A banking firm's cloud server will be decommissioned after a successful proof of concept using mirrored data. Which of the following is the best action to take regarding the storage used on the decommissioned server?
A company's VMs that are created using the noncritical application tag are automatically shut down at 5:00 p.m. using a cronjob. Which of the following actions would allow a cloud engineer to stop all unresponsive instances with the least effort in case the automation fails?
A cloud engineer is troubleshooting a connectivity issue. The application server with IP 192.168.1.10 in one subnet is not connecting to the MySQL database server with IP 192.168.2 20 in a different subnet. The cloud engineer reviews the following information:
Application Server Stateful Firewall
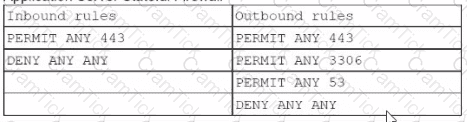
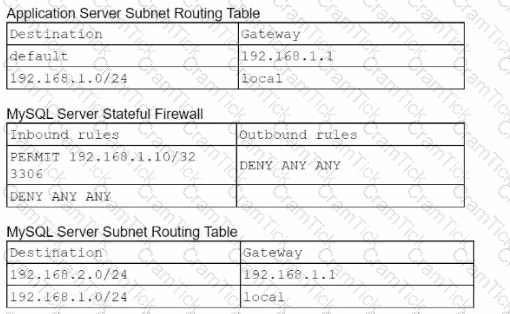
Which of the following should the cloud engineer address lo fix the communication issue?
A cloud solutions architect is designing a VM-based solution that requires reducing the cost as much as possible. Which of the following solutions will best satisfy this requirement?
A write-intensive workload is having frequent performance issues. The workload is running on pay-as-you-go VMs. These VMs use SSDs and have appropriate CPU and RAM sizes. The workload writes millions of small files and has a one-year retention requirement. Which of the following actions should be taken?
A cloud engineer is in charge of deploying a platform in an laaS public cloud. The application tracks the state using session cookies, and there are no affinity restrictions. Which of
the following will help the engineer reduce monthly expenses and allow the application to provide the service?
Which of the following describes the main difference between public and private container repositories?
For compliance purposes, a cloud developer at an insurance company needs to save all customer policies for more than ten years. Which of the following options is the most cost-
efficient tier to save the data in the cloud?
An engineer wants lo scale several cloud workloads on demand. Which of the following approaches is the most suitable?
A software engineer is integrating an application lo The cloud that is web socket based. Which of the following applications is the engineer most likely deploying?
Two CVEs are discovered on servers in the company's public cloud virtual network. The CVEs are listed as having an attack vector value of network and CVSS score of 9.0. Which
of the following actions would be the best way to mitigate the vulnerabilities?
An organization's web application experiences penodic bursts of traffic when a new video is launched. Users are reporting poor performance in the middle of the month. Which of the following scaling approaches should the organization use to scale based on forecasted traffic?
Which of the following is the correct order of the steps to take when a system is suspected of being vulnerable?
