The following description of the construction of a digital certificate, which item is wrong
The following description of IDS, which items are correct
The IDS cannot be linked to the firewall.
A three-way handshake is required to establish a TCP connection, and a four-way handshake is required to end a TCP connection.
When IPSec VPN uses tunnel mode to encapsulate packets, which of the following is not within the encryption scope of the ESP security protocol?
Which of the following statements is correct about characteristics of a firewall?
The RADIUS protocol specifies how to pass user information, billing information, authentication and billing results between the NAS and the RADIUS server, and the RADIUS server is responsible for receiving the user's connection request, completing the authentication, and returning the result to the NAS.
Which of the following packets is controlled by a firewall's security policy by default?
Which of the following characteristics does a denial-of-service attack include?
Database operation records can be used as ___ evidence to backtrack security events.[fill in the blank]*
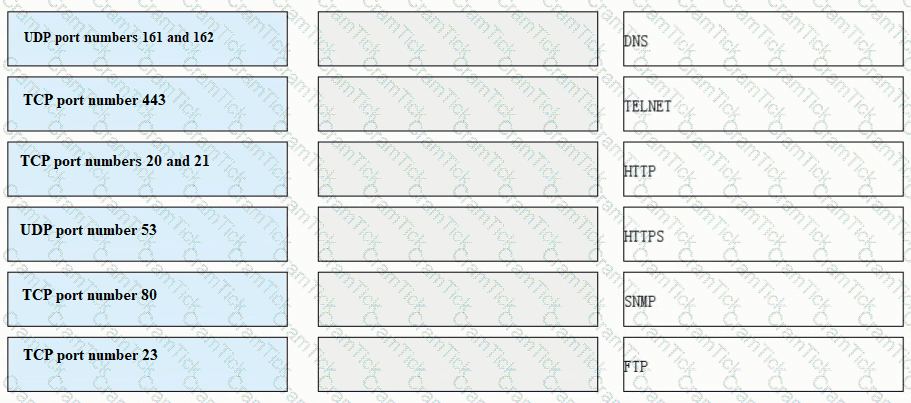
Match each of the following application layer service protocols with the correct transport layer protocols and port numbers.
A Web server is deployed in an enterprise intranet to provide Web access services to Internet users, and in order to protect the access security of the server, it should be divided into the _____ area of the firewall.
How frequently should antivirus signature databases be updated to ensure the effectiveness of an antivirus program or software?
Which of the following functions help implement IPsec secure transmission of user service data on the Internet by means of encryption and authentication?
Which of the following descriptions about the main implementation of single sign-on is wrong?
Which of the following NAT technologies can implement a public network address to provide source address translation for multiple private network addresses ( )*
HTTPS introduces the TLS layer based on HTTP to provide identity authentication, encryption, and integrity check for data transmission.
We should choose the encryption algorithm according to our own use characteristics. When we need to encrypt a large amount of data, it is recommended to use the ____ encryption algorithm to improve the encryption and decryption speed.[fill in the blank]*
Which of the following attack methods is to construct special SQL statements and submit sensitive information to exploit program vulnerabilities
As shown in the figure, the administrator needs to test the network quality of the 20.0.0/24 CIDR block to the 40.0.0/24 CIDR block on Device B, and the device needs to send large packets for a long time to test the network connectivity and stability.

In asymmetric encryption algorithms, only public keys can be used to encrypt data, and private keys are used to decrypt data. This process is irreversible.
DES is a stream encryption algorithm, because the cipher capacity is only 56 bits, so it is not enough to deal with the weakness of insufficient security, and later 3DES was proposed.
Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution. 1. Inhibition stage, 2. recovery phase, 3. Detection stage, 4. eradication phase[fill in the blank]*
What are the correct entries in the following description of firewall security zones?
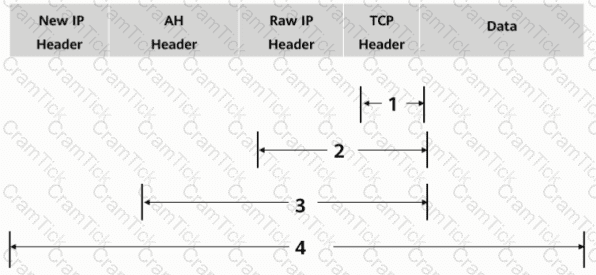
As shown in the figure, what is the authentication range of the AH protocol in tunnel mode?
An engineer needs to back up the firewall configuration. Now he wants to use a command to view all the current configurations of the firewall. May I ask the command he uses is ____[fill in the blank]*
While working for a company, Tom receives an email with an attachment. Which of the following operations is correct?
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
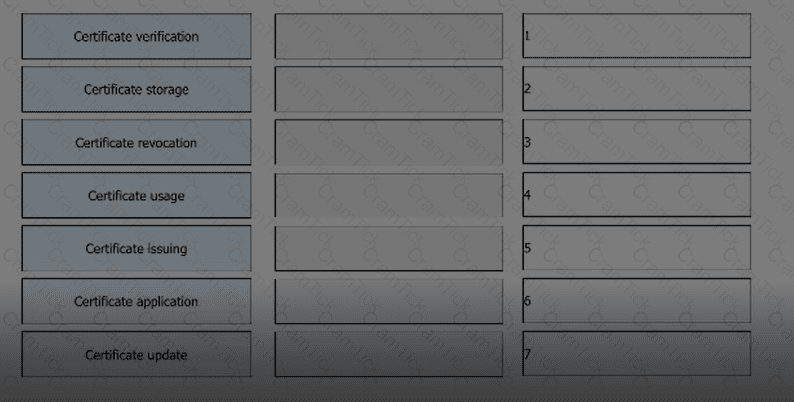
Arrange the following processes in the correct order based on the PKI lifecycle.