You are creating a custom trainable classifier to Identify organizational product codes referenced in Microsoft 36S content. You identify 300 files to use as seed content When? should you store the seed content?
You have a Microsoft 365 E5 subscription.
You create a data loss prevention (DLP) policy and select.
Use Notifications to inform your users and help educate them on the proper use of sensitive info.
Which apps will show the policy tip?
You have a Microsoft 365 E5 subscription.
You need to enable support for sensitivity labels in Microsoft SharePoint Online.
What should you use?
You have a Microsoft 365 E5 subscription.
You plan to implement insider risk management for users that manage sensitive data associated with a project.
You need to create a protection policy for the users. The solution must meet the following requirements:
● Minimize the impact on users who are NOT part of the project.
● Minimize administrative effort.
What should you do first?
You have a Microsoft 365 E5 subscription.
You need to review a Microsoft 365 Copilot usage report.
From where should you review the report?
You have a data loss prevention (DIP) policy that applies to the Devices location. The policy protects documents that contain United States passport numbers
Users report that they cannot upload documents to a travel management website because of the pokey.
You need to ensure that the users can upload the documents to the travel management website. The solution must prevent the protected content from being uploaded to other locations.
Which Microsoft 365 Endpoint data loss prevention (Endpoint DIP) setting should you configure?
You have a Microsoft 365 E5 subscription.
You plan to use insider risk management to collect and investigate forensic evidence.
You need to enable forensic evidence capturing.
What should you do first?
You have a Microsoft 365 tenant.
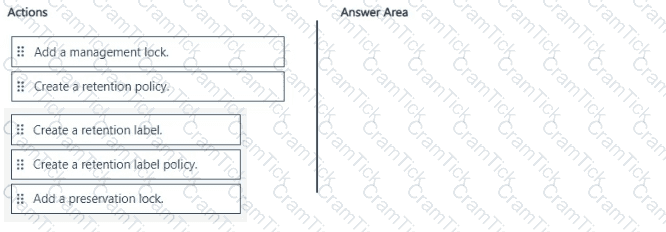
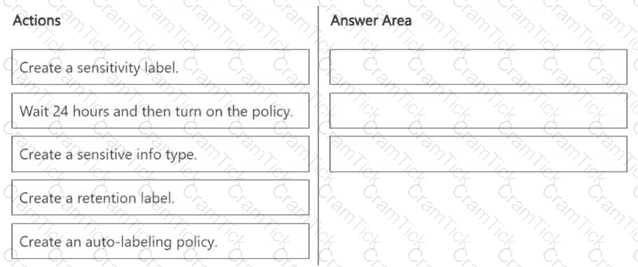
A new regulatory requirement states that all documents containing a patent ID be labeled, retained for 10 years, and then deleted. The policy used to apply the retention settings must never be disabled or deleted by anyone.
You need to implement the regulatory requirement.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
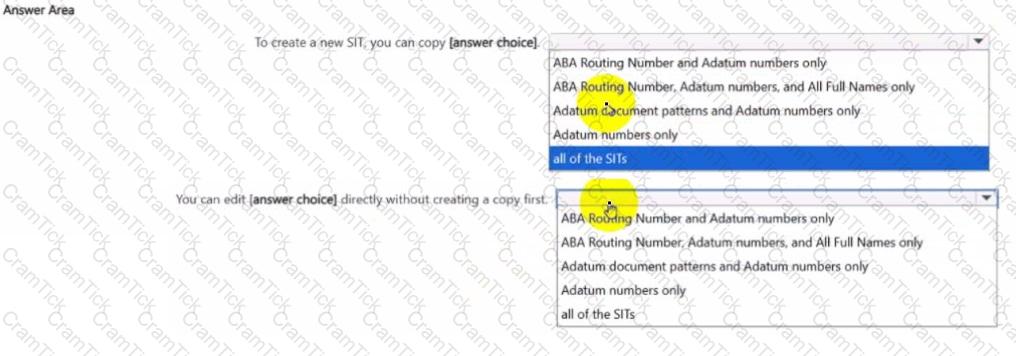
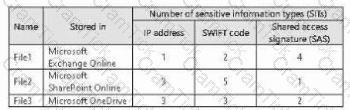
You have a Microsoft 36S subscription that contains the sensitive information types (SITs) shown in the following exhibit.