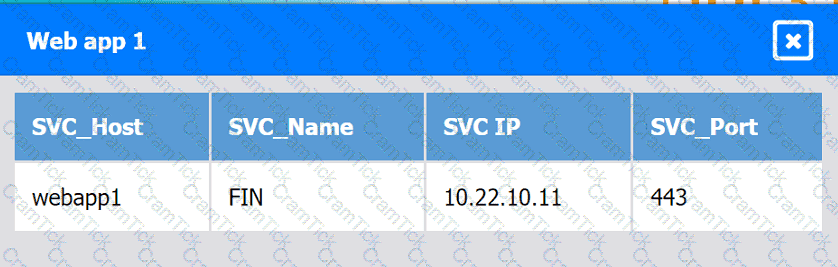
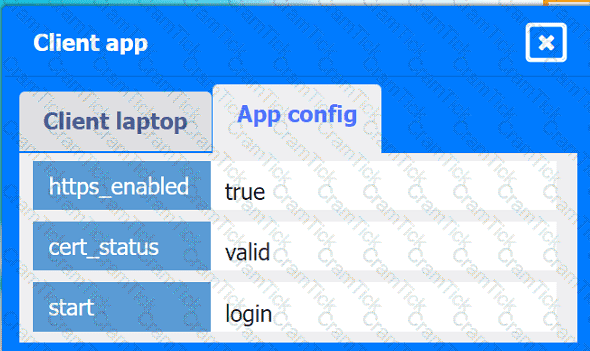
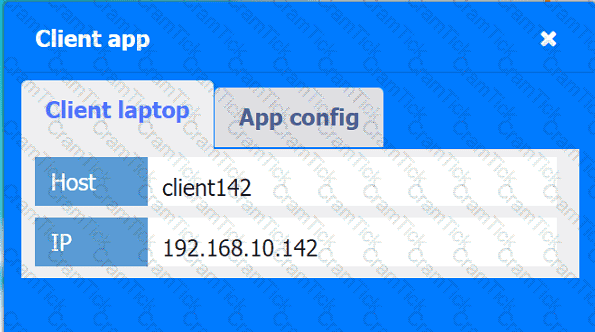
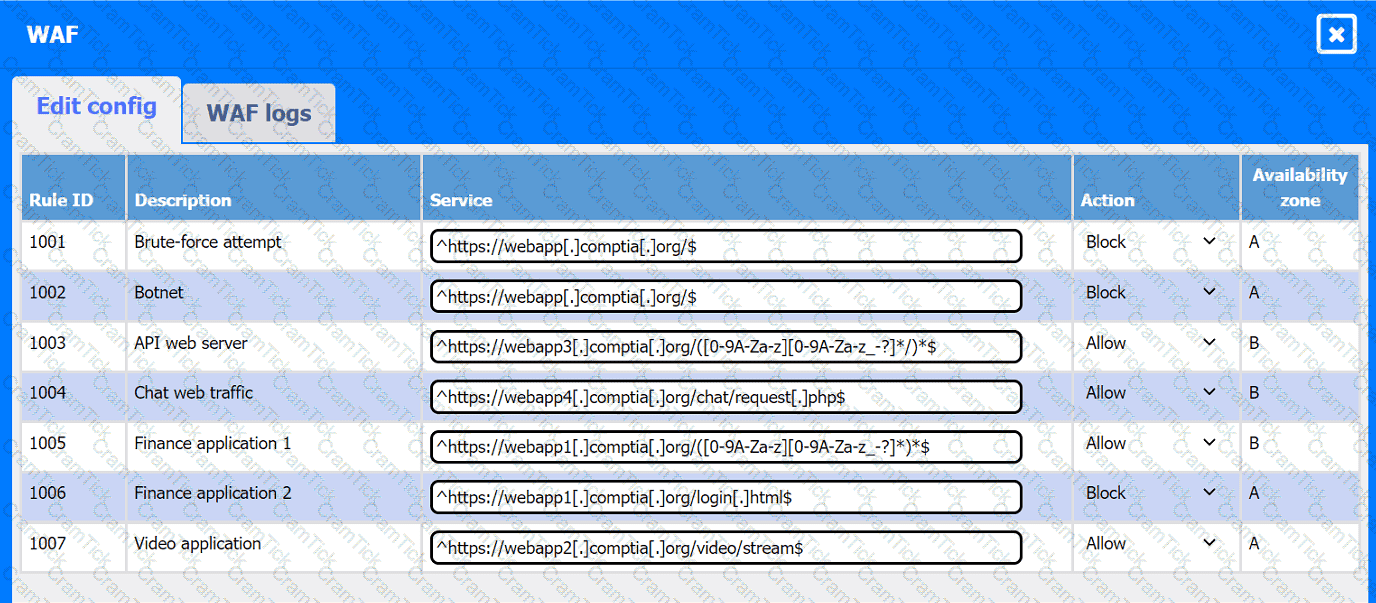
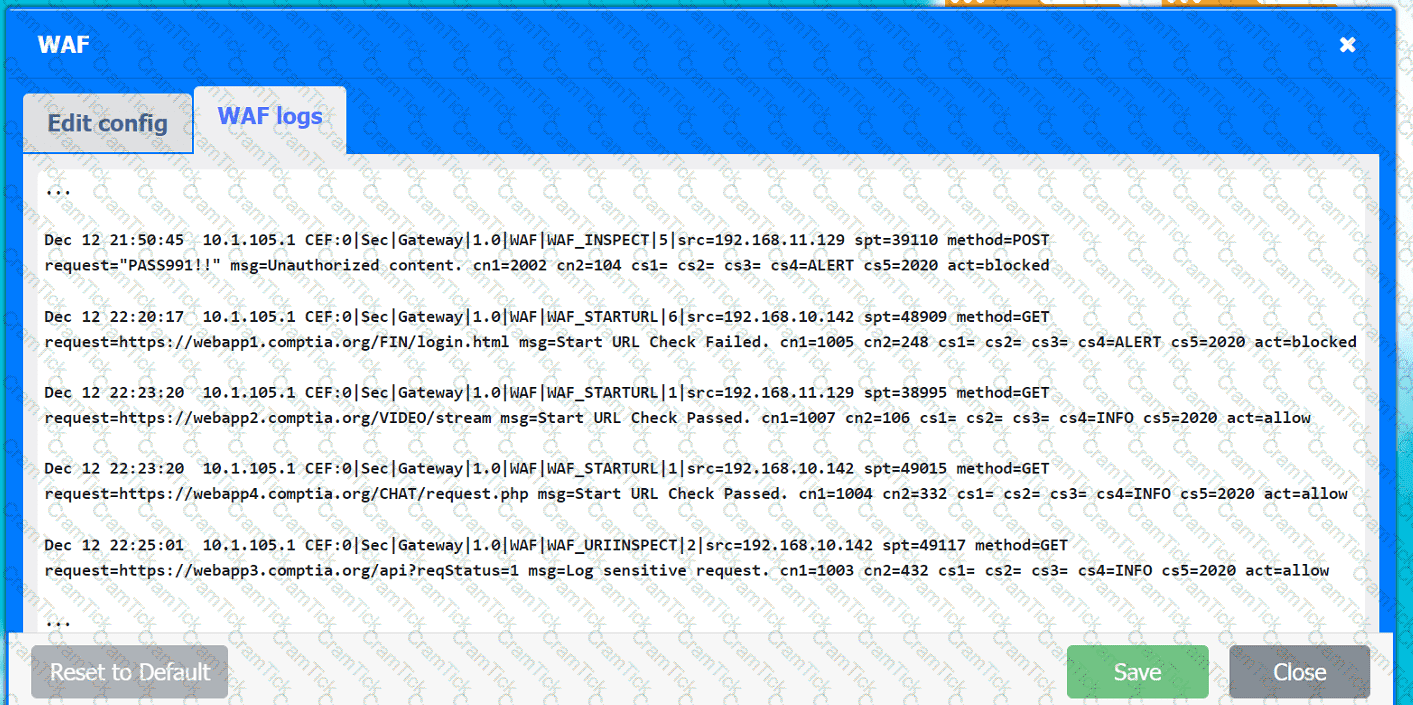
A company hosts various containerized applications for business uses. A client reports that one of its routine business applications fails to load the web-based login prompt hosted in the company cloud.
INSTRUCTIONS
Click on each device and resource. Review the configurations, logs, and characteristics of each node in the architecture to diagnose the issue. Then, make the necessary changes to the WAF configuration to remediate the issue.
