The following commands are configured on the Huawei firewall:
[USG] firewall defend ip-fragment enable
Which of the following situations will be recorded as an offensive behavior? (multiple choice)
Location refers to the end user's use AC-Campus The terminal environment when accessing the controlled network office. Which of the following options is correct for the description of the place?
Regarding intrusion detection I defense equipment, which of the following statements are correct? (multiple choice)
The security management system is only optional, and anti-virus software or anti-hacking technology can be a good defense against network threats.
Visitors refer to users who need temporary access to the network at a specific location.
Regarding the basic principles of user access security, it is wrong not to list any description?
Regarding the description of the logic architecture of the business accompanying, which of the following options is correct?
Portal page push rules have priority, and the rules with higher priority are matched with the user's authentication information first. If none of the configured rules match, The default rules are used.
Security authentication is mainly achieved through security policies. The terminal host support management for the security check of monthly users is mainly realized by loose check policies. End user behavior management is mainly realized by monitoring policies. If users need to formulate policies according to their own wishes, they can use them. Custom strategy.
Use the command on the switch to view the status of free mobility deployment, the command is as follows:
For the above command, which of the following descriptions is correct?
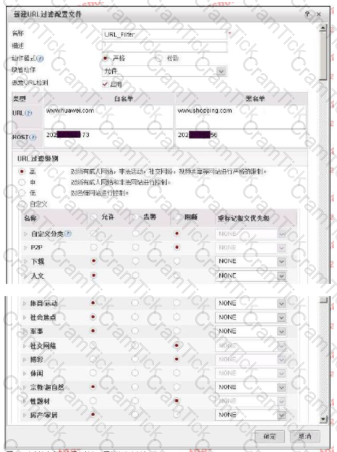
The administrator of a certain enterprise wants employees of Yangzhi to visit the shopping website during working hours. So a URL filtering configuration file is configured to divide the predefined
The shopping website in the category is selected as blocked. But employee A can still use the company's network to shop online during lunch break. Then what are the following possible reasons
some?
There is a three-layer forwarding device between the authentication client and the admission control device:If at this time Portal The certified three-layer authentication device can also obtain the authentication client's MAC address,So you can use IP Address and MC The address serves as the information to identify the user.
An enterprise has a large number of mobile office employees, and a mobile office system needs to be deployed to manage the employees. The number of employees in this enterprise exceeds 2000 People, and the employees’ working areas are distributed all over the country. In order to facilitate management, which deployment method is adopted?
Which of the following options is right PKI The sequence description of the work process is correct?
1. PKI Entity direction CA ask CA Certificate. .
2. PKI Entity received CA After the certificate, install CA Certificate.
3. CA receive PKI Entity CA When requesting a certificate, add your own CA Certificate reply to PKI entity.
4. PKI Entity direction CA Send a certificate registration request message.
5. PKI When the entities communicate with each other, they need to obtain and install the local certificate of the opposite entity.
6. PKI Entity received CA The certificate information sent.
7. PKI After the entity installs the local certificate of the opposite entity,Verify the validity of the local certificate of the peer entity. When the certificate is valid,PC The public key of the certificate is used for encrypted communication between entities.
8. CA receive PKI The entity's certificate registration request message.
Terminal security access technology does not include which of the following options?
Free mobility is a special access control method, according to the user’s access location, access time, access method and terminal authorization instructions. Set permissions, as long as the user’s access conditions remain unchanged, the permissions and network experience after accessing the network--To q
Web Standards that come with the client and operating system 8021 The instrument client only has the function of identity authentication: It does not support the execution of inspection strategies and monitoring strategies. Any Office The client supports all inspection strategies and monitoring strategies.
