You are setting up an HPE Aruba Networking VIA solution for a company. You have already created a VPN pool with IP addresses for the remote clients. During
tests, however, the clients do not receive IP addresses from that pool.
What is one setting to check?
HPE Aruba Networking Central displays a Gateway Threat Count alert in the alert list. How can you gather more information about what caused the alert to trigger?
You are setting up user-based tunneling (UBT) between access layer AOS-CX switches and AOS-10 gateways. You have selected reserved (local) VLAN mode.
Tunneled devices include IoT devices, which should be assigned to:
Roles: iot on the switches and iot-wired on the gateways
VLAN: 64, for which the gateways route traffic.
IoT devices connect to the access layer switches' edge ports, and the access layer switches reach the gateways on their uplinks.
Where must you configure VLAN 64?
A company wants to use the HPE Aruba Networking ClearPass OnGuard agent to assign posture to clients.
How do you define the conditions by which a client receives a particular posture?
A company uses HPE Aruba Networking ClearPass Policy Manager (CPPM) as a TACACS+ server to authenticate managers on its AOS-CX switches. You want
to assign managers to groups on the AOS-CX switch by name.
How do you configure this setting in a CPPM TACACS+ enforcement profile?
HPE Aruba Networking Central displays an alert about an Infrastructure Attack that was detected. You go to the Security > RAPIDS events and see that the attack was "Detect adhoc using Valid SSID." What is one possible next step?
A company has HPE Aruba Networking gateways that implement gateway IDS/IPS. Admins sometimes check the Security Dashboard, but they want a faster way to discover if a gateway starts detecting threats in traffic.
What should they do?
HPE Aruba Networking Central displays an alert about an Infrastructure Attack that was detected. You go to the Security > RAPIDS events and see that the attack
was "Detect adhoc using Valid SSID."
What is one possible next step?
A company has AOS-CX switches and HPE Aruba Networking APs, which run AOS-10 and bridge their SSIDs. Company security policies require 802.1X on all edge ports, some of which connect to APs. How should you configure the auth-mode on AOS-CX switches?
What correctly describes an HPE Aruba Networking AP's Device (TPM) certificate?
You have configured an AOS-CX switch to implement 802.1X on edge ports. Assume ports operate in the default auth-mode. VolP phones are assigned to the
"voice" role and need to send traffic that is tagged for VLAN 12.
Where should you configure VLAN 12?
A company is using HPE Aruba Networking Central SD-WAN Orchestrator to establish a hub-spoke VPN between branch gateways (BGWs) at 1444 site and
VPNCs at multiple data centers.
What is part of the configuration that admins need to complete?
Refer to Exhibit.
