What does the abbreviation CSMS round in ISA 62443-2-1 represent?
Available Choices (select all choices that are correct)
Which steps are part of implementing countermeasures?
Available Choices (select all choices that are correct)
A manufacturing plant has inconsistent cybersecurity processes that vary widely between shifts and teams. According to the maturity levels described in ISA/IEC 62443-2-1, how would this situation be classified?
Which Security Level (SL) would be MOST appropriate for a system that requires protection against attackers with high motivation and extended resources using sophisticated means?
Which of the following PRIMARILY determines access privileges for user accounts?
Available Choices (select all choices that are correct)
Which is the implementation of PROFIBUS over Ethernet for non-safety-related communications?
Available Choices (select all choices that are correct)
Which is the PRIMARY responsibility of the network layer of the Open Systems Interconnection (OSI) model?
Available Choices (select all choices that are correct)
What programs are MOST effective if they are tailored to the audience, consistent with company policy, and communicated regularly?
What programs are MOST effective if they are tailored to the audience, consistent with company policy, and communicated regularly?
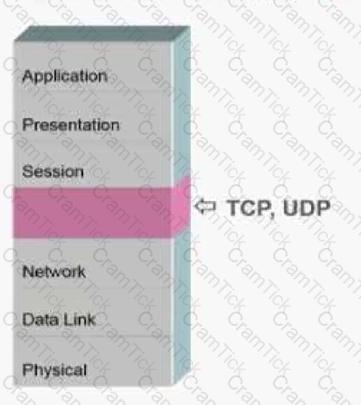
At Layer 4 of the Open Systems Interconnection (OSI) model, what identifies the application that will handle a packet inside a host?
Available Choices (select all choices that are correct)
Why is it important for the asset owner to incorporate the IACS into its organization and security program during the Operation and Maintenance phase?
What are the two sublayers of Layer 2?
Available Choices (select all choices that are correct)
Which U.S. Department is responsible for the Chemical Facility Anti-Terrorism Standards (CFATS)?
Who is responsible for defining the tolerable residual cybersecurity risk as an input requirement for all activities?
Which of the following attacks relies on a human weakness to succeed?
Available Choices (select all choices that are correct)
What does Layer 1 of the ISO/OSI protocol stack provide?
Available Choices (select all choices that are correct)
What is the name of the missing layer in the Open Systems Interconnection (OSI) model shown below?
Which standard focuses on protecting sensitive information across all organizational systems through a broad Information Security Management System (ISMS)?
Which steps are included in the ISA/IEC 62443 assess phase?
Available Choices (select all choices that are correct)
In which layer is the physical address assigned?
Available Choices (select all choices that are correct)
What is the PRIMARY goal of the IACS Security Program (SP) requirements according to ISA/IEC 62443-2-1?
Which type of cryptographic algorithms requires more than one key?
Available Choices (select all choices that are correct)
To which category of the ISA-62443 (IEC 62443) series does the document titled "Patch management in the IACS environment" belong?
Which of the following is an element of security policy, organization, and awareness?
Available Choices (select all choices that are correct)
Which is the PRIMARY objective when defining a security zone?
Available Choices (select all choices that are correct)
How many element groups are in the "Addressing Risk" CSMS category?
Available Choices (select all choices that are correct)
Which part of the ISA/IEC 62443 series describes a methodology to develop quantitative metrics?
If an asset owner wants to improve their organization’s ability to respond during a cyberattack, which of the following activities would be MOST appropriate to implement?
What is the name of the protocol that implements serial Modbus over Ethernet?
Available Choices (select all choices that are correct)
In an IACS system, a typical security conduit consists of which of the following assets?
Which statement is TRUE reqardinq application of patches in an IACS environment?
Available Choices (select all choices that are correct)
During the operation of an IACS, who is responsible for executing the Security Protection Scheme (SPS) process measures and responding to emerging risks?
Which of the following refers to internal rules that govern how an organization protects critical system resources?
Available Choices (select all choices that are correct)
What is the FIRST step required in implementing ISO 27001?
Available Choices (select all choices that are correct)
An industrial control system requires strong protection against intentional violations using sophisticated means and moderate skills. According to the Security Level (SL) definitions, which SL should be targeted?
Which of the following staff is NOT mentioned as a stakeholder in the CSMS Program?
A company needs to create a standardized interface for exchanging real-time plant data between heterogeneous control devices while maintaining a structured organization of data elements such as folders, classes, and methods. Which feature of OPC supports this requirement?
Why is segmentation from non-IACS zones important in Network & Communication Security (SP Element 3)?
A company discovers malware on a portable USB device used within their IACS environment. According to the document, which SP Element and controls would be MOST relevant to address this issue?
Which of the following provides the overall conceptual basis in the design of an appropriate security program?
Available Choices (select all choices that are correct)
Which is NOT a potential consequence for organizations that fail to prioritize control system security?
Which of the following is an element of monitoring and improving a CSMS?
Available Choices (select all choices that are correct)
How many security levels are in the ISASecure certification program?
Available Choices (select all choices that are correct)
Which is the BEST deployment system for malicious code protection?
Available Choices (select all choices that are correct)
Which of the following is an activity that should trigger a review of the CSMS?
Available Choices (select all choices that are correct)
What is the name of the missing layer in the Open Systems Interconnection (OSI) model shown below?
How does ISA-62443-2-1 suggest integrating the IACS Security Program (SP) within an organization?
If an asset owner wants to demonstrate compliance with ISA/IEC 62443-2-1 requirements during an external audit, which type of evidence would be MOST appropriate?
In a defense-in-depth strategy, what is the purpose of role-based access control?
Available Choices (select all choices that are correct)
A company is developing an automation solution and wants to align its cybersecurity efforts with ISA/IEC 62443 standards. Which lifecycle phases should be integrated into their project plan to cover both security and automation solution security comprehensively?
What does the System under Consideration (SuC) include in the context of ISA/IEC 62443 risk assessment?
Which policies and procedures publication is titled Patch Manaqement in the IACS Environment?
Available Choices (select all choices that are correct)
Which organization manages the ISASecure conformance certification program?
Available Choices (select all choices that are correct)


