Which task Is mandatory when provisioning a device through the plug-and-play workflow in Cisco DNA Center?
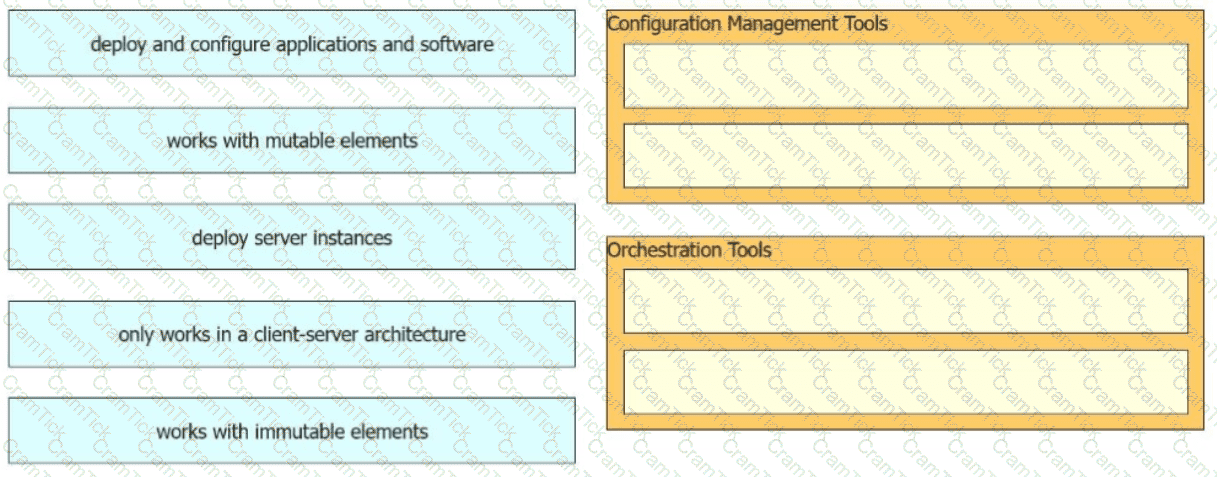
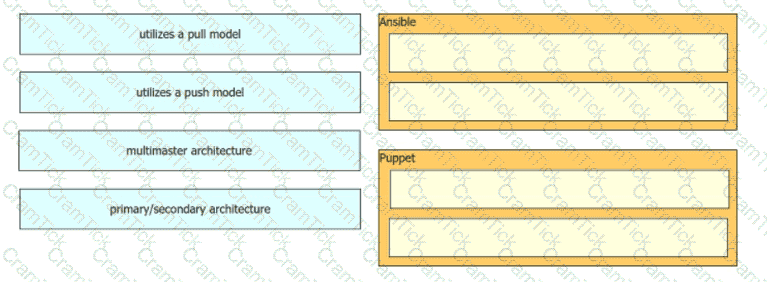
Drag and drop the characteristics from the left onto the tools on the right. Not all options are used.
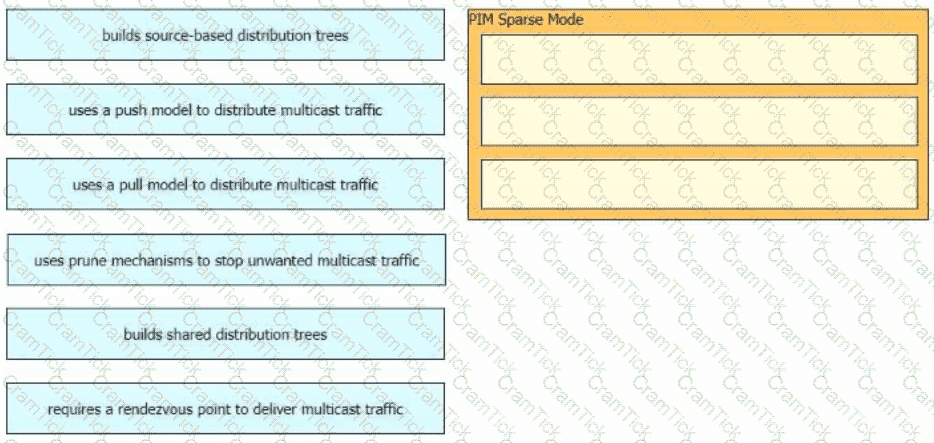
Drag and drop the characteristics of PIM Sparse Mode from the left to the right. Not all options are used.
In a Cisco SD-Access solution, which protocol is used by an extended node to connect to a single edge node?
Which design principle states that a user has no access by default to any resource, and unless a resource is explicitly granted, it should be denied?