Web app 1
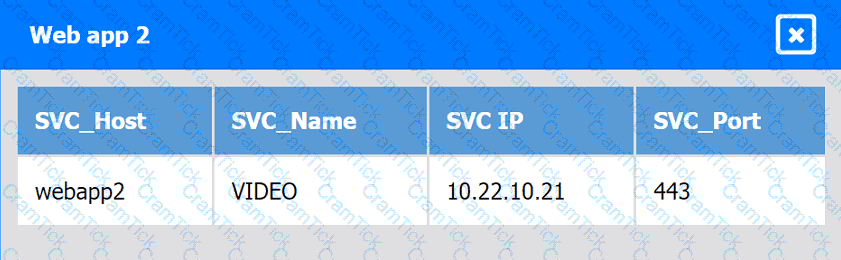
Web app 2
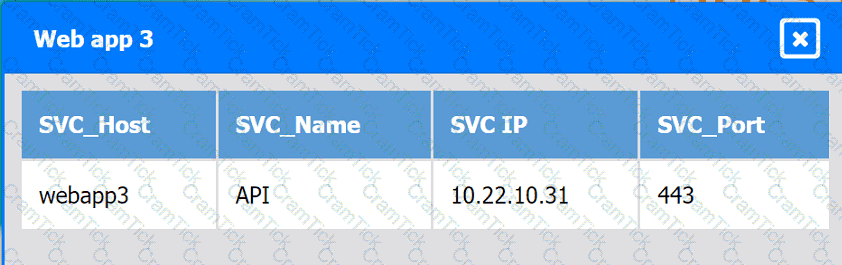
Web app 3
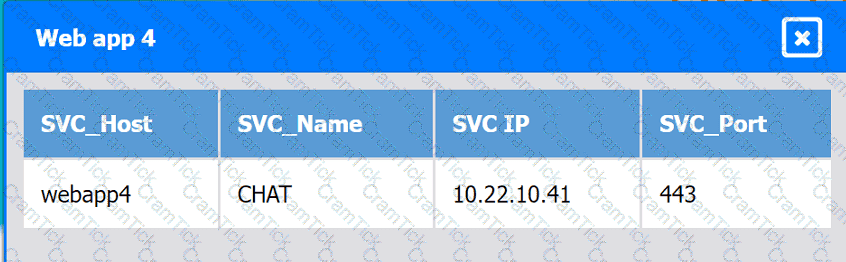
Web app 4
Client app
A cloud engineer is concerned about command-and-control (C2) communication leaving a cloud network over HTTPS. Which of the following should the cloud engineer implement to most efficiently identify this type of communication?
Once a change has been made to templates, which of the following commands should a cloud architect use next to deploy an laaS platform?
