A Mule application exposes an HTTPS endpoint and is deployed to the CloudHub Shared Worker Cloud. All traffic to that Mule application must stay inside the AWS VPC.
To what TCP port do API invocations to that Mule application need to be sent?
An organization wants MuleSoft-hosted runtime plane features (such as HTTP load balancing, zero downtime, and horizontal and vertical scaling) in its Azure environment. What runtime plane minimizes the organization's effort to achieve these features?
Question 10: Skipped
An API implementation returns three X-RateLimit-* HTTP response headers to a requesting API client. What type of information do these response headers indicate to the API client?
In an organization, the InfoSec team is investigating Anypoint Platform related data traffic.
From where does most of the data available to Anypoint Platform for monitoring and alerting originate?
A company uses a hybrid Anypoint Platform deployment model that combines the EU control plane with customer-hosted Mule runtimes. After successfully testing a Mule API implementation in the Staging environment, the Mule API implementation is set with environment-specific properties and must be promoted to the Production environment. What is a way that MuleSoft recommends to configure the Mule API implementation and automate its promotion to the Production environment?
Refer to the exhibit.
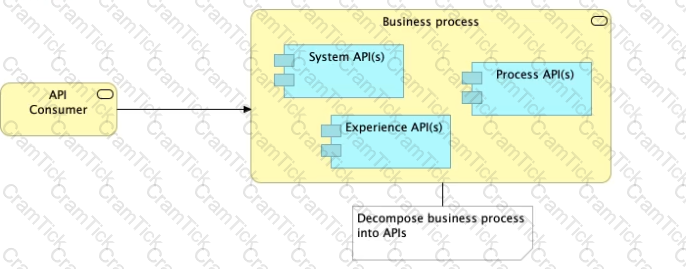
What is the best way to decompose one end-to-end business process into a collaboration of Experience, Process, and System APIs?
A) Handle customizations for the end-user application at the Process API level rather than the Experience API level
B)Allow System APIs to return data that is NOT currently required by the identified Process or Experience APIs
C)Always use a tiered approach by creating exactly one API for each of the 3 layers (Experience, Process and System APIs)

D)Use a Process API to orchestrate calls to multiple System APIs, but NOT to other Process APIs
What is the main change to the IT operating model that MuleSoft recommends to organizations to improve innovation and clock speed?
A company has started to create an application network and is now planning to implement a Center for Enablement (C4E) organizational model. What key factor would lead the company to decide upon a federated rather than a centralized C4E?
An API implementation is updated. When must the RAML definition of the API also be updated?
An organization has implemented a Customer Address API to retrieve customer address information. This API has been deployed to multiple environments and has been configured to enforce client IDs everywhere.
A developer is writing a client application to allow a user to update their address. The developer has found the Customer Address API in Anypoint Exchange and wants to use it in their client application.
What step of gaining access to the API can be performed automatically by Anypoint Platform?
How can the application of a rate limiting API policy be accurately reflected in the RAML definition of an API?
What Mule application deployment scenario requires using Anypoint Platform Private Cloud Edition or Anypoint Platform for Pivotal Cloud Foundry?
Which of the below, when used together, makes the IT Operational Model effective?
Refer to the exhibit.
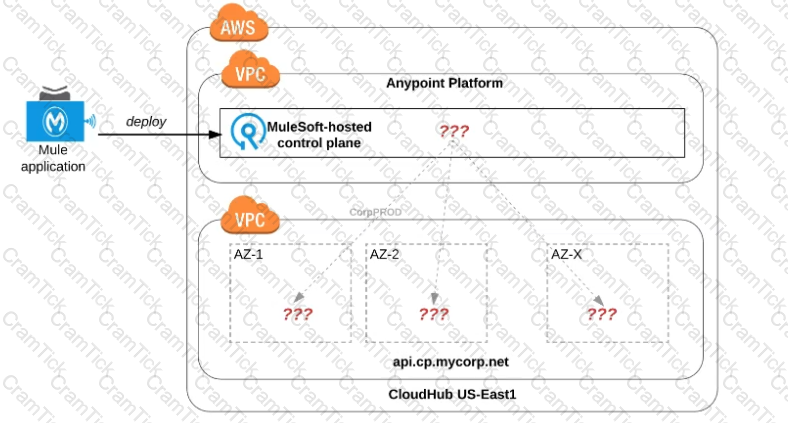
An organization uses one specific CloudHub (AWS) region for all CloudHub deployments.
How are CloudHub workers assigned to availability zones (AZs) when the organization's Mule applications are deployed to CloudHub in that region?
What Mule application can have API policies applied by
Anypoint Platform to the endpoint exposed by that Mule application?
A)A Mule application that accepts requests over HTTP/1.x