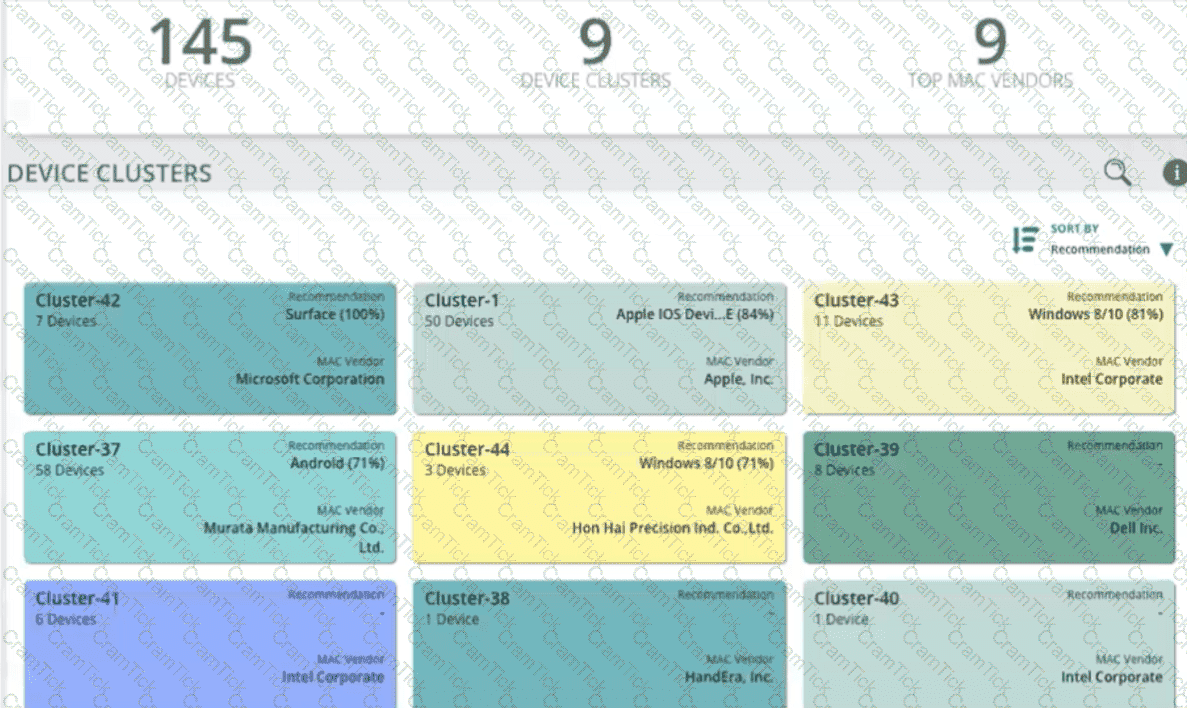
A company is using HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application). In the CPDI interface, you go to the Generic Devices
page and see the view shown in the exhibit.
What correctly describes what you see?
What role can Internet Key Exchange (IKE)/IKEv2 play in an HPE Aruba Networking client-to-site VPN?
You manage AOS-10 APs with HPE Aruba Networking Central. A role is configured on these APs with these rules (in order):
Allow UDP on port 67 to any destination
Allow any to network 10.1.4.0/23
Deny any to network 10.1.0.0/18 + log
Deny any to network 10.0.0.0/8
Allow any to any destination
You add this new rule immediately before rule 4:
Deny SSH to network 10.1.0.0/21 + denylist
After this change, what happens when a client assigned to this role sends SSH traffic to 10.1.7.12?
A company uses HPE Aruba Networking ClearPass Policy Manager (CPPM) as a TACACS+ server to authenticate managers on its AOS-CX switches. The company wants CPPM to control which commands managers are allowed to enter.
Which service must you add to the managers' TACACS+ enforcement profile?
A company uses HPE Aruba Networking ClearPass Policy Manager (CPPM) and HPE Aruba Networking ClearPass Device Insight (CPDI) and has integrated the
two. CPDI admins have created a tag. CPPM admins have created rules that use that tag in the wired 802.1X and wireless 802.1X services' enforcement policies.
The company requires CPPM to apply the tag-based rules to a client directly after it learns that the client has that tag.
What is one of the settings that you should verify on CPPM?
You are establishing a cluster of HPE Aruba Networking ClearPass servers. (Assume that they are running version 6.9.).
For which type of certificate is it recommended to install a CA-signed certificate on the Subscriber before it joins the cluster?
A company wants you to integrate HPE Aruba Networking ClearPass Policy Manager (CPPM) with HPE Aruba Networking ClearPass Device Insight (CPDI).
What is one aspect of the integration that you should explain?
A company assigns a different block of VLAN IDs to each of its access layer AOS-CX switches. The switches run version 10.07. The IDs are used for standard
purposes, such as for employees, VolP phones, and cameras. The company wants to apply 802.1X authentication to HPE Aruba Networking ClearPass Policy
Manager (CPPM) and then steer clients to the correct VLANs for local forwarding.
What can you do to simplify setting up this solution?
You have set up a mirroring session between an AOS-CX switch and a management station, running Wireshark. You want to capture just the traffic sent in the
mirroring session, not the management station's other traffic.
What should you do?
Refer to Exhibit:

All of the switches in the exhibit are AOS-CX switches.
What is the preferred configuration on Switch-2 for preventing rogue OSPF routers in this network?
