 days of their termination date. Which of the following should the risk practitioner use to monitor
adherence to the 15-day threshold?
Within the risk management space, which of the following activities could be
delegated to a cloud service provider?
Which of the following is the BEST indication that key risk indicators (KRIs) should be revised?
Which of the following would be MOST helpful to an information security management team when allocating resources to mitigate exposures?
A peer review of a risk assessment finds that a relevant threat community was not included. Mitigation of the risk will require substantial changes to a software application. Which of the following is the BEST course of action?
An organization has just started accepting credit card payments from customers via the corporate website. Which of the following is MOST likely to increase as a result of this new initiative?
Which of the following is the GREATEST benefit of identifying appropriate risk owners?
Which of the following is the BEST approach for obtaining management buy-in
to implement additional IT controls?
A financial organization is considering a project to implement the use of blockchain technology. To help ensure the organization ' s management team can make informed decisions on the project, which of the following should the risk practitioner reassess?
Which of the following is MOST important to the effective monitoring of key risk indicators (KRIS)?
Which of the following BEST indicates the condition of a risk management program?
Who is BEST suited to determine whether a new control properly mitigates data loss risk within a system?
In an organization that allows employee use of social media accounts for work purposes, which of the following is the BEST way to protect company sensitive information from being exposed?
An organization allows programmers to change production systems in emergency situations. Which of the following is the BEST control?
Reviewing which of the following provides the BEST indication of an organizations risk tolerance?
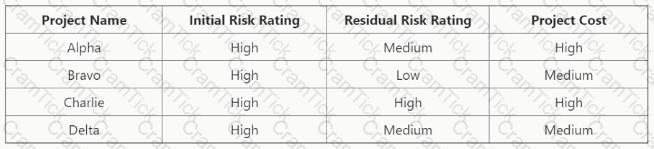
An organization has four different projects competing for funding to reduce overall IT risk. Which project should management defer?
Which of the following is the GREATEST risk of relying on artificial intelligence (Al) within heuristic security systems?
To minimize risk in a software development project, when is the BEST time to conduct a risk analysis?
Which of the following is the MOST important objective of regularly presenting the project risk register to the project steering committee?
Which of the following is the MOST important course of action for a risk practitioner when reviewing the results of control performance monitoring?
To mitigate the risk of using a spreadsheet to analyze financial data, IT has engaged a third-party vendor to deploy a standard application to automate the process. Which of the following parties should own the risk associated with calculation errors?
Which of the following is MOST important for an organization to consider when developing its IT strategy?
The PRIMARY reason to have risk owners assigned to entries in the risk register is to ensure:
When a risk practitioner is determining a system ' s criticality. it is MOST helpful to review the associated:
In order to efficiently execute a risk response action plan, it is MOST important for the emergency response team members to understand:
Which of the following is the MOST effective way to assess the risk associated with outsourcing IT processes?
A risk practitioner ' s BEST guidance to help an organization develop relevant risk scenarios is to ensure the scenarios are:
Which of the following should be a risk practitioner ' s GREATEST concern upon learning of failures in a data migration activity?
Which of the following is BEST used to aggregate data from multiple systems to identify abnormal behavior?
Which of the following would present the GREATEST challenge when assigning accountability for control ownership?
After the implementation of a remediation plan, an assessment of associated control design and operating effectiveness can determine the level of:
Which of the following would provide executive management with the BEST information to make risk decisions as a result of a risk assessment?
Which stakeholders are PRIMARILY responsible for determining enterprise IT risk appetite?
Which of the following is the BEST approach to mitigate the risk associated with outsourcing network management to an external vendor who will have access to sensitive information assets?
Which of the following should be implemented to BEST mitigate the risk associated with infrastructure updates?
An organization has identified that terminated employee accounts are not disabled or deleted within the time required by corporate policy. Unsure of the reason, the organization has decided to monitor the situation for three months to obtain more information. As a result of this decision, the risk has been:
An organization is preparing to transfer a large number of customer service representatives to the sales department. Of the following, who is responsible for mitigating the risk associated with residual system access?
Which of the following roles is PRIMARILY accountable for risk associated with business information protection?
Which of the following should be considered FIRST when creating a comprehensive IT risk register?
