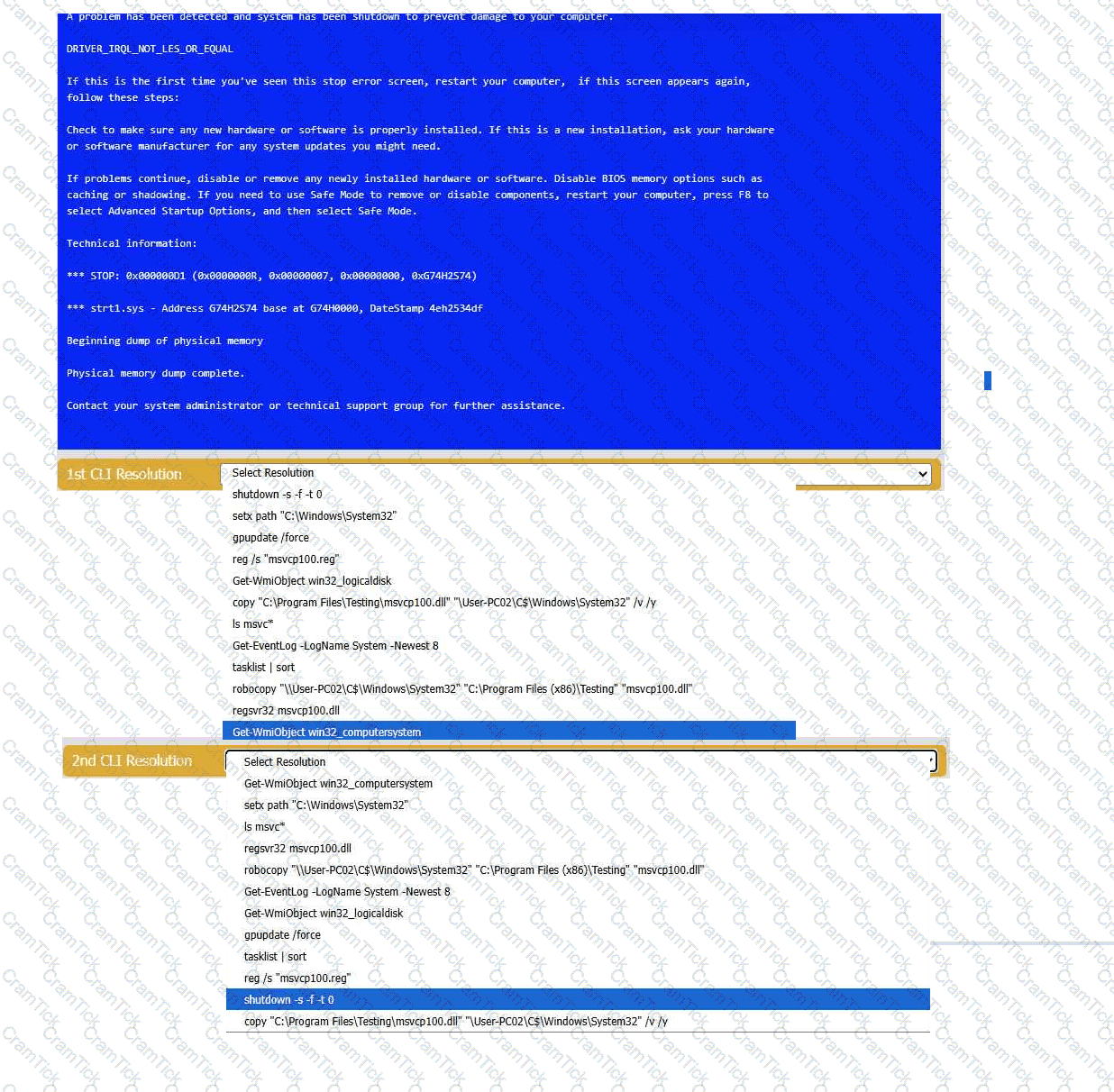
After installing new webcam software, a PC experiences BSOD during videoconference calls. What should the technician do next?