HPE Aruba Networking ClearPass Device Insight (CPDI) could not classify some endpoints using system and user rules. Using machine learning, it did assign those endpoints to a cluster and discover a recommendation. In which of these circumstances does CPDI automatically classify the endpoints based on that recommendation?
What is one use case that companies can fulfill using HPE Aruba Networking ClearPass Policy Manager's (CPPM's) Device Profiler?
A company wants to use HPE Aruba Networking ClearPass Policy Manager (CPPM) to profile Linux devices. You have decided to schedule a subnet scan of the devices' subnets. Which additional step should you complete before scheduling the scan?
A company has HPE Aruba Networking APs and AOS-CX switches. The APs bridge wireless traffic. They receive DHCP IP addresses on VLAN 18. Wireless users are assigned to VLAN 12.
The company wants the APs to start using 802.1X authentication on their switch ports. You are configuring the port-access role to which the APs are assigned after authentication.
What is one recommended setting for that role?
Assume that an AOS-CX switch is already implementing DHCP snooping and ARP inspection successfully on several VLANs.
What should you do to help minimize disruption time if the switch reboots?
A ClearPass Policy Manager (CPPM) service includes these settings:
Role Mapping Policy:
Evaluate: Select first
Rule 1 conditions:
Authorization:AD:Groups EQUALS Managers
Authentication:TEAP-Method-1-Status EQUALS Success
Rule 1 role: manager
Rule 2 conditions:
Authentication:TEAP-Method-1-Status EQUALS Success
Rule 2 role: domain-comp
Default role: [Other]
Enforcement Policy:
Evaluate: Select first
Rule 1 conditions:
Tips Role EQUALS manager AND Tips Role EQUALS domain-comp
Rule 1 profile list: domain-manager
Rule 2 conditions:
Tips Role EQUALS manager
Rule 2 profile list: manager-only
Rule 3 conditions:
Tips Role EQUALS domain-comp
Rule 3 profile list: domain-only
Default profile: [Deny access]
A client is authenticated by the service. CPPM collects attributes indicating that the user is in the Contractors group, and the client passed both TEAP methods.
Which enforcement policy will be applied?
A company has HPE Aruba Networking APs running AOS-10 that connect to AOS-CX switches. The APs will:
. Authenticate as 802.1X supplicants to HPE Aruba Networking ClearPass Policy Manager (CPPM)
. Be assigned to the "APs" role on the switches
. Have their traffic forwarded locally
What information do you need to help you determine the VLAN settings for the "APs" role?
A company has AOS-CX switches and HPE Aruba Networking ClearPass Policy Manager (CPPM). The company wants switches to implement 802.1X authentication to CPPM and download user roles. What is one task that you must complete on CPPM to support this use case?
A company wants to apply a standard configuration to all AOS-CX switch ports and have the ports dynamically adjust their configuration based on the identity of
the user or device that connects. They want to centralize configuration of the identity-based settings as much as possible.
What should you recommend?
A company has HPE Aruba Networking APs (AOS-10), which authenticate clients to HPE Aruba Networking ClearPass Policy Manager (CPPM). CPPM is set up
to receive a variety of information about clients' profile and posture. New information can mean that CPPM should change a client's enforcement profile.
What should you set up on the APs to help the solution function correctly?
An admin has configured an AOS-CX switch with these settings:
port-access role employees
vlan access name employees
This switch is also configured with CPPM as its RADIUS server.
Which enforcement profile should you configure on CPPM to work with this configuration?
What is one use case for implementing user-based tunneling (UBT) on AOS-CX switches?
A company uses both HPE Aruba Networking ClearPass Policy Manager (CPPM) and HPE Aruba Networking ClearPass Device Insight (CPDI). What is one way integrating the two solutions can help the company implement Zero Trust Security?
Refer to the Exhibit:

These packets have been captured from VLAN 10. which supports clients that receive their IP addresses with DHCP.
What can you interpret from the packets that you see here?
These packets have been captured from VLAN 10, which supports clients that receive their IP addresses with DHCP. What can you interpret from the packets that you see here?
ACNSP |