Which of the following attacks are attacks against web servers? (multiple choices)
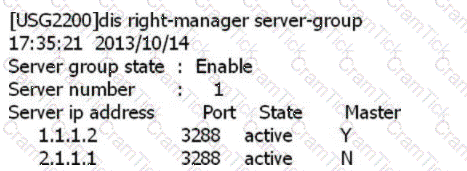
SACG query right-manager information as follows, which options are correct? (Select 2 answers)
If you deploy Free Mobility, in the logic architecture of Free Mobility, which of the following options should be concerned by the administrator?
Traditional network single--The strategy is difficult to cope with the current complex situations such as diversified users, diversified locations, diversified terminals, diversified applications, and insecure experience.
Which of the following is not an abnormal situation of the file type recognition result?
In the campus network, employees can use 802.1X, Portal,MAC Address or SACG Way to access. Use different access methods according to different needs to achieve the purpose of user access control.
Which of the following options is Agile Controller-Campus middle SC The main function of the component?
In a centralized networking, the database, SM server, SC server, and AE server are all centrally installed in the corporate headquarters. This networking method is suitable. It is used for enterprises with a wide geographical distribution of users and a large number of users.
In enterprises where terminal host access control management is relatively strict, administrators hope to bind terminal hosts and accounts to prevent terminal users from accessing the controlled network from unauthorized terminal hosts at will. Regarding the description of binding the terminal host and account, which of the following is correct?
Which of the following options does not belong to the basic DDoS attack prevention configuration process?
Use on access control equipment test-aaa Command test and Radius When the server is connected, the running result shows a timeout, which may be caused by incorrect account or password configuration.
The anti-tampering technology of Huawei WAF products is based on the cache module. Suppose that when user A visits website B, website B has page tampering.
Signs: The workflow for the WAF tamper-proof module has the following steps:.
① WAF uses the pages in the cache to return to the client;
②WAF compares the watermark of the server page content with the page content in the cache
③Store the content of the page in the cache after learning
④ When the user accesses the Web page, the WAF obtains the page content of the server
⑤WAF starts the learning mode to learn the page content of the user's visit to the website;
For the ordering of these steps, which of the following options is correct?
The traditional campus network is based on IP As the core network, if there are mobile office users, which of the following options is not the problem that mobile office users face when deploying access authentication?
Guest management is Agile Controller-Campus Important function of, regarding visitor management, which of the following statements are correct? (Multiple choice)
The relationship between user groups and accounts in user management is stored in a tree on the Agile Controller-Campus. An account belongs to only one user group.
Consistent with the corporate organizational structure: If the OU (OnizbonUnit) structure stored in the AD/LDAP server is consistent with the corporate organizational structure, users are stored Under 0OU, when the Agile Controller-Campus synchronizes AD/LDAP server accounts, which synchronization method can be used?
The following figure shows the configuration of the URL filtering configuration file. Regarding the configuration, which of the following statements is correct?
The user accesses the network through the network access device, and the third-party RADIUS server authenticates and authorizes the user. Regarding the certification process, which of the following options is wrong?
Which of the following options is for Portal The statement of the gateway access process is correct?
Use on the terminal Portal The authentication is connected to the network, but you cannot jump to the authentication page. The possible reason does not include which of the following options?
Mobile smartphone, tablet PC users through Any Office Client and AE Establish IPSec Encrypted tunnel, After passing the certification and compliance check, visit the enterprise business.
Using Agile Controller-Campus for visitor management, users can obtain the account they applied for in a variety of ways, but which of the following are not included A way?
In the big data intelligent security analysis platform, it is necessary to collect data from data sources, and then complete a series of actions such as data processing, detection and analysis, etc.
do. Which of the following options does not belong to the action that needs to be completed in the data processing part?
155955cc-666171a2-20fac832-0c042c0422
Regarding the processing flow of file filtering, which of the following statements is wrong?
The administrator has configured file filtering to prohibit internal employees from uploading development files, but internal employees can still upload development files. Which of the following is not allowed Can the reason?
When a guest needs to access the network through an account, which of the following methods can be used to access? (Multiple choice)
Regarding the strategy for checking the screensaver settings, which of the following descriptions are correct? (Multiple choice)