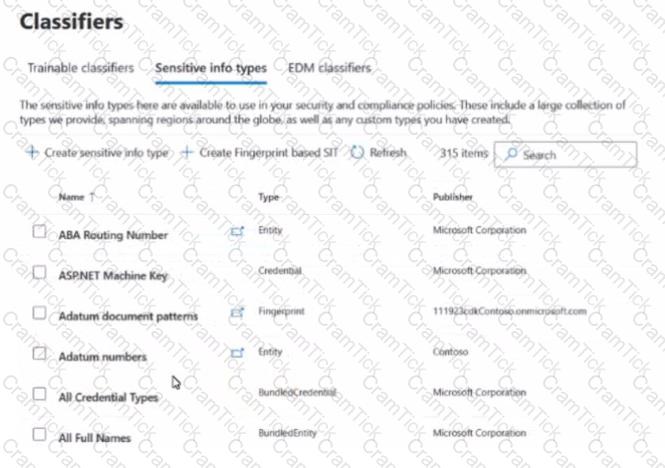
Use the drop-down menus To select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct flection is worth one point.
You have a data loss prevention (DIP) policy that has the advanced DIP rules shown in the following table.
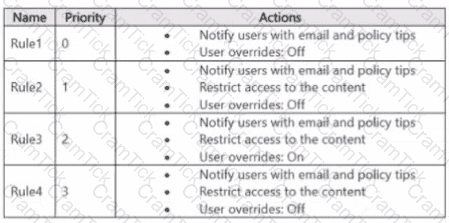
You need to identity which rules will apply when content matches multiple advanced DIP rules.
Which rules should you identify? To answer, select the appropriate options in the answer area.
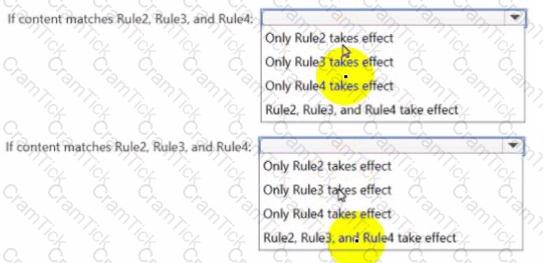
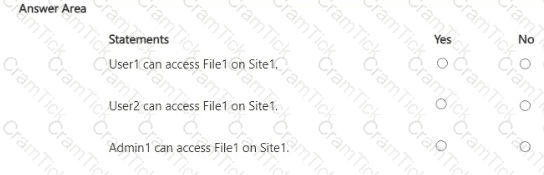
You have a Microsoft 365 E5 subscription that contains a Microsoft SharePoint Online site named Site1 and the users shown in the following table.
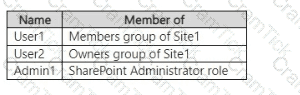
You have a data loss prevention (DLP) policy named DLP1 as shown in the following exhibit.
You apply DLP1 to Site1.
User1 uploads a file named File1 to Site1. File1 does NOT match any of the DLP1 rules. User2 updates File1 to contain data that matches the DLP1 rules.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
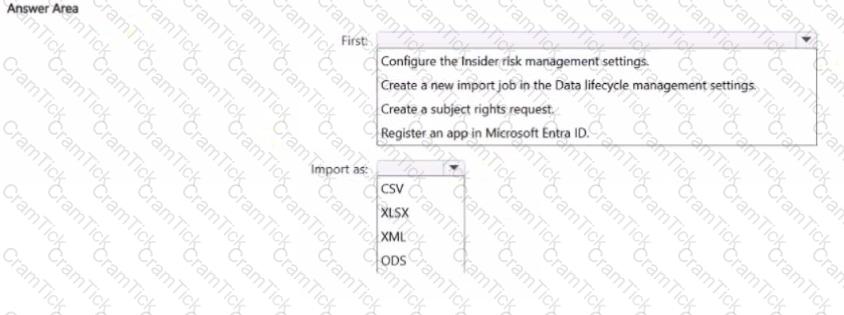
You have a Microsoft 36S ES subscription.
You plan to use the Microsoft Purview portal to map human resources (HR) data for use with insider risk management policies.
You need to add a data connector to import the HR data.