B)A Mule application that accepts JSON requests over TCP but is NOT required to provide a response
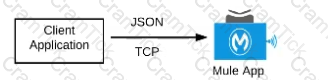
C)A Mute application that accepts JSON requests over WebSocket

D)A Mule application that accepts gRPC requests over HTTP/2

An organization has several APIs that accept JSON data over HTTP POST. The APIs are all publicly available and are associated with several mobile applications and web applications.
The organization does NOT want to use any authentication or compliance policies for these APIs, but at the same time, is worried that some bad actor could send payloads that could somehow compromise the applications or servers running the API implementations.
What out-of-the-box Anypoint Platform policy can address exposure to this threat?
A new upstream API Is being designed to offer an SLA of 500 ms median and 800 ms maximum (99th percentile) response time. The corresponding API implementation needs to sequentially invoke 3 downstream APIs of very similar complexity.
The first of these downstream APIs offers the following SLA for its response time: median: 100 ms, 80th percentile: 500 ms, 95th percentile: 1000 ms.
If possible, how can a timeout be set in the upstream API for the invocation of the first downstream API to meet the new upstream API's desired SLA?
What best describes the Fully Qualified Domain Names (FQDNs), also known as DNS entries, created when a Mule application is deployed to the CloudHub Shared Worker Cloud?
Refer to the exhibit.
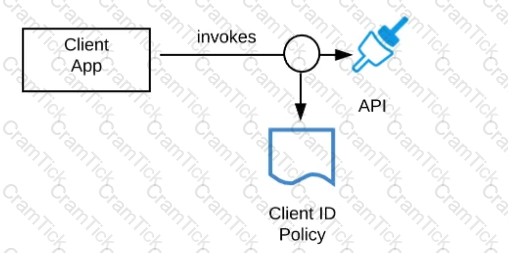
A developer is building a client application to invoke an API deployed to the STAGING environment that is governed by a client ID enforcement policy.
What is required to successfully invoke the API?
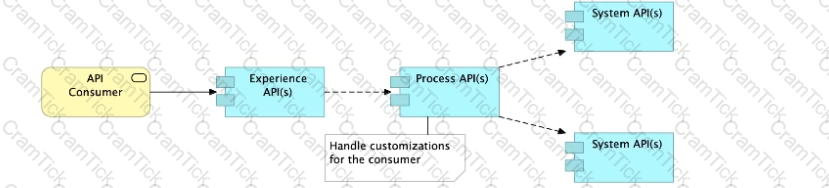
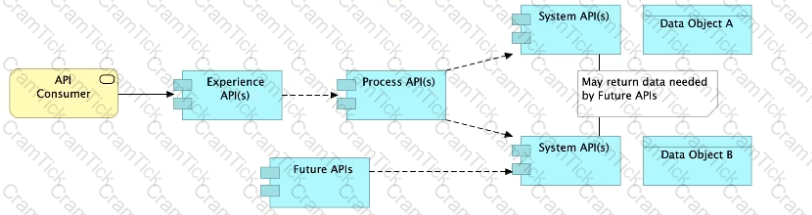
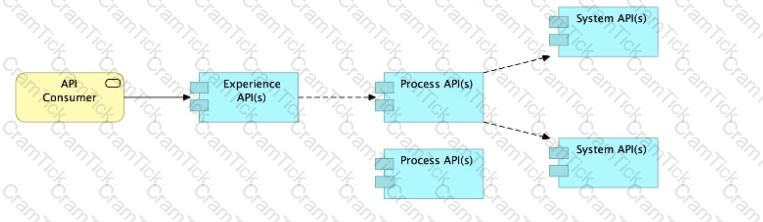
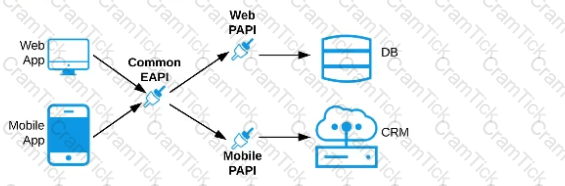
Refer to the exhibit. An organization needs to enable access to their customer data from both a mobile app and a web application, which each need access to common fields as well as certain unique fields.
The data is available partially in a database and partially in a 3rd-party CRM system.
What APIs should be created to best fit these design requirements?
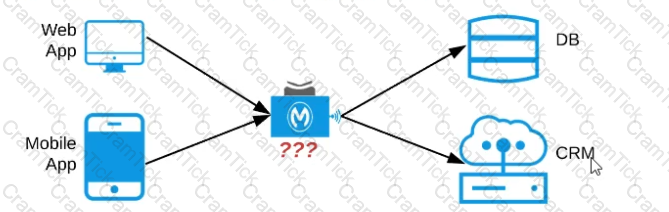
A)A Process API that contains the data required by both the web and mobile apps, allowing these applications to invoke it directly and access the data they need thereby providing the flexibility to add more fields in the future without needing API changes