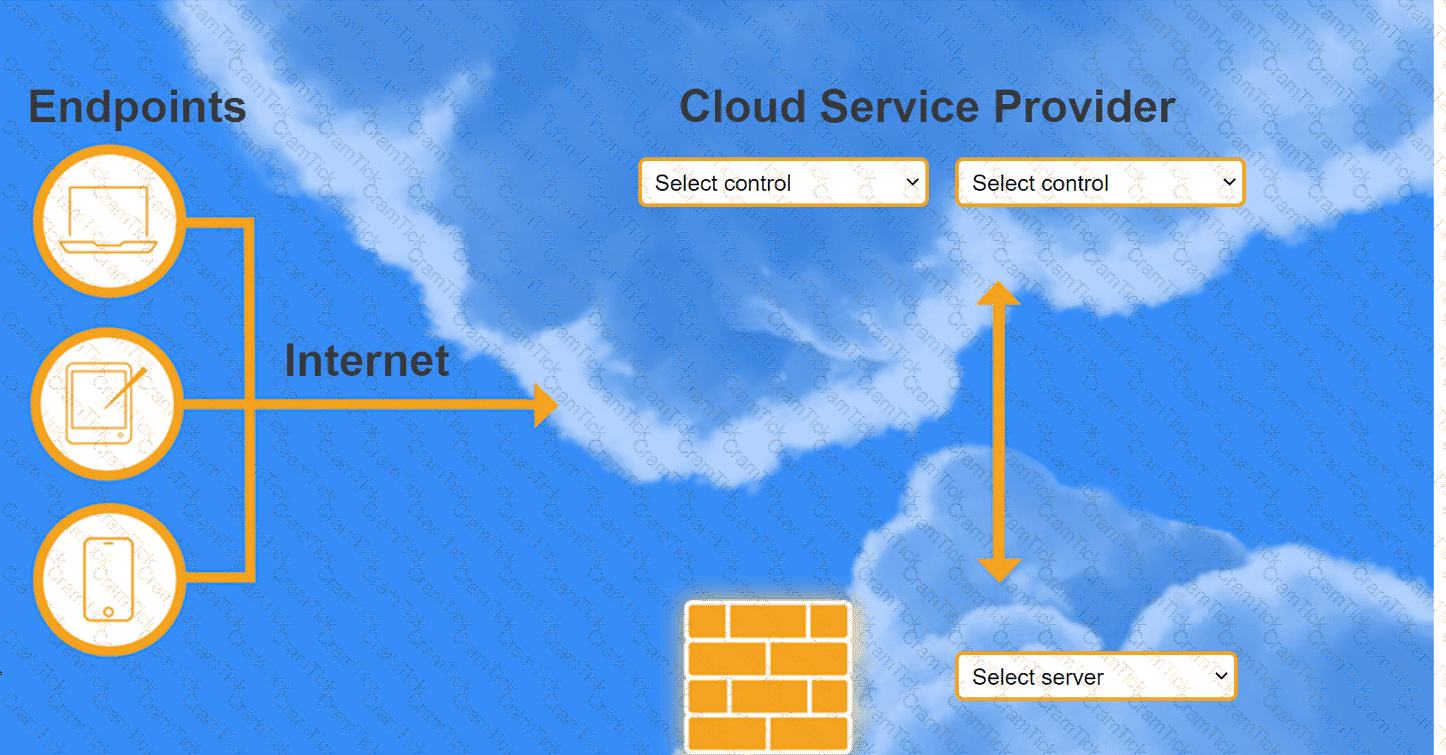
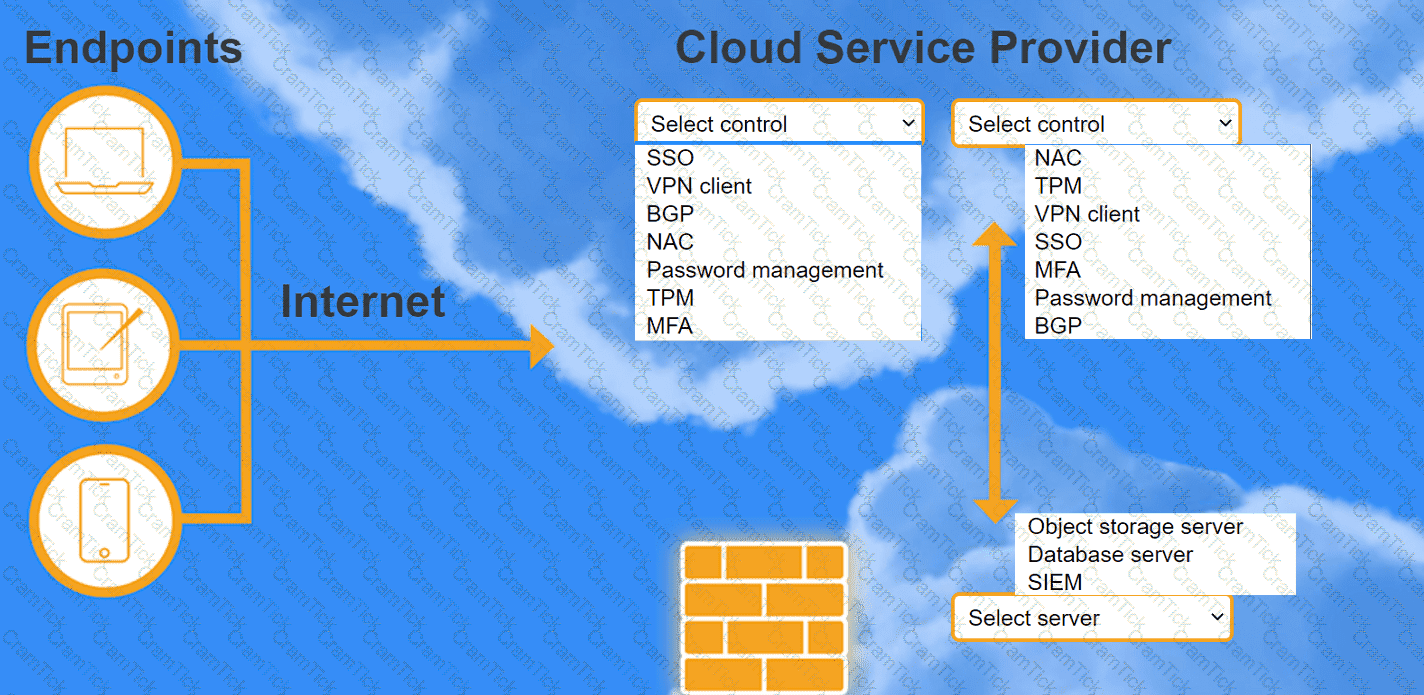
A highly regulated business is required to work remotely, and the risk tolerance is very low. You are tasked with providing an identity solution to the company cloud that includes the following:
secure connectivity that minimizes user login
tracks user activity and monitors for anomalous activity
requires secondary authentication
INSTRUCTIONS
Select controls and servers for the proper control points.
