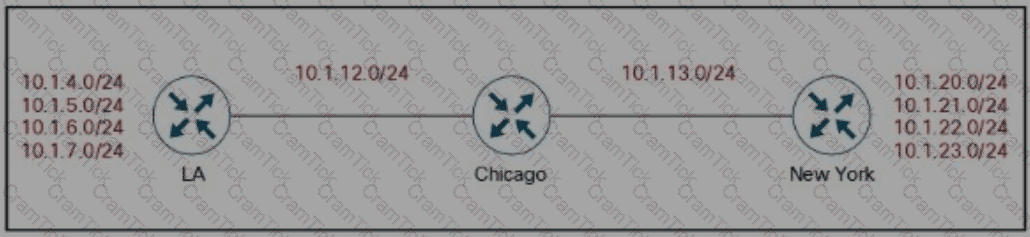
Refer lo the exhibit Company XYZ BGP topology is as shown in the diagram The interface on the LA router connected toward the 10 1 5 0/24 network is faulty and is going up and down, which affects the entre routing domain Which routing technique can be used in the routing policy design so that the rest of the network is not affected by the flapping issue ?
In a multi-cloud environment, which two practices should be implemented to safeguard the integrity of Al-driven network decisions? (Choose two.)
In traditional network design, the network and data center are confined within a single building In this configuration, a router connects the internal and external networks Basic configuration of an access control list within the router controls the traffic that can pass through Which security technique defines the boundary between an internal/trusted network and an external/untrusted network?
Network designers often segment networks by creating modules for various reasons Sometimes however a network can be unintentionally segmented For instance, if the only way to connect a remote site to a headquarters or regional site is to connect them both to the public Internet the corporate network is now unintentionally segmented Which of the following option can be used to desegment the network in this situation?
An engineer must redesign the QoS strategy for Company XYZ The current network is experiencing many dropped packets due to oversubscription of the guaranteed bandwidth allocated by the service provider Company XYZ wants a design with a QoS strategy that controls the traffic flow leaving the Edge router to minimize packet drops Which QoS technique can be recommended as a solution?
In the case of outsourced IT services, the RTO is defined within the SLA Which two support terms are often included in the SLA by IT and other service providers’ (Choose two)
Implementing a network automation architecture usually follows a phased approach that increases automation as the new technology and processes in the preceding phases are integrated and adopted. What provides a model that greatly simplifies the interaction with network devices?
A customer has a functional requirement that states HR systems within a data center must be segmented from other systems that reside in the same data center and same VLAN The systems run legacy applications by using hard-coded IP addresses with all HR systems dedicated to 129 to 254 of the 10 20.20 0/24 prefix Which segmentation method is optimal for the customer?
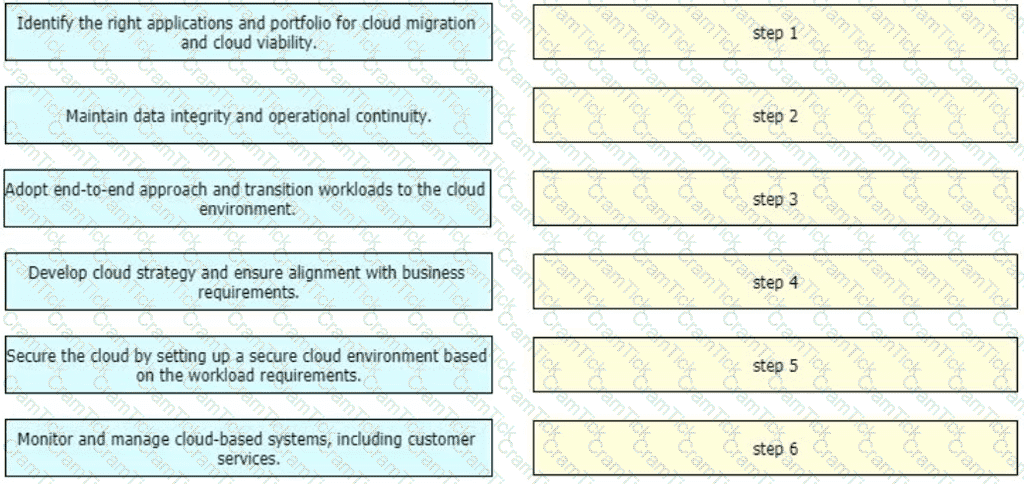
An enterprise wants to migrate an on-premises network to a cloud network, and the design team is finalizing the overall migration process. Drag and drop the options from the left into the correct order on the right.