B)One set of APIs (Experience API, Process API, and System API) for the web app, and another set for the mobile app
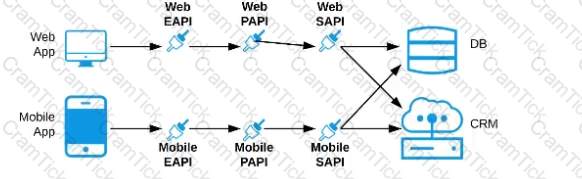
C)Separate Experience APIs for the mobile and web app, but a common Process API that invokes separate System APIs created for the database and CRM system
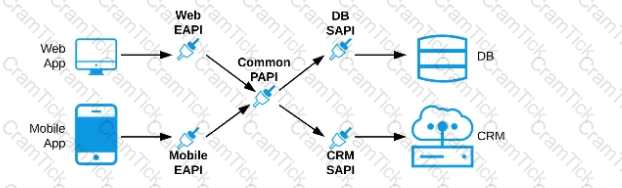
D)A common Experience API used by both the web and mobile apps, but separate Process APIs for the web and mobile apps that interact with the database and the CRM System
An organization is deploying their new implementation of the OrderStatus System API to multiple workers in CloudHub. This API fronts the organization's on-premises Order Management System, which is accessed by the API implementation over an IPsec tunnel.
What type of error typically does NOT result in a service outage of the OrderStatus System API?
What is most likely NOT a characteristic of an integration test for a REST API implementation?
MuleSoft Certified Platform Architect | MCPA-Level-1 Questions Answers | MCPA-Level-1 Test Prep | MuleSoft Certified Platform Architect - Level 1 Questions PDF | MCPA-Level-1 Online Exam | MCPA-Level-1 Practice Test | MCPA-Level-1 PDF | MCPA-Level-1 Test Questions | MCPA-Level-1 Study Material | MCPA-Level-1 Exam Preparation | MCPA-Level-1 Valid Dumps | MCPA-Level-1 Real Questions | MuleSoft Certified Platform Architect MCPA-Level-1 Exam Questions