A cloud engineer hardened the WAF for a company that operates exclusively in North America. The engineer did not make changes to any ports, and all protected applications have
continued to function as expected. Which of the following configuration changes did the engineer most likely apply?
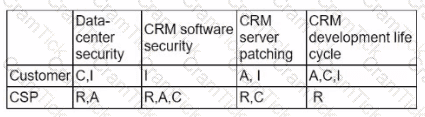
An administrator received a report that company data has been compromised. The compromise occurred on a holiday, and no one in the organization was working. While reviewing
the logs from the holiday, the administrator noted the following details:
The most appropriate action for the cloud security analyst to recommend is using CIS-hardened images. These images are pre-configured by the Center for Internet Security to provide security benchmark standards that help in mitigating vulnerabilities in publicly available container images. References: CompTIA Cloud+ Study Guide (Exam CV0-004) - Chapter on Cloud Security Posture
Which of the following accounts should the administrator disable to prevent a further breach?
A cloud developer is creating a static website that customers will be accessing globally. Which of the following services will help reduce latency?
Which of the following interfaces is most commonly used for SSDs but not for HDDs?
Which of the following provides secure, private communication between cloud environments without provisioning additional hardware or appliances?
A cloud service provider requires users to migrate to a new type of VM within three months. Which of the following is the best justification for this requirement?
A cloud administrator is working on the deployment of an e-commerce website. The administrator evaluates the scaling methods to be implemented when seasonal or flash sales are launched. Which of the following scaling approaches should the administrator use to best manage this scenario?
A company's engineering department is conducting a month-long test on the scalability of an in-house-developed software that requires a cluster of 100 or more servers. Which of
the following models is the best to use?
Which of the following should be used on containers to process data and keep the output in files for later review?
A cloud engineer is collecting web server application logs to troubleshoot intermittent issues. However, the logs are piling up and causing storage issues. Which of the following log
mechanisms should the cloud engineer implement to address this issue?
An organization needs to retain its data for compliance reasons but only when required. Which of the following would be the most cost-effective type of tiered storage?
A cloud engineer is exploring options to reduce the management overhead of the servers and network. Which of the following cloud service models should the engineer implement?
A healthcare organization must follow strict compliance requirements to ensure that Pll is not leaked. The cloud administrator needs to ensure the cloud email system can support this requirement Which of the following should the organization enable?
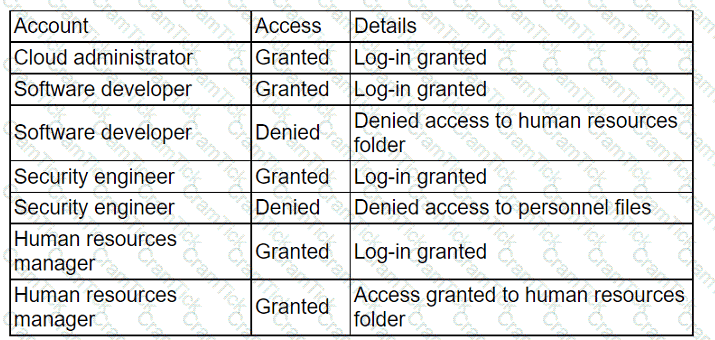
A company migrated its CRM system to a SaaS solution. The security team is updating the RAG matrix for the newly migrated CRM. Given the following table:
Which of the following responsibility assignments best aligns with the shared responsibility model for the new CRM?
An organization has been using an old version of an Apache Log4j software component in its critical software application. Which of the following should the organization use to
calculate the severity of the risk from using this component?
Which of the following do developers use to keep track of changes made during software development projects?
Given the following command:
Sdocker pull images.comptia.org/user1/myimage:latest
Which of the following correctly identifies images.comptia.org?
