Will this command ensure that overlay traffic between service tasks is encrypted?
Solution: docker network create -d overlay -o encrypted=true
Does this command create a swarm service that only listens on port 53 using the UDP protocol?
Solution. ‘docker service create -name dns-cache -p 53:53 -udp dns-cache’
Two development teams in your organization use Kubernetes and want to deploy their applications while ensuring that Kubernetes-specific resources, such as secrets, are grouped together for each application.
Is this a way to accomplish this?
Solution: Create one namespace for each application and add all the resources to it.
Is this a way to configure the Docker engine to use a registry without a trusted TLS certificate?
Solution. Set and export the IGNORE_TLS environment variable on the command line.
Does this command create a swarm service that only listens on port 53 using the UDP protocol?
Solution. ‘docker service create -name dns-cache -p 53:53 -constraint networking.protocol.udp=true dns-cache"
Is this statement correct?
Solution: A Dockerfile provides instructions for building a Docker image
Will a DTR security scan detect this?
Solution.image configuration poor practices, such as exposed ports or inclusion of compilers in production images
Does this command create a swarm service that only listens on port 53 using the UDP protocol?
Solution: ‘docker service create -name dns-cache -p 53:53 -service udp dns-cache'
A persistentVolumeClaim (PVC) is created with the specification storageClass: "", and size requirements that cannot be satisfied by any existing persistentVolume.
Is this an action Kubernetes takes in this situation?
Solution: The PVC remains unbound until a persistentVolume that matches all requirements of the PVC becomes available.
Will this configuration achieve fault tolerance for managers in a swarm?
Solution: at least seven nodes in total
Will this command ensure that overlay traffic between service tasks is encrypted?
Solution:docker service create --network --encrypted
You are troubleshooting a Kubernetes deployment called api, and want to see the events table for this object. Does this command display it?
Solution: kubectl events deployment api
Does this command display all the pods in the cluster that are labeled as 'env: development'?
Solution: 'kubectl get pods --all-namespaces -label env=development'
Does this command display all the pods in the cluster that are labeled as 'env: development'?
Solution: 'kubectl get pods -I env=development'
The Kubernetes yaml shown below describes a clusterIP service.
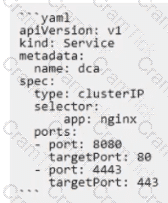
Is this a correct statement about how this service routes requests?
Solution: Traffic sent to the IP of this service on port 8080 will be routed to port 80 in a random pod with the label aPP: nginx.
You configure a local Docker engine to enforce content trust by setting the environment variable
DOCKER_CONTENT_TRUST=1.
If myorg/myimage: 1.0 is unsigned, does Docker block this command?
Solution: docker container run myorg/myimage:1.0
In Docker Trusted Registry, is this how a user can prevent an image, such as 'nginx:latest’, from being overwritten by another user with push access to the repository?
Solution: Tag the image with 'nginx:immutable'.
In Docker Trusted Registry, is this how a user can prevent an image, such as 'nginx:latest’, from being overwritten by another user with push access to the repository?
Solution: Use the DTR web Ul to make all tags in the repository immutable.
Two development teams in your organization use Kubernetes and want to deploy their applications while ensuring that Kubernetes-specific resources, such as secrets, are grouped together for each application.
Is this a way to accomplish this?
Solution: Add all the resources to the default namespace.
Is this an advantage of multi-stage builds?
Solution: faster image builds by allowing parallel execution of Docker builds
You created a new service named 'http' and discover it is not registering as healthy. Will this command enable you to view the list of historical tasks for this service?
Solution: 'docker ps http'
A user's attempts to set the system time from inside a Docker container are unsuccessful.
Could this be blocking this operation?
Solution.SELinux
Will this Linux kernel facility limit a Docker container's access to host resources, such as CPU or memory?
Solution: cgroups
Is this a supported user authentication method for Universal Control Plane?
Solution: PAM
Your organization has a centralized logging solution, such as Splunk.
Will this configure a Docker container to export container logs to the logging solution?
Solution.docker run -- log driver=splunk for every container at run time
You want to create a container that is reachable from its host's network.
Does this action accomplish this?
Solution.Use either EXPOSE or -publish to access the container on the bridge network.
Is this the purpose of Docker Content Trust?
Solution: Enable mutual TLS between the Docker client and server.
In Kubernetes, to mount external storage to a filesystem path in a container within a pod, you would use a volume in the pod specification. This volume is populated with a persistentVolumeClaim that is bound to an existing persistentVolume. The persistentVolume is defined and managed by the storageClass which provides dynamic or static provisioning of the volume and determines what type of storage will be provided1. References:
•Dynamic Volume Provisioning | Kubernetes
Is this a supported user authentication method for Universal Control Plane?
Solution: Docker ID
Some Docker images take time to build through a Continuous Integration environment. You want to speed up builds and take advantage of build caching.