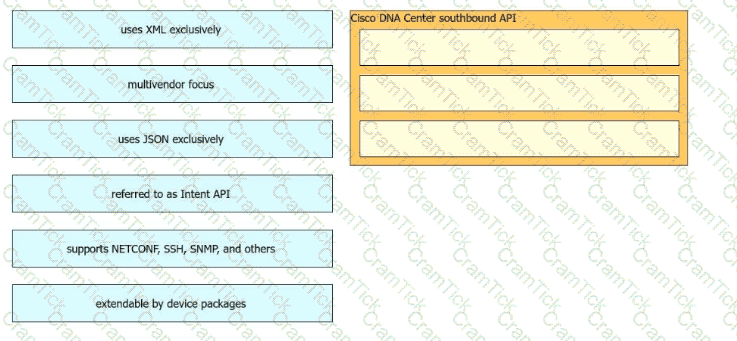
Drag and drop the Cisco Catalyst Center (formerly DNA Center) southbound API characteristics from the left to the right. Not all options are used.
An engineer must configure a new 6 Ghz only SSID on a cisco catalyst 9800 series WLC, with these requirements:
Provide 802.11ax data rates for supported devices
All users authenticate using a certificate
Which wireless layer 2 security mode meets the requirements?
Which method is used by an AP to join HA controllers and is configured in NVRAM?
In Cisco CatalystCenter(formerly DNA Center) Inventory, the Software Version of a networkdevice displays a status of OUTDATED. What does It me?
Which component of the Cisco Cyber Threat Defense solution provides user and flow context analysis?
Which two southbound interfaces originate from Cisco Catalyst Center (formerly DNA Center) and terminate at fabric underlay switches'? (Choose two.)
Which LISP device is responsible for publishing EID-to-RLOC mappings for a site?
A company recently decided to use RESTCONF instead of NETCONF. and many of their NETCONF scripts contain the operation
Refer to the exhibit. An engineer must create a script that appends the output of the show process cpu sorted command to a file.
Which AP mode allows administrators to generate pcap files to use for troubleshooting?
Which two Cisco SD-Access components provide communication between traditional network elements and the controller layer? (Choose two.)
Drag and drop the characteristics from the left onto the orchestration tools they describe on the right.
Which protocol does Cisco Catalyst SD-WAN use to protect control plane communication?
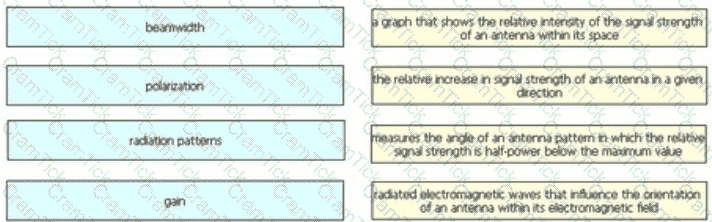
Drag and drop the wireless elements on the left to their definitions on the right.
Which mechanism is used to protect the confidentiality of sensitive information exchanged over REST APIs?
What is a characteristic of the Cisco Catalyst Center (formerly DNA Center) Template Editor feature?
What is used to validate the authenticity of the client and is sent in HTTP requests as a JSON object?
A system must validate access rights to all its resources and must not rely on a cached permission matrix. If the access level to a given resource is revoked but is not reflected in the permission matrix, the security is violates Which term refers to this REST security design principle?
Which two actions are recommended as security best practices to protect REST API? (Choose two.)
Which language defines the structure or modeling of data for NETCONF and RESTCONF?
Which RF value represents the decline of the RF signal amplitude over a given distance"?
When deploying Cisco SD-Access Fabric APs, where does the data plane VXLAN tunnel terminate?
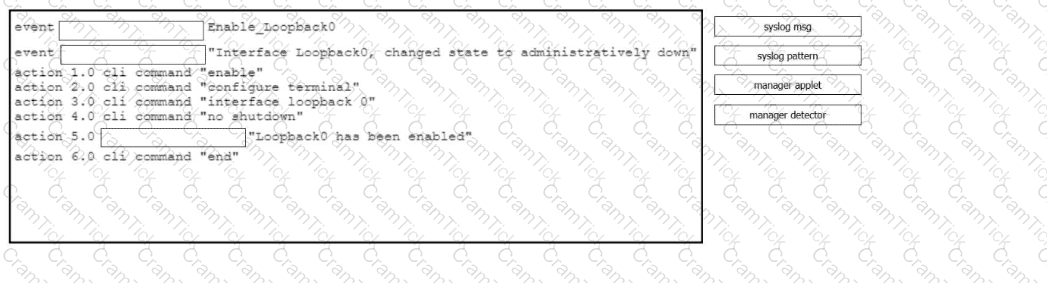
Drag and drop the command snippets from the right onto the blanks in the configuration to create an EEM applet that will enable interface Loopback0 and log a message when the logging message -Interface Loopback0. changed state to administratively down" is received. Not all commands are used.