While working from home, the Chief Financial Officer (CFO) needs to open reports from accounting software. When the application opens, the CFO sees the error “unable to connect to database.” Which of the following should the CFO do first?
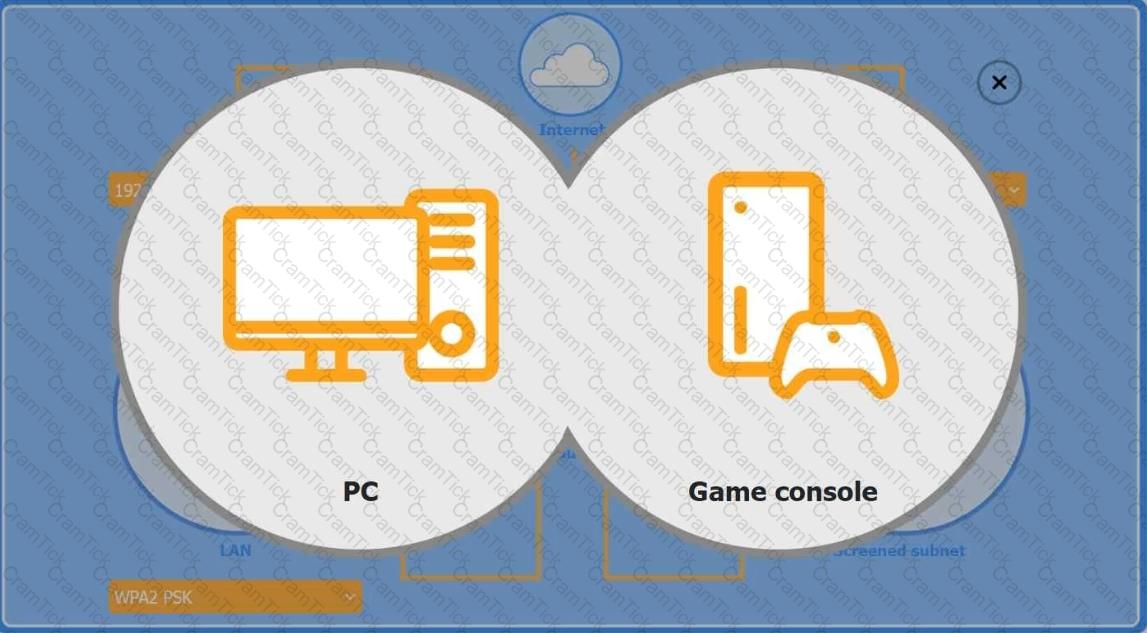
You are configuring a home network for a customer. The customer has requested the ability to access a Windows PC remotely, and needs all chat and optional functions to work in their game console.
INSTRUCTIONS
Use the drop-down menus to complete the network configuration for the customer. Each option may only be used once, and not all options will be used.
Then, click the + sign to place each device in its appropriate location.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Wireless AP LAN
Firewall Screened Subnet
An engineer notices that many websites prompt users to input login and payment details. The engineer wants to require the browser to encrypt communications. Which of the following best helps to protect sensitive data?
A smartphone user unsuccessfully attempts to open an email attachment that includes an unexpected overdue invoice. After that attempt, the user notices performance issues while using the mobile browser and other applications. The user restarts the smartphone, but the issue persists. Which of the following actions would most likely resolve the issue?
A help desk technician recently installed an SSH client on a workstation in order to access remote servers. What does this enable?
Which of the following file types is best for performing automated tasks on startup on a Windows computer?
Which of the following is the quickest way to move from Windows 10 to Windows 11 without losing data?
When a corporate laptop is connected to the company network, it can reach external websites. However, it cannot reach any internal websites, displaying the error message “Cannot reach this page.” Which of the following should a technician configure?
A desktop technician is mapping a remote Windows share \\WinNAS\shared as local drive Z:. Which command should the technician run?
A technician is troubleshooting a print spooler that fails to start on a Windows 11 desktop computer. The technician determines the root cause is that required dependencies are failing to run. Which of the following tools is the technician using?
A technician completes the installation of an OS that appears to be successful. However, when the technician removes the USB drive that was used for the installation and restarts the system, the error “No boot device found” appears. Which of the following should the technician do next to resolve the issue?
A technician is attempting to join a workstation to a domain but is receiving an error message stating the domain cannot be found. However, the technician is able to ping the server and access the internet. Given the following information:
IP Address – 192.168.1.210
Subnet Mask – 255.255.255.0
Gateway – 192.168.1.1
DNS1 – 8.8.8.8
DNS2 – 1.1.1.1
Server – 192.168.1.10
Which of the following should the technician do to fix the issue?
Which of the following file types allows macOS users to uninstall software completely by placing the file in the trash?
A technician is working on multiple remote machines using a command line. Which of the following commands should the technician use to verify which SMB shares are currently mapped?
Which of the following file types would a desktop support technician most likely use to automate tasks for a Windows user log-in?
Multiple users clicked a phishing link from a compromised email account. The security team isolates and removes the threat. Then, the management team provides security awareness training to the company. What step is this?
A technician needs to map a shared drive from a command-line interface. Which of the following commands should the technician use?
A technician needs to change hibernation settings on a Windows computer via a batch file. Domain policies are unavailable. Which is the best method?
A Microsoft OS laptop user requests an alternative log-in authentication method because they have forgotten their password multiple times. Which of the following should a technician enable to satisfy this request?
A customer is unable to open some files on their system. Each time the customer attempts to open a file, the customer receives a message that the file is encrypted. Which of the following best describes this issue?
A user ' s application only works with a legacy version of the OS. The OS is reaching its end-of-life date. For security reasons, the company is migrating to the current version of the OS. Which of the following is the most efficient way to complete the migration while maintaining accessibility to the application?
Which of the following must be followed during incident response to ensure the collected evidence is properly handled and accounted for?
A company computer is being repurposed within an organization. The existing configuration has a static IP address, but it is no longer required. Which of the following should a technician do to satisfy the network requirements?
Which of the following is a Linux command that is used for administrative purposes?
A user is attempting to open on a mobile phone a HD video that is hosted on a popular media streaming website. The user is receiving connection timeout errors. The mobile reception icon area is showing two bars next to 3G. Which of the following is the most likely cause of the issue?
A company recently transitioned to a cloud-based productivity suite and wants to secure the environment from external threat actors. Which of the following is the most effective method?
A company wants to prevent unauthorized physical access to its mobile devices. Which of the following should the company do? (Select two).
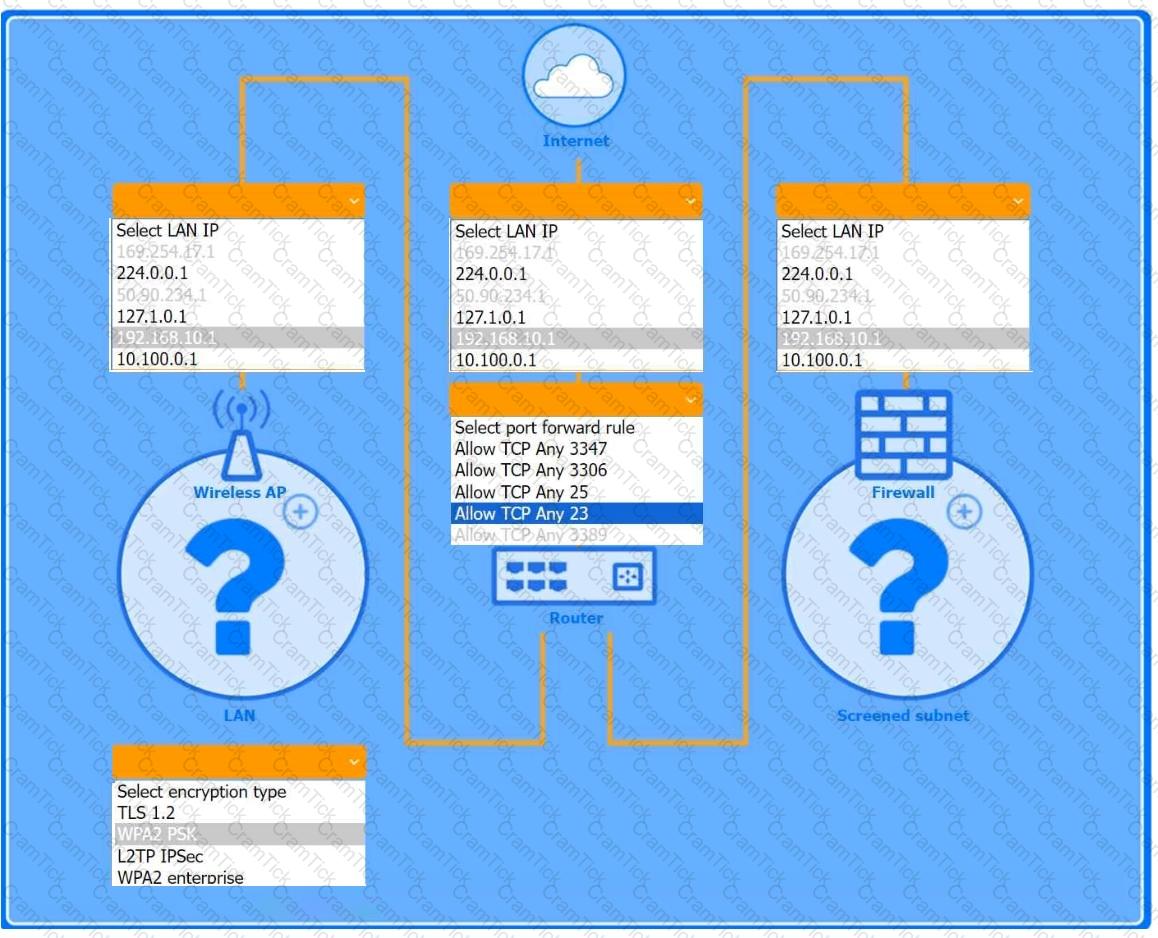
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
Why would a network engineering team provide a help desk technician with IP addresses for a wired network segment?
A technician is installing a cloud-based productivity suite and gets an error saying the installation is unavailable. What should be tried first?
A technician is reviewing an organization ' s current incident management policy. The organization uses a third-party vendor to protect the organization ' s assets with multiple tools. Which of the following service types is the organization using?
A developer is using an AI tool to generate a complex sorting algorithm for a web application. Which of the following is the best choice to legally generate code in their application?
Which of the following concepts should a technician consider when discussing confidential work projects with individuals outside the company?
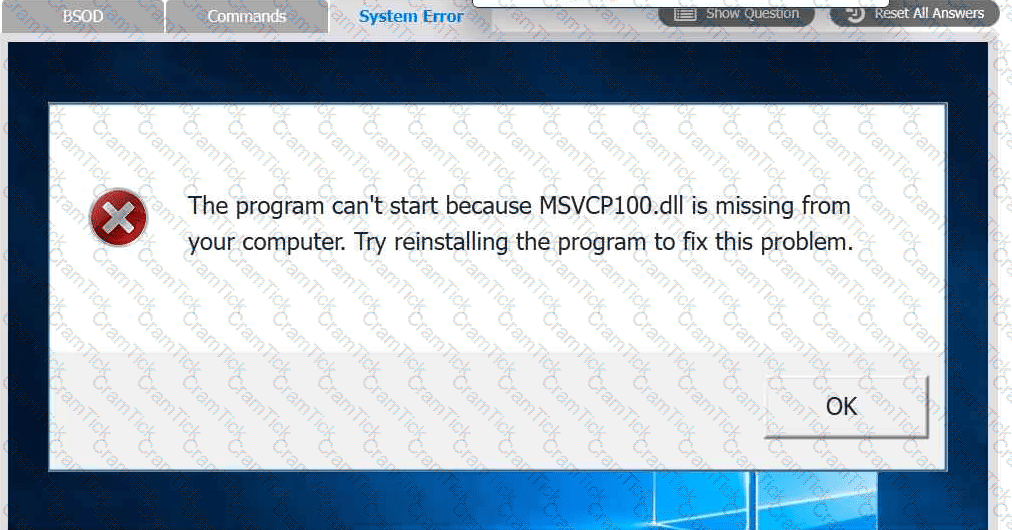
A user reports that after a recent software deployment to upgrade the Testing application, they can no longer use it. However, other employees can successfully
use the Testing program.
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve
any issues discovered by selecting the:
· First command to resolve the issue
· Second command to resolve the issue
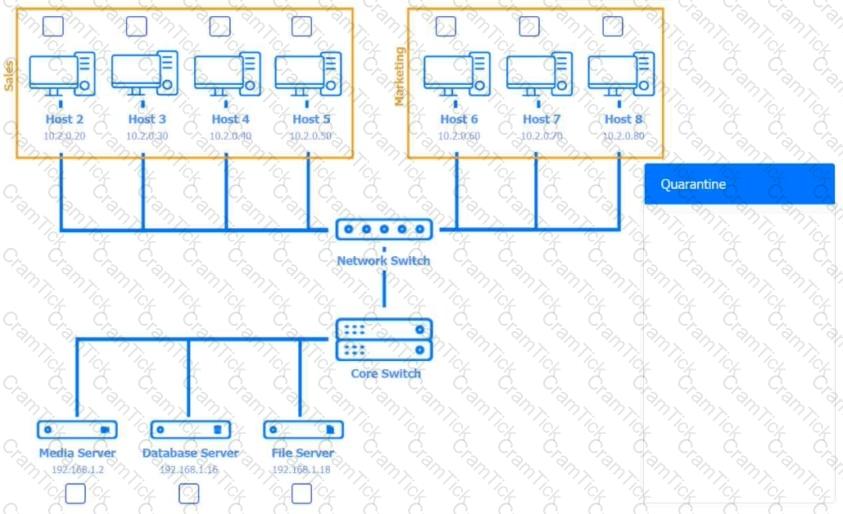
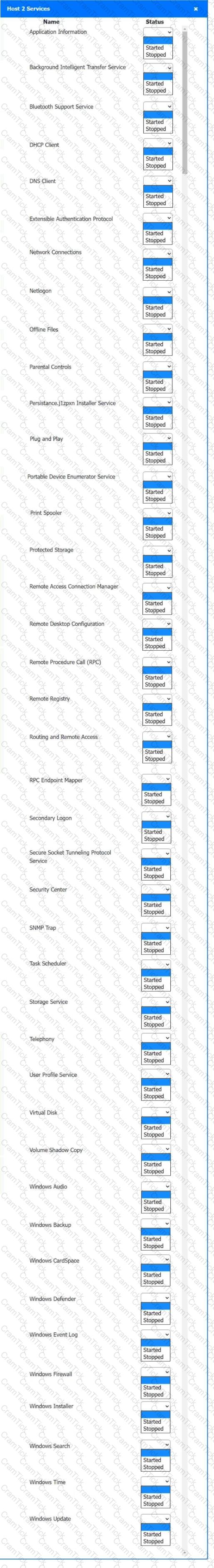
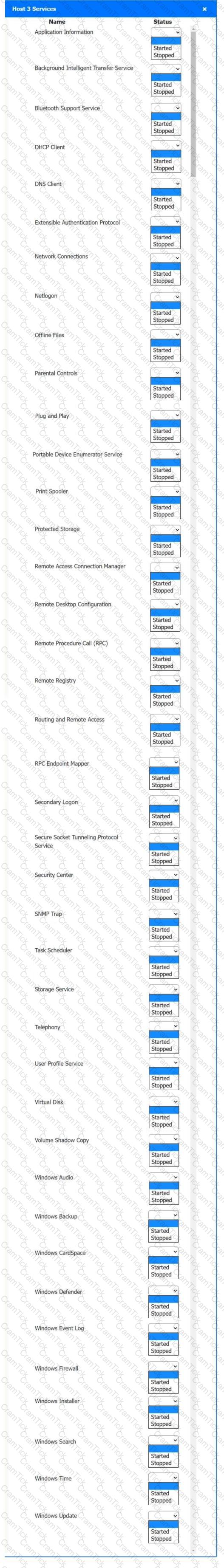
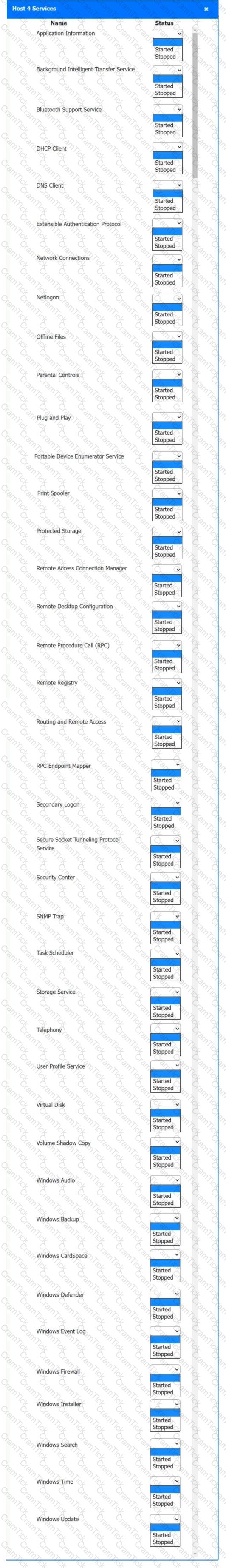
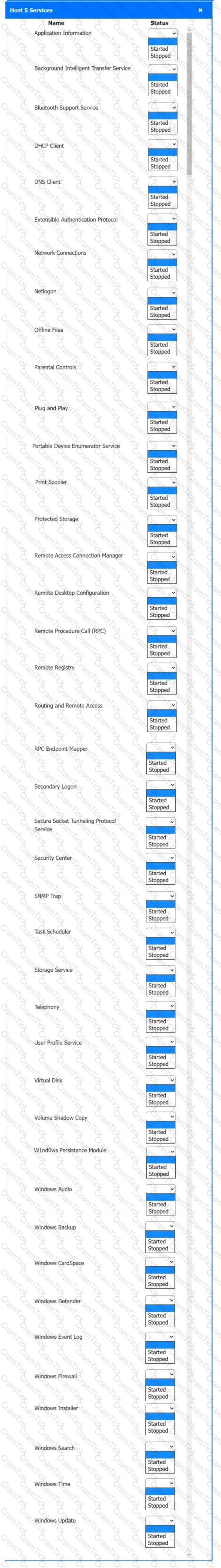
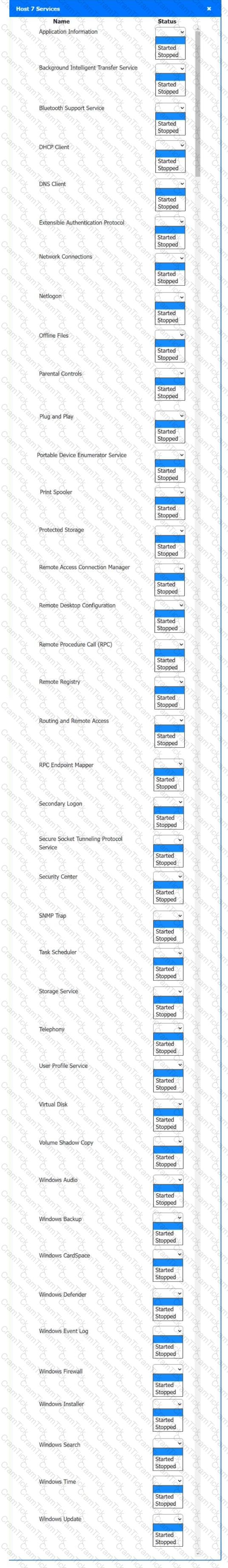
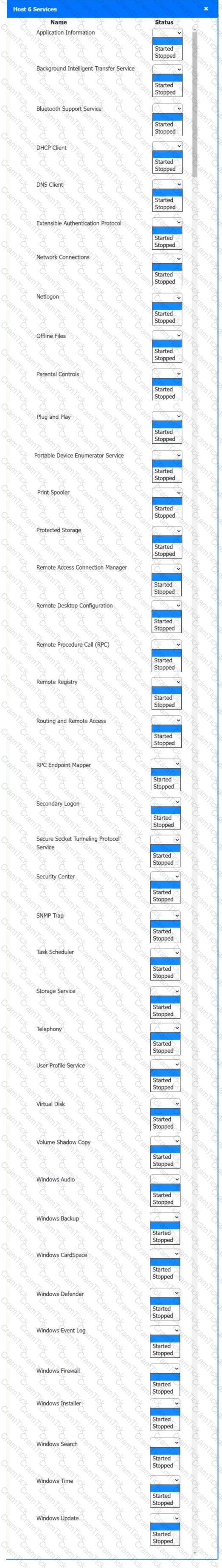
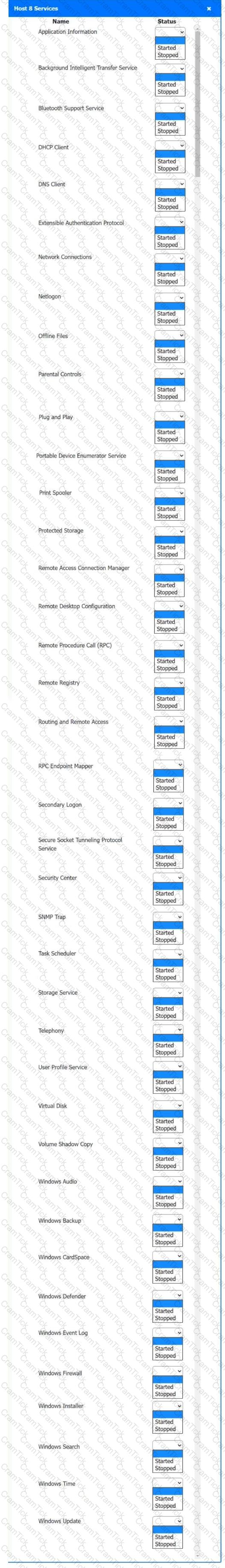
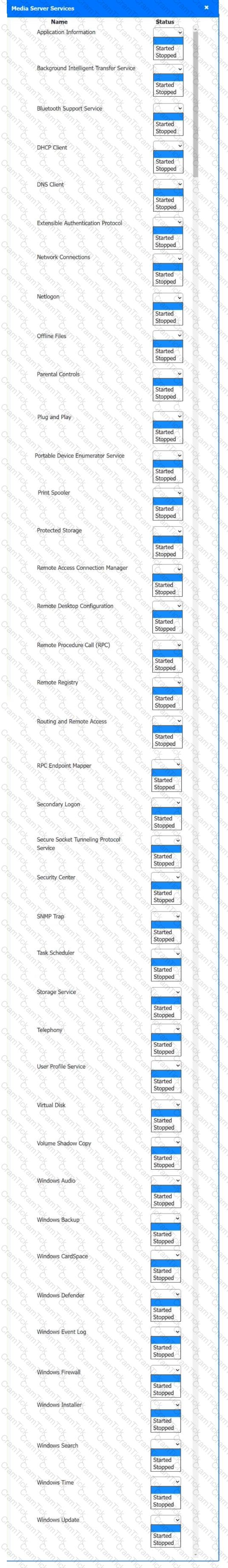