Which interface between the controller and the networking device enables the two to communicate and allows the controller to program the data plane forwarding tables of the networking device?
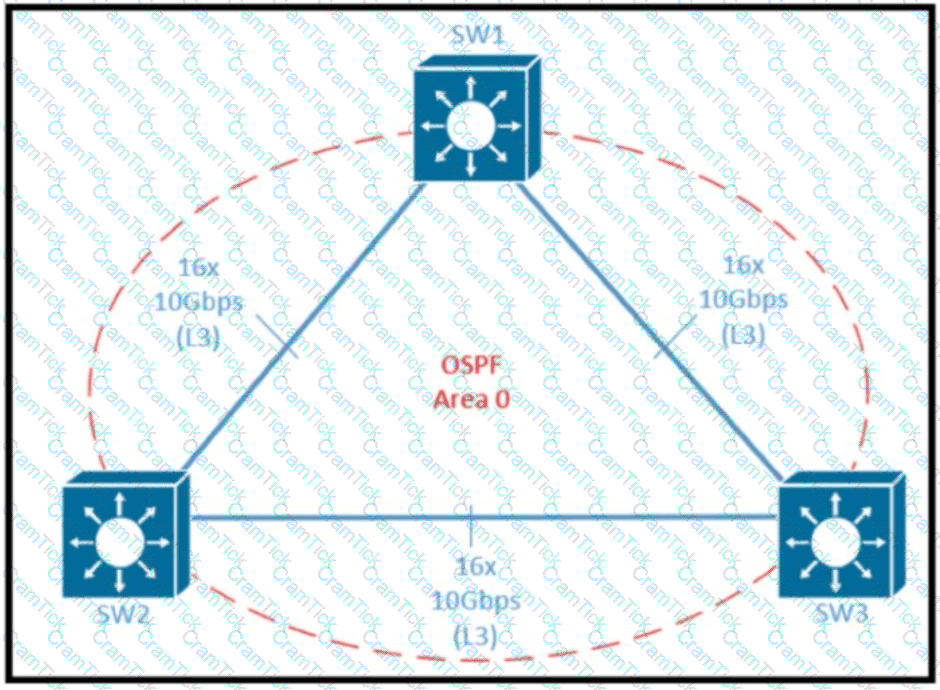
Refer to the exhibit Which two design options reduce the size of OSPF database in the shown topology? (Choose two.)
The PaaS model provides customers with a virtualized application development platform without the need for them to furnish hardware or system administration using in-house resources All necessary infrastructure components and application development services are provided and managed by the cloud service provider. Which limitation should be considered when selecting PaaS model?
A global e-commerce company is expanding its operations and planning to migrate its entire infrastructure to a hybrid cloud solution. They are concerned about data governance and want to ensure that their customers ' data is treated with utmost respect to sovereignty and privacy. What is an appropriate approach?
A multinational enterprise integrates a cloud solution with these objectives
Achieve seamless connectivity across different countries and regions
Extend data center and private clouds into public clouds and provider-hosted clouds
What are two outcomes of deploying data centers and fabrics that interconnect different cloud networks? (Choose two)
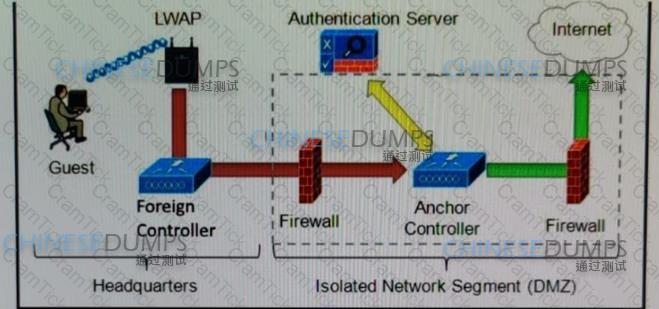
Refer to the diagram. Which solution must be used to send traffic from the foreign wireless LAN controller to the anchor wireless LAN controller?