A systems engineer tries to mount an iSCSI LUN to a VM host in a data center, but the host does not discover any iSCSI targets. A sample of the switch configuration is shown in the following image:
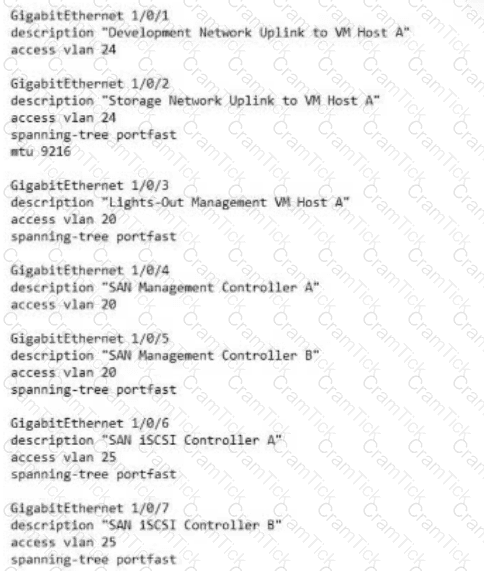
Which of the following configuration changes would most likely resolve the discovery issues?
A customer is migrating applications to the cloud and wants to grant authorization based on the classification levels of each system. Which of the following should the customer implement to ensure authorisation to systems is granted when the user and system classification properties match? (Select two).
A manager wants information about which users signed in to a certain VM during the past month. Which of the following can the cloud administrator use to obtain this information?
A cloud engineer is reviewing the following Dockerfile to deploy a Python web application:
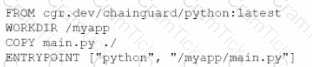
Which of the following changes should the engineer make lo the file to improve container security?
A government agency in the public sector is considering a migration from on premises to the cloud. Which of the following are the most important considerations for this cloud migration? (Select two).
A company wants to implement a work environment that will have low operational overhead and highly accessible enterprise resource planning, email, and data resources. Which of
the following cloud service models should the company implement?
Which of the following industry standards mentions that credit card data must not be exchanged or stored in cleartext?
Which of the transfer when comparing a multiregional to a single-region cloud platform design?
An e-commerce store is preparing for an annual holiday sale. Previously, this sale has increased the number of transactions between two and ten times the normal level of
transactions. A cloud administrator wants to implement a process to scale the web server seamlessly. The goal is to automate changes only when necessary and with minimal cost.
Which of the following scaling approaches should the administrator use?
A cloud engineer is concerned about command-and-control (C2) communication out of a cloud network over HTTPS. Which of the following should the cloud engineer implement to most efficiently identify the type of communication?
An administrator configures three subnets to the corporate network. All servers should communicate with the main corporate network and access the internet. The administrator creates the following configurations:
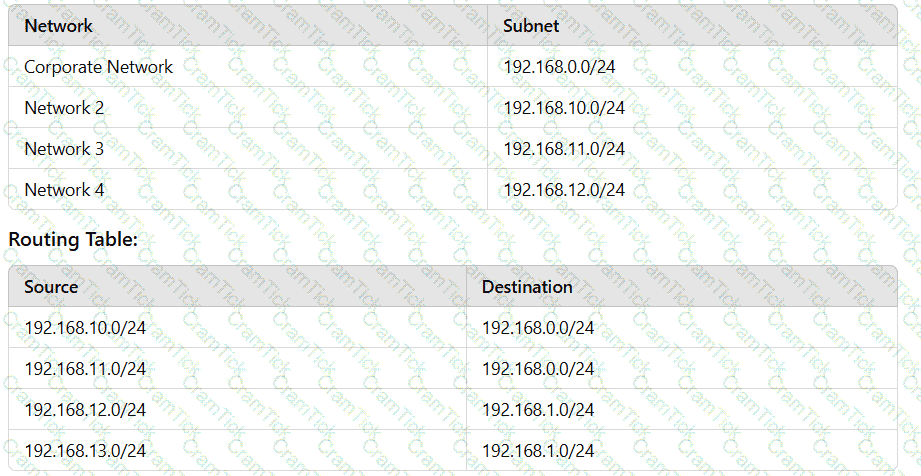
After configuring the networks, the administrator recognizes an issue with the configuration. Which of the following can the administrator change in one step to accomplish the goal?