What should you do first and in which format should you import the data? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
HOTSPOT
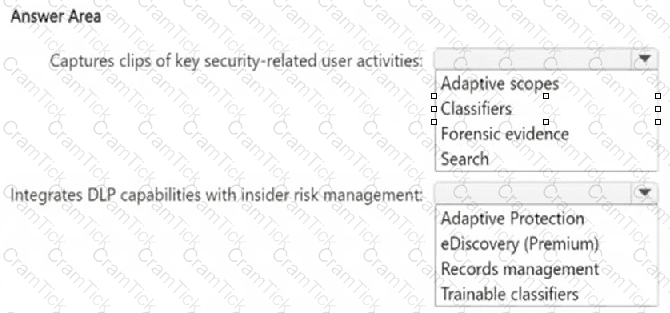
You have a Microsoft 365 E5 subscription.
You need to implement a compliance solution that meets the following requirements:
● Captures clips of key security-related user activities, such as the exfiltration of sensitive company data.
● Integrates data loss prevention (DLP) capabilities with insider risk management.
What should you use for each requirement? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription.
You configure a Microsoft Purview insider risk management policy named Policy1.
You need to ensure that you will receive real-time recommendations on how to configure the indicator thresholds for Policy1. The solution must ensure that the recommendations are based on a user ' s activity from the past 10 days.
What should you do first?
You have a Microsoft 365 E5 tenant that contains a user named User1. User1 is assigned the Compliance Administrator role. User1 cannot view the regular expression in the IP Address sensitive info type. You need to ensure that User! can view the regular expression. What should you do?
You have a Microsoft 365 E5 subscription. The subscription contains 500 devices that are onboarded to Microsoft Purview.
You select Activate Microsoft Purview Audit.
You need to ensure that you can track interactions between users and generative AI websites.
What should you deploy to the devices?
You have a Microsoft 365 subscription. You create a retention policy and apply the policy to Exchange Online mailboxes.
You need to ensure that the retention policy tags can be assigned to mailbox items as soon as possible.
What should you do?
You have 4 Microsoft 565 E5 subscription that contains two Microsoft SharePoint Online sites named Site1 and Site2. You plan to configure a retention label named Labe1 and apply label1 to all the files in Site1 You need to ensure that two years after a file is created in Site1. the file moves automatically to Site2. How should you configure the Choose what happens after the retention period setting for Label1?
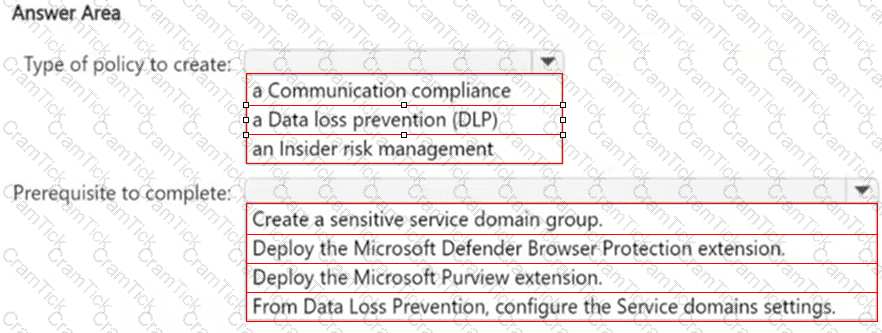
You have a Microsoft 36S ES subscription.
From the Microsoft Purview Data Security Posture Management for Al portal, you review the recommendations for Al data security
You plan to create a one-click policy to block elevated risk users from pasting or uploading sensitive data to Al websites
How will the policy be configured? To answer, select the appropriate options in the answer area
NOTE: Each correct selection is worth one point.