Compared to data plane traffic, control plane traffic is relatively small in volume, but these flows are critical to the overall functioning of the network infrastructure and to voice and video endpoint well. When designing a QoS policy for a network, which two actions for the network control service-class is recommended? (Choose two)
Company XYZ wants to use the FCAPS ISO standard for network management design. The focus of the design should be to minimize network outages by employing a set of procedures and activities to detect and isolate network issues and the appropriate corrective actions to overcome current issues and prevent them from occurring again. Which layer accomplishes this design requirement?
Company XYZ has implemented policy-based routing in their network. Which potential problem must be kept in mind about network reconvergence and PBR?
A multinational corporation intends to deploy Al/ML-driven analytics for consumer data The company operates in multiple locations, including the EU, where data protection regulations are rigorous The organization must guarantee that its Al/ML solution adheres to local regulations, especially with data storage and processing
Which cloud environment will most effectively meet the company’s data sovereignty needs while assuring adherence to regional data protection regulations?
An external edge router provides connectivity from a service provider to an enterprise Which two Internet edge best practices meet compliance regulations? (Choose two.)
multinational corporation with offices in various regions worldwide are looking for a network architecture that provides a balance between low- latency and cost-effectiveness for connecting their offices to the cloud. Which cloud connectivity option is the best fit for this corporation?
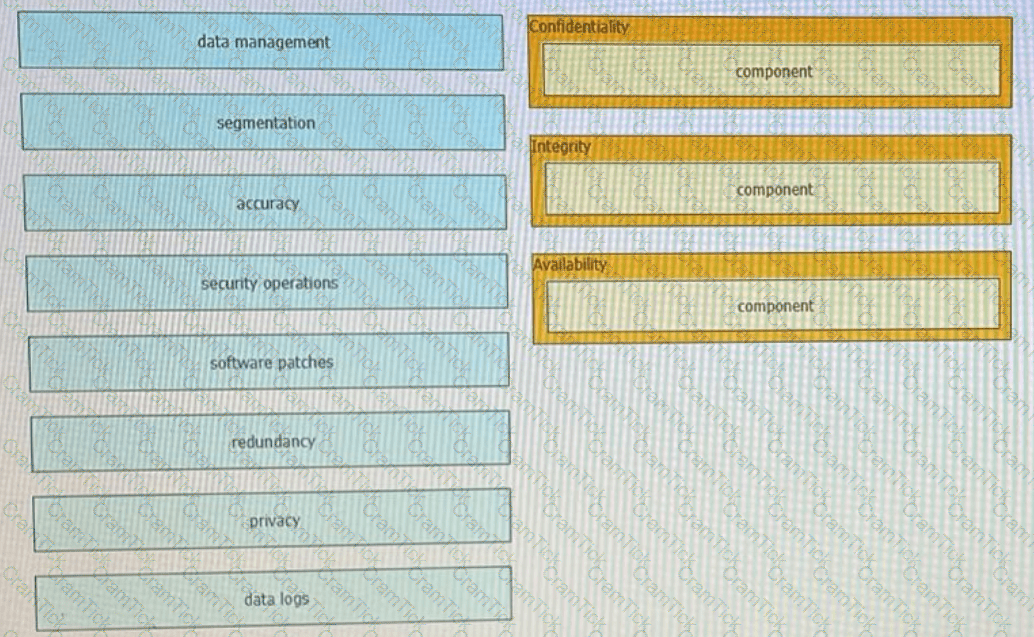
Drag t he components that are part of the CIA triad to the correct target on the right. Not all components are used.
An enterprise service provider is planning to migrate the customer network to MPLS to connect cloud applications The customer network team and service provider team are analyzing all process (tows before live migration and implementation Before planning the migration, what is a crucial task that must be executed?
When planning their cloud migration journey what is crucial for virtually all organizations to perform?
What are two reasons for a company to prefer a hybrid approach rather than a mixed approach while transitioning to a software-defined network? (Choose two.)
Company XYZ is designing the network for IPv6 security and they have these design
requirements:
A switch or router must deny access to traffic from sources with addresses that are correct, but are topologically incorrect
Devices must block Neighbor Discovery Protocol resolution for destination addresses that are not found in the binding table.