A company operates a website that allows customers to upload, share, and retain full ownership of their photographs. Which of the following could affect image ownership as the website usage expands globally?
A cloud engineer creates an IaC repository to deploy an application to a specific region. The cloud engineer receives a new request to deploy the same application to ten different regions. Which of the following options best fulfills this new request?
A cloud engineer is developing an operating expense report that will be used to purchase various cloud billing models for virtual machine instances. The cloud billing model must meet the following requirements:
• The instance cannot be ephemeral.
• The minimum life cycle of the instance is expected to be five years.
• The software license is charged per physical CPU count.
Which of the following models would best meet these requirements?
A security team recently hired multiple interns who all need the same level of access. Which of the following controls should the security team implement to provide access to the
cloud environment with the least amount of overhead?
A company has ten cloud engineers working on different manual cloud deployments. In the past, engineers have had difficulty keeping deployments consistent. Which of the following is the best method to address this issue?
A cloud administrator needs to collect process-level, memory-usage tracking for the virtual machines that are part of an autoscaling group. Which of the following is the best way to
accomplish the goal by using cloud-native monitoring services?
Which of the following refers to the idea that data should stay within certain borders or territories?
Which of the following cloud deployment strategies is best for an organization that wants to run open-source workloads with other organizations that are sharing the cost?
A cloud developer resigned from an organization and gave a two-week notice. Within the first week since the developer resigned, a security analyst identifies large volumes of file downloads to the developer’s laptop from the source code repository. Which of the following security controls is the best way to mitigate the organization’s risk of data loss?
Which of the following is the most cost-effective way to store data that is infrequently accessed?
A cloud administrator deploys new VMs in a cluster and discovers they are getting IP addresses in the range of 169.254.0.0/16. Which of the following is the most likely cause?
A customer's facility is located in an area where natural disasters happen frequently. The customer requires the following:
• Data resiliency due to exposure to frequent natural disasters
• Data localization because of privacy regulations in the country
• High availability
Which of the following cloud resources should be provisioned to meet these requirements?
Which of the following requirements are core considerations when migrating a small business's on-premises applications to the cloud? (Select two).
A cloud architect attempts to modify a protected branch but is unable to do so. The architect receives an error indicating the action cannot be completed. Which of the following should the architect try instead''
A cloud server needs to automatically allocate more resources during sudden peak times. This allocation does not need to occur in regular intervals. Which of the following scaling
approaches should be used?
Which of the following is the most cost-effective and efficient strategy when migrating to the cloud?
A cloud administrator is working on the deployment of an e-commerce website. The administrator evaluates the scaling methods to be implemented when seasonal or flash sales are launched. Which of the following scaling approaches should the administrator use to best manage this scenario?
Which of the following application migration strategies will best suit a customer who wants to move a simple web application from an on-premises server to the cloud?
A cloud engineer wants to implement a disaster recovery strategy that:
. Is cost-effective.
. Reduces the amount of data loss in case of a disaster.
. Enables recovery with the least amount of downtime.
Which of the following disaster recovery strategies best describes what the cloud engineer wants to achieve?
A social networking company operates globally. Some users from Brazil and Argentina are reporting the following error: website address was not found. Which of the following is the most likely cause of this outage?
Five thousand employees always access the company's public cloud-hosted web application on a daily basis during the same time frame. Some users have been reporting performance issues while attempting to connect to the web application Which of the following is the best configuration approach to resolve this issue?
A developer is building an application that has multiple microservices that need to communicate with each other. The developer currently manually updates the IP address of each service. Which of the following best resolves the communication issue and automates the process?
Which of the following is a field of computer science that enables computers to identify and understand objects and people in images and videos?
A developer at a small startup company deployed some code for a new feature to its public repository. A few days later, a data breach occurred. A security team investigated the
incident and found that the database was hacked. Which of the following is the most likely cause of this breach?
A cloud engineer must update the company’s code repository, which is running on a VM, to the latest version. The engineer downloads and runs the latest update, which appears to be successful. Which of the following steps should the engineer take next?