Who is BEST suited to provide objective input when updating residual risk to reflect the results of control effectiveness?
A risk practitioner is organizing a training session lo communicate risk assessment methodologies to ensure a consistent risk view within the organization Which of the following i < the MOST important topic to cover in this training?
Which of the following BEST enables risk-based decision making in support of a business continuity plan (BCP)?
Which of the following is the PRIMARY benefit of implementing key control indicators (KCIs)?
What is the PRIMARY role of the application owner when changes are being introduced into an existing environment?
A monthly payment report is generated from the enterprise resource planning (ERP) software to validate data against the old and new payroll systems. What is the BEST way to mitigate the risk associated with data integrity loss in the new payroll system after data migration?
Which of the following BEST enables an organization to determine whether external emerging risk factors will impact the organization ' s risk profile?
Which of the following has the GREATEST positive impact on ethical compliance within the risk management process?
Which of the following is MOST helpful in identifying gaps between the current and desired state of the IT risk environment?
After the implementation of a blockchain solution, a risk practitioner discovers noncompliance with new industry regulations. Which of the following is the MOST important course of actionpriorto informing senior management?
Senior management has requested more information regarding the risk associated with introducing a new application into the environment. Which of the following should be done FIRST?
A risk practitioner is developing a set of bottom-up IT risk scenarios. The MOST important time to involve business stakeholders is when:
Which of the following would prompt changes in key risk indicator {KRI) thresholds?
An application owner has specified the acceptable downtime in the event of an incident to be much lower than the actual time required for the response team to recover the application. Which of the following should be the NEXT course of action?
Which of the following is the BEST indicator of an effective IT security awareness program?
An internally developed payroll application leverages Platform as a Service (PaaS) infrastructure from the cloud. Who owns the related data confidentiality risk?
Which of the following BEST enables an organization to increase the likelihood of identifying risk associated with unethical employee behavior?
A user has contacted the risk practitioner regarding malware spreading laterally across the organization ' s corporate network. Which of the following is the risk practitioner’s BEST course of action?
Which of the following is the BEST metric to demonstrate the effectiveness of an organization ' s patch management process?
What is the GREATEST concern with maintaining decentralized risk registers instead of a consolidated risk register?
Which of the following is the FIRST consideration to reduce risk associated with the storage of personal data?
Which of the following methods is the BEST way to measure the effectiveness of automated information security controls prior to going live?
When establishing leading indicators for the information security incident response process it is MOST important to consider the percentage of reported incidents:
Which of the following activities BEST facilitates effective risk management throughout the organization?
To define the risk management strategy which of the following MUST be set by the board of directors?
Which of the following should be considered FIRST when assessing risk associated with the adoption of emerging technologies?
Which of the following provides the MOST reliable evidence of a control ' s effectiveness?
Which of the following provides the BEST measurement of an organization ' s risk management maturity level?
An organization ' s internal audit department is considering the implementation of robotics process automation (RPA) to automate certain continuous auditing tasks. Who would own the risk associated with ineffective design of the software bots?
Which of the following is the BEST method to identify weaknesses in an organization ' s technical environment that could be leveraged by an attacker to gain access?
Which of the following is the MOST important responsibility of a business process owner to enable effective IT risk management?
Which of the following is the MOST important foundational element of an effective three lines of defense model for an organization?
What is the BEST recommendation to reduce the risk associated with potential system compromise when a vendor stops releasing security patches and updates for a business-critical legacy system?
Which of the following should be a risk practitioner ' s NEXT step upon learning the impact of an organization ' s noncompliance with a specific legal regulation?
Who is responsible for IT security controls that are outsourced to an external service provider?
Which of the following is the PRIMARY reason to establish the root cause of an IT security incident?
Which of the following would BEST mitigate the ongoing risk associated with operating system (OS) vulnerabilities?
Which of the following will BEST help mitigate the risk associated with malicious functionality in outsourced application development?
A business impact analysis (BIA) enables an organization to determine appropriate IT risk mitigation actions by:
Which of the following is the MOST important key performance indicator (KPI) to monitor the effectiveness of disaster recovery processes?
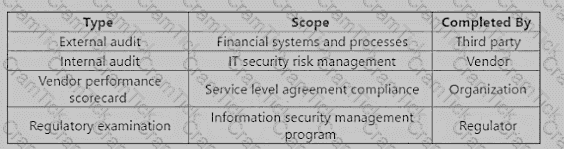
After a high-profile systems breach at an organization s key vendor, the vendor has implemented additional mitigating controls. The vendor has voluntarily shared the following set of assessments:
Which of the assessments provides the MOST reliable input to evaluate residual risk in the vendor ' s control environment?
An incentive program is MOST likely implemented to manage the risk associated with loss of which organizational asset?
Which of the following is the MOST useful information an organization can obtain from external sources about emerging threats?
Which of the following metrics is BEST used to communicate to senior management that the control environment manages risk within appetite and tolerance?
When determining which control deficiencies are most significant, which of the following would provide the MOST useful information?
Which of the following occurs during the implementation phase of the system development life cycle (SDLC)?
A risk heat map is MOST commonly used as part of an IT risk analysis to facilitate risk:
Which of the following is the MOST appropriate key performance indicator (KPI) to measure change management performance?
Which of the following is the PRIMARY reason to ensure software engineers test patches before release to the production environment?
A new risk practitioner finds that decisions for implementing risk response plans are not being made. Which of the following would MOST likely explain this situation?
An organization wants to transfer risk by purchasing cyber insurance. Which of the following would be MOST important for the risk practitioner to communicate to senior management for contract negotiation purposes?
When assessing the maturity level of an organization ' s risk management framework, which of the following should be of GREATEST concern to a risk practitioner?
Which of the following is the MOST useful information for a risk practitioner when planning response activities after risk identification?
Which of the following is MOST important to identify when developing top-down risk scenarios?
Which of the following is MOST important when creating a program to reduce ethical risk?
During a routine check, a system administrator identifies unusual activity indicating an intruder within a firewall. Which of the following controls has MOST likely been compromised?
Which of the following should be accountable for ensuring that media containing financial information are adequately destroyed per an organization ' s data disposal policy?
Which of the following is the MOST appropriate key control indicator (KCI) to help an organization prevent successful cyber risk events on the external-facing infrastructure?
Which of the following is the GREATEST risk associated with the transition of a sensitive data backup solution from on-premise to a cloud service provider?
An organization has determined that risk is not being adequately tracked and
managed due to a distributed operating model. Which of the following is the
BEST way to address this issue?
Which of the following BEST indicates effective information security incident management?
An IT control gap has been identified in a key process. Who would be the MOST appropriate owner of the risk associated with this gap?
Which of the following outcomes of disaster recovery planning is MOST important to enable the initiation of necessary actions during a disaster?
The PRIMARY objective of the board of directors periodically reviewing the risk profile is to help ensure:
Which of the following would cause the GREATEST concern for a risk practitioner reviewing the IT risk scenarios recorded in an organization’s IT risk register?
An organization ' s business gap analysis reveals the need for a robust IT risk strategy. Which of the following should be the risk practitioner ' s PRIMARY consideration when participating in development of the new strategy?
What should be the PRIMARY objective for a risk practitioner performing a post-implementation review of an IT risk mitigation project?
An organization ' s senior management is considering whether to acquire cyber insurance. Which of the following is the BEST way for the risk practitioner to enable management’s decision?
Which of the following should be given the HIGHEST priority when developing a response plan for risk assessment results?
A risk practitioner has received an updated enterprise risk management (ERM) report showing that residual risk is now within the organization ' s defined appetite and tolerance levels. Which of the following is the risk practitioner ' s BEST course of action?
Which of the following is the MOST important requirement for monitoring key risk indicators (KRls) using log analysis?
Which of the following is the BEST indication that an organization ' s IT asset life cycle is poorly managed?
The number of tickets to rework application code has significantly exceeded the established threshold. Which of the following would be the risk practitioner s BEST recommendation?
The PRIMARY objective of testing the effectiveness of a new control before implementation is to:
Which of the following approaches MOST effectively enables accountability for data protection?
Which of the following is MOST important to include in a Software as a Service (SaaS) vendor agreement?
A risk practitioner notes control design changes when comparing risk response to a previously approved action plan. Which of the following is MOST important for the practitioner to confirm?