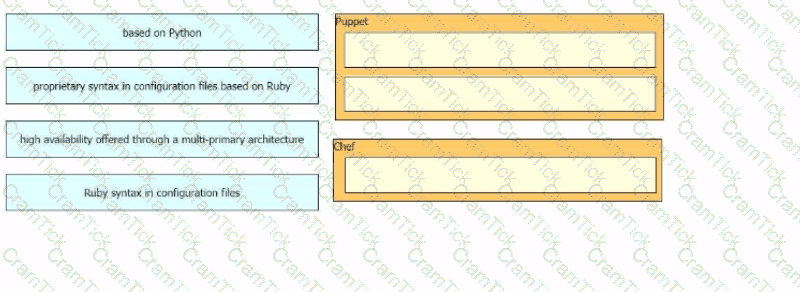
Drag and drop the automation characteristics from the left onto the corresponding tools on the right. Not all options are used.
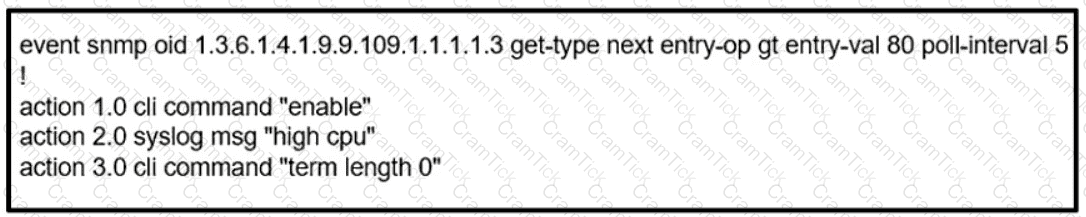
Refer to the exhibit.

An engineer must modify the access control list EGRESS to allow all IP traffic from subnet 10.1.10.0/24 to 10.1.2.0/24. The access control list is applied in the outbound direction on router interface GigabitEthemet 0/1. Which configuration commands can the engineer use to allow this traffic without disrupting existing traffic flows?
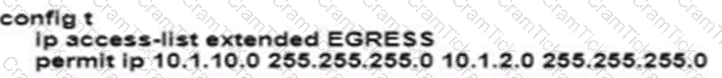
A)
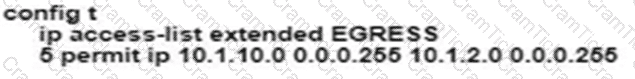
B)
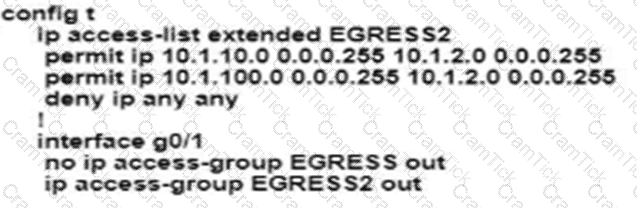
C)
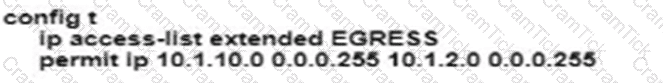
D)
What does a next-generation firewall that is deployed at the data center protect against?
In a fabric-enabled wireless network, which device is responsible for maintaining the endpoint ID database?
A customer has several small branches and wants to deploy a Wi-Fi solution with local management using CAPWAP. Which deployment model meets this requirement?
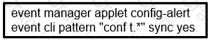
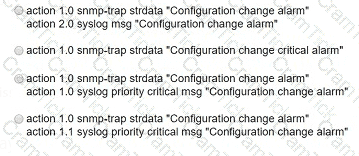
Refer to the exhibit. A network engineer must be notified when a user switches to configuration mode. Which script should be applied to receive an SNMP trap and a critical-level log message?
CCNP Enterprise | 350-401 Written Exam | 350-401 Questions Answers | 350-401 Test Prep | 350-401 CCNP Enterprise Actual Questions | Implementing Cisco Enterprise Network Core Technologies (ENCOR) Exam Questions PDF | 350-401 Online Exam | 350-401 Practice Test | 350-401 PDF | 350-401 CCNP Enterprise Dumps | 350-401 Test Questions | 350-401 Study Material | 350-401 Exam Preparation | 350-401 Valid Dumps | 350-401 Real Questions | 350-401 CCNP Enterprise Practice Test | CCNP Enterprise 350-401 Dumps | Implementing Cisco Enterprise Network Core Technologies (ENCOR) Exam Questions