Where should the most frequently changed part of a Docker image be placed in a Dockerfile?
You add a new user to the engineering organization in DTR.
Will this action grant them read/write access to the engineering/api repository?
Solution: Add them to a team in the engineering organization that has read/write access to the engineering/api repository.
Is this a supported user authentication method for Universal Control Plane?
Solution.LDAP
Will this command display a list of volumes for a specific container?
Solution. ‘docker container inspect nginx’
Will this command ensure that overlay traffic between service tasks is encrypted?
Solution:docker service create --network --secure
A company's security policy specifies that development and production containers must run on separate nodes in a given Swarm cluster.
Can this be used to schedule containers to meet the security policy requirements?
Solution: node affinities
What is the difference between the ADD and COPY Dockerfile instructions? (Select two.)
Are these conditions sufficient for Kubernetes to dynamically provision a persistentVolume, assuming there are no limitations on the amount and type of available external storage?
Solution: A persistentVolumeClaim is created that specifies a pre-defined storageClass.
You want to provide a configuration file to a container at runtime. Does this set of Kubernetes tools and steps accomplish this?
Solution: Mount the configuration file directly into the appropriate pod and container using the .spec.containers.configMounts key.
The following Docker Compose file is deployed as a stack:
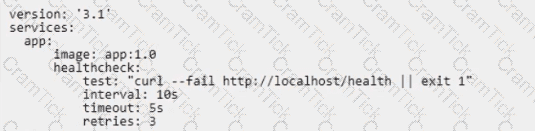
Is this statement correct about this health check definition?
Solution: Health checks test for app health ten seconds apart. If the test fails, the container will be restarted three times before it gets rescheduled.
You created a new service named 'http' and discover it is not registering as healthy. Will this command enable you to view the list of historical tasks for this service?
Solution:'docker service ps http'
Will a DTR security scan detect this?
Solution: known vulnerabilities or exposures in binaries
You are running only Kubernetes workloads on a worker node that requires
maintenance, such as installing patches or an OS upgrade.
Which command must be run on the node to gracefully terminate all pods on
the node, while marking the node as unschedulable?
During development of an application meant to be orchestrated by Kubernetes, you want to mount the /data directory on your laptop into a container.
Will this strategy successfully accomplish this?
Solution. Set containers. Mounts. hostBinding: /data in the container's specification.
Are these conditions sufficient for Kubernetes to dynamically provision a persistentVolume, assuming there are no limitations on the amount and type of available external storage?
Solution: A default storageClass is specified, and subsequently a persistentVolumeClaim is created.
In Docker Trusted Registry, is this how a user can prevent an image, such as 'nginx:latest’, from being overwritten by another user with push access to the repository?
Solution: Remove push access from all other users.
An application image runs in multiple environments, with each environment using different certificates and ports.
Is this a way to provision configuration to containers at runtime?
Solution: Create a Dockerfile for each environment, specifying ports and ENV variables for certificates.
In Docker Trusted Registry, is this how a user can prevent an image, such as 'nginx:latest’, from being overwritten by another user with push access to the repository?
Solution: Keep a backup copy of the image on another repository.
Your organization has a centralized logging solution, such as Splunk.
Will this configure a Docker container to export container logs to the logging solution?
Solution: Set the log-driver and log-oPt keys to values for the logging solution (Splunk) In the daemon.json file.
Is this statement correct?
Solution.A Dockerfile stores persistent data between deployments of a container
Will this configuration achieve fault tolerance for managers in a swarm?
Solution: an odd number of manager nodes, totaling more than two
Will this command display a list of volumes for a specific container?
Solution: 'docker container inspect nginx'
You want to create a container that is reachable from its host's network. Does this action accomplish this?
Solution:Use either EXPOSE or --publish to access the containers on the bridge network
Is this a way to configure the Docker engine to use a registry without a trusted TLS certificate?
Solution: Set IGNORE_TLS in the 'daemon.json' configuration file.
The Kubernetes yaml shown below describes a networkPolicy.
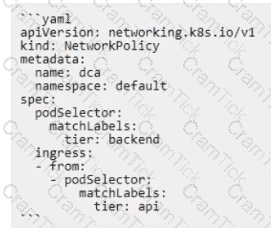
Will the networkPolicy BLOCK this traffic?
Solution: a request issued from a pod lacking the tier: api label, to a pod bearing the tier: backend label
Seven managers are in a swarm cluster.
Is this how should they be distributed across three datacenters or availability zones?
Solution: 5-1-1
Docker Certified Associate | DCA Questions Answers | DCA Test Prep | Docker Certified Associate (DCA) Exam Questions PDF | DCA Online Exam | DCA Practice Test | DCA PDF | DCA Test Questions | DCA Study Material | DCA Exam Preparation | DCA Valid Dumps | DCA Real Questions | Docker Certified Associate DCA Exam Questions