In the three lines of defense model, a PRIMARY objective of the second line is to:
Which of the following should a risk practitioner review FIRST when evaluating risk events associated with the organization ' s data flow model?
Before implementing instant messaging within an organization using a public solution, which of the following should be in place to mitigate data leakage risk?
Which of the following BEST indicates whether security awareness training is effective?
From a data protection and regulatory compliance perspective, which of the following is the MOST important reason for a global organization to use immutable backups?
An organization is outsourcing a key database to be hosted by an external service provider. Who is BEST suited to assess the impact of potential data loss?
What is the MOST important consideration when selecting key performance indicators (KPIs) for control monitoring?
As part of an overall IT risk management plan, an IT risk register BEST helps management:
An organization planning to transfer and store its customer data with an offshore cloud service provider should be PRIMARILY concerned with:
Which of the following is MOST important for a risk practitioner to consider when evaluating plans for changes to IT services?
Which type of cloud computing deployment provides the consumer the GREATEST degree of control over the environment?
Which of the following is MOST important to review when evaluating the ongoing effectiveness of the IT risk register?
An automobile manufacturer is considering implementing an Internet of Things (IoT) network to improve customer service by collecting customer and vehicle data. Which of the following would be the risk practitioner’s BEST recommendation?
Which of the following provides the BEST indication that existing controls are effective?
An information system for a key business operation is being moved from an in-house application to a Software as a Service (SaaS) vendor. Which of the following will have the GREATEST impact on the ability to monitor risk?
Which of the following is MOST important to review when an organization needs to transition the majority of its employees to remote work during a crisis?
Which of the following is the PRIMARY benefit of using a risk map with stakeholders?
Which of the following BEST helps to identify significant events that could impact an organization?
Vulnerability analysis
A risk practitioner is summarizing the results of a high-profile risk assessment sponsored by senior management. The BEST way to support risk-based decisions by senior management would be to:
An organization is planning to outsource its payroll function to an external service provider Which of the following should be the MOST important consideration when selecting the provider?
Which of the following would present the MOST significant risk to an organization when updating the incident response plan?
Winch of the following can be concluded by analyzing the latest vulnerability report for the it infrastructure?
An organization is moving its critical assets to the cloud. Which of the following is the MOST important key performance indicator (KPI) to include in the service level agreement (SLA)?
Which of the following BEST indicates that an organization ' s risk management processes are mature?
Management has required information security awareness training to reduce the risk associated with credential compromise. What is the BEST way to assess the effectiveness of the training?
When implementing an IT risk management program, which of the following is the BEST time to evaluate current control effectiveness?
A risk practitioner is performing a risk assessment of recent external advancements in quantum computing. Which of the following would pose the GREATEST concern for the risk practitioner?
The BEST way to obtain senior management support for investment in a control implementation would be to articulate the reduction in:
Which of the following would MOST effectively protect financial records from ransomware attacks?
An organization wants to assess the maturity of its internal control environment. The FIRST step should be to:
Which of the following is the GREATEST benefit of a three lines of defense structure?
Which of the following is the PRIMARY purpose of creating and documenting control procedures?
Which of the following will provide the BEST measure of compliance with IT policies?
A risk practitioner is concerned with potential data loss in the event of a breach at a hosted third-party provider. Which of the following is the BEST way to mitigate this risk?
Which of the following BEST indicates the effectiveness of anti-malware software?
Which of the following poses the GREATEST risk to an organization ' s operations during a major it transformation?
While reviewing the risk register, a risk practitioner notices that different business units have significant variances in inherent risk for the same risk scenario. Which of the following is the BEST course of action?
An organization uses an automated vulnerability scanner to identify potential vulnerabilities on various enterprise systems. Who is accountable for ensuring the vulnerabilities are mitigated?
Isaca Certification | CRISC Questions Answers | CRISC Test Prep | Certified in Risk and Information Systems Control Questions PDF | CRISC Online Exam | CRISC Practice Test | CRISC PDF | CRISC Test Questions | CRISC Study Material | CRISC Exam Preparation | CRISC Valid Dumps | CRISC Real Questions | Isaca Certification CRISC Exam Questions