Which two IPv4 security features are recommended for this company? (Choose two)
Which two statements describe the functionality of OSPF packet-pacing timers? (Choose two )
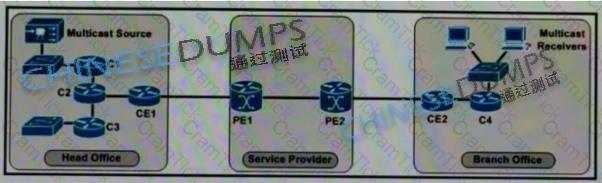
Refer to the exhibit. The enterprise customer wants to stream one-way video from their head office to eight branch offices using multicast. Their current service provider provides a Layer3 VPN solution and manages the CE routers, but they do not currently support multicast. Which solution quickly allows this multicast traffic to go through while allowing for future scalability?
With virtualization being applied in many parts of the network, every physical link is likely to carry one or more virtual links, but what is a drawback in cases like this?
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)
A company with an existing multivendor network is moving from 1 G dark fiber to an ISP virtual leased-line solution The company ' s internal security policy states that any traffic traversing a network that is not owned by the company must be encrypted What must be used to meet the requirements?
A software-defined network can be defined as a network with an API that allows applications to understand and react to the state of the network in near real time A vendor is building an SDN solution that exposes an API to the RIB and potentially the forwarding engine directly The solution provides off-box processes with the capability to interact with the routing table in the same way as a distributed routing process Which SDN framework model does the solution use?
If the desire is to connect virtual network functions together to accommodate different types of
network service connectivity, what must be deployed?
SDN is still maturing Throughout the evolution of SDN which two things will play a key role in enabling a successful deployment and avoiding performance visibility gaps in the infrastructure’ (Choose two.)
A network architect is working on a large project involving migration to a software-defined networking platform, and is currently working on writing an executive summary for final approval by the management board. When writing the executive summary, What is a limitation of or challenges with software-defined networks that must be listed?
Company XYZ has 30 sites using MPLS L3 VPN and the company is now concerned about data integrity. The company wants to redesign the security aspect of their network based on these requirements:
Securely transfer the corporate data over the private WAN
Use a centralized configuration model.
Minimize overhead on the tunneled traffic.
Which technology can be used in the new design to meet the company’s requirements?
A product manufacturing organization is integrating cloud services into their IT solution The IT team is working on the preparation phase of the implementation approach, which includes the Define Strategy step This step defines the scope of IT. the application, and the service. What is one topic that should be considered in the Define Strategy step?
In large-scale networks controllers needs to be able to process millions of flows per second without compromising the quality of the service What are two actions that must be implemented to address scaling limitations when deploying the network*? (Choose two.)
Enterprise XYZ wants to implement fast convergence on their network and optimize timers for OSPF However they also want to prevent excess flooding of ISAs if there is a constantly flapping link on the network Which timers can help prevent excess flooding of LSAs for OSPF?
A small organization of 20 employees is looking to deliver a network design service for modernizing customer networks to support advanced solutions.
Project scope and weekly progress should be visualized by the management.
Always consider feedback and make changes accordingly during the project.
Should consider flexibility to change scope at the point of time.
Which project methodology meets the requirements and have the least impact on the outcome?
Agile and Waterfall are two popular methods for organizing projects What describes any Agile network design development process?
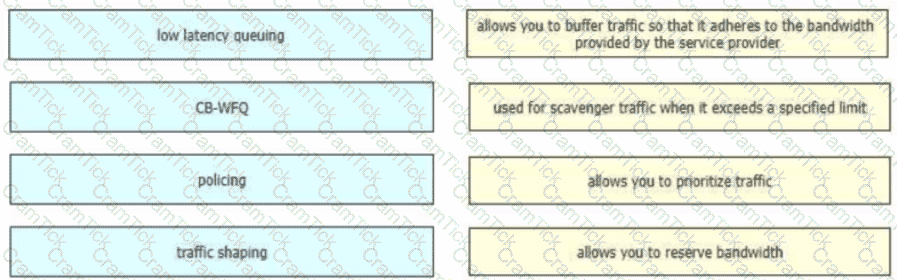
Drag and drop the QoS technologies from the left onto the correct capabilities on the right
Which technique facilitates analytics and knowledge discovery in big data systems to recognize hidden and complex patterns?
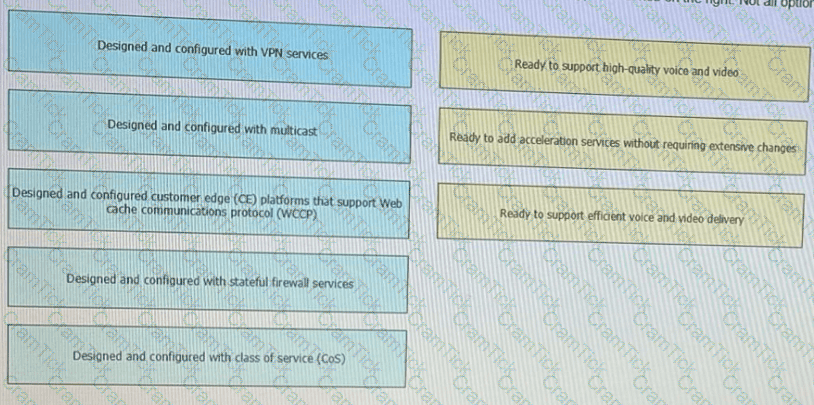
Flexibility, scalability, resiliency, and security are all chrematistics of a services-ready network An architecture featuring a modular design enables technologies and services to be added when the organization is ready to deploy. Drag and drop the design considerations on the left to the to type of service on the right Not all options are used
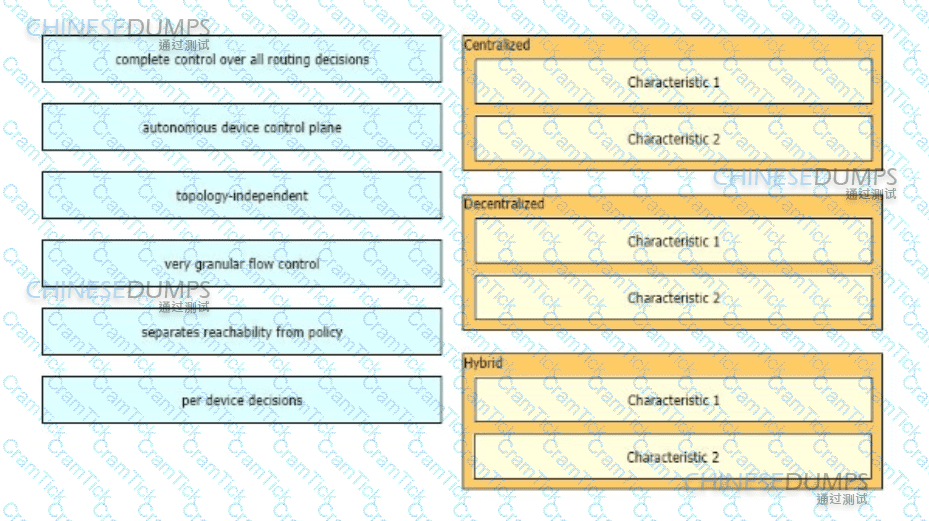
As part of a design solution a consultant needs to describe the trade-offs between different SDN models Drag the characteristics on the left to the correct controller-based network designs on the right in no particular order.
In a distributed cloud-native environment, calls to services and cloud resources can fail caused by unanticipated events that will require longer periods of time to resolve. These faults can range in severity from a partial loss of connectivity to the complete failure of a service. In these situations, it ' s pointless for an application to continually retry an operation that is unlikely to succeed. Which pattern can prevent an application from repeatedly trying to execute an operation that ' s likely to fail?
PaaS provides a cloud-based platform for developing, running, managing applications. Users access the PaaS through a GUI, where development or DevOps teams can collaborate on all their work across the entire application lifecycle including coding, integration, testing, delivery, deployment, and feedback. Which benefit does an organization get by using PaaS?
Which redundancy element plays a crucial role in ensuring business continuity even in challenging situations?
In a controller-based network architecture, between which of the two elements the southbound interface does the communication happen with a goal to program the data plane forwarding tables? (Choose two.)
Company XYZ Is running a redundant private WAN network using OSPF as the underlay protocol The current design accommodates for redundancy In the network, but it Is taking over 30 seconds for the network to reconverge upon failure Which technique can be Implemented In the design to detect such a failure in a subsecond?
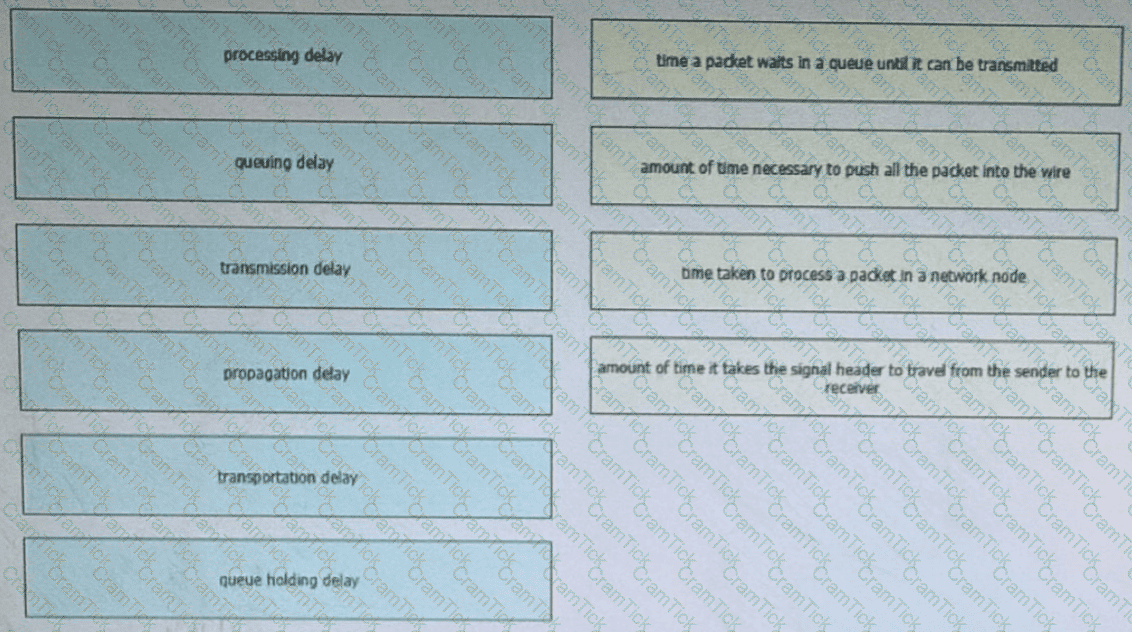
Flow is a set of IP packets passing an observation point in the network during a certain time interval. A flow could consist of ail packets in a specific transport connection or a media stream. Packet flow temporal efficiency can be affected by one-way delay Drag and drop the delay types from the left onto the corresponding definitions on the right Not all are used
Which component of the SDN architecture automatically ensures that application traffic is routed according to policies established by network administrators?
An enterprise SDWAN customer based in the US has several branches in Europe Currently branches use the HQ in the US to access both internal and external services over an MPLS arcuit The design team has been tasked to suggest a solution allowing branches to access their cloud-based office productivity tools and services directly Since all their applications and services are hosted in the cloud, the design team has also been asked to come up with a solution, so branches can connect to the cloud directly from the branch as well Which two cost-effective and optimized solutions can be suggested? (Choose two)
cloud onRamp (SaaS)
The API of an SDN controller named CTL-A uses the HTTP POST method and the same URL for all resources The JSON body of each message is used to get information for specific resources and operations The API of a SDN controller named CTL-B uses HTTP CRUD methods and a uniform interface with different URLs for each resource Which API type is used by each SDN controller?
The first step to building en A! strategy is understanding how it helps achieve business goals and objectives Al-first scorecard is an assessment of your organization ' s readiness to adopt and integrate AI technologies to gauge your capabilities and align stakeholders. Which scorecard is useful to understand whether the organization ' s digital infrastructure is strong enough to ensure seamless, standardized data flow between systems with optimal performance?
Which regulatory compliance element ensures adherence to regulations and improves speed to market, which gives businesses a competitive advantage?
which two actions must be taken when assessing an existing wireless network implementation for its readliness to support voice traffic? (choose two)