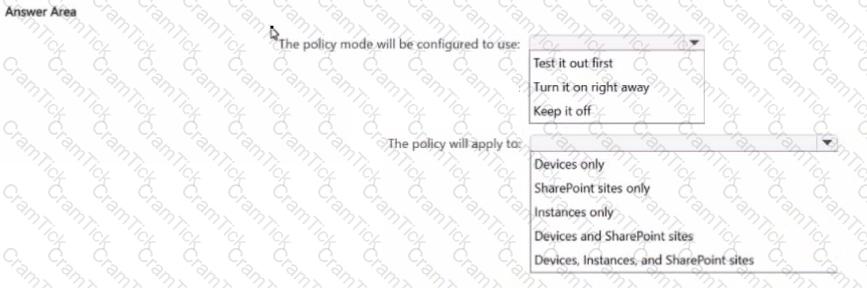
HOTSPOT
You are reviewing policies for the SharePoint Online environment.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
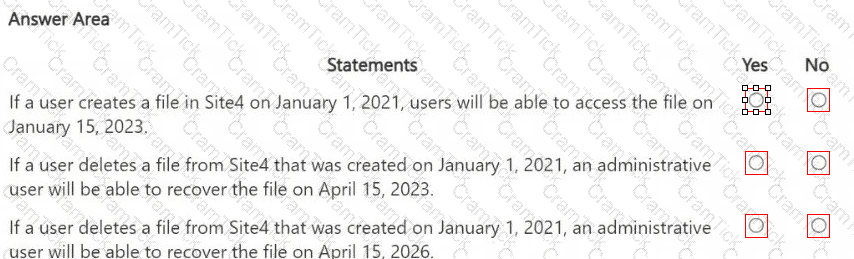
HOTSPOT
You have a Microsoft 365 E5 subscription that uses Microsoft Purview.
You need ensure that an incident will be generated when a user visits a phishing website.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
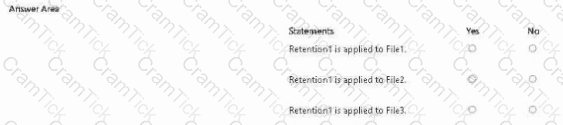
You have a Microsoft 365 subscription that has a retention label named Retention1. The subscription contains the files shown in the following table.
You create an auto-labeling policy named Policy1 that will automatically apply Retention1 as shown in the Auto-labeling policy
Exhibit. (Click the Auto-labeling policy tab.)
You configure Policy1 to apply Retention1 as shown in the Locations exhibit. (Click the Locations tab.)
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You need to meet the retention requirement for the users ' Microsoft 365 data.
What is the minimum number of retention policies required to achieve the goal?
You need to meet the technical requirements for the Site1 documents.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You need to meet the technical requirements for the creation of the sensitivity labels.
To which user or users must you assign the Sensitivity Label Administrator role?
HOTSPOT
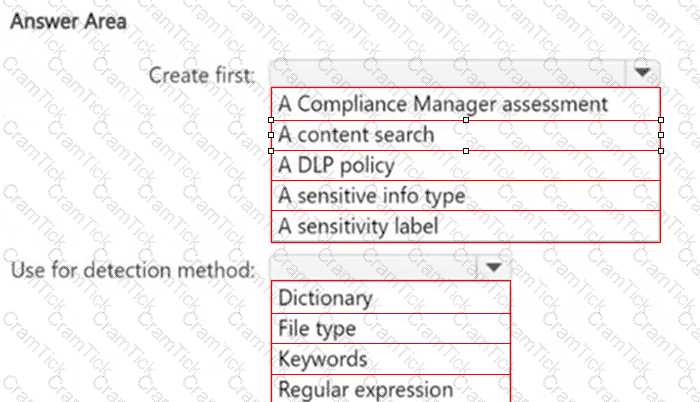
You need to meet the technical requirements for the confidential documents.
What should you create first, and what should you use for the detection method? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
HOTSPOT
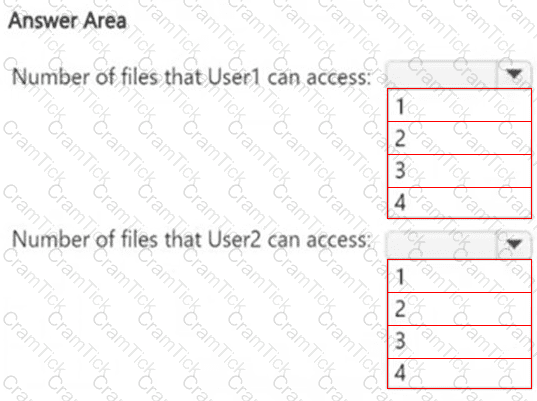
How many files in Site2 can User1 and User2 access after you turn on DLPpolicy1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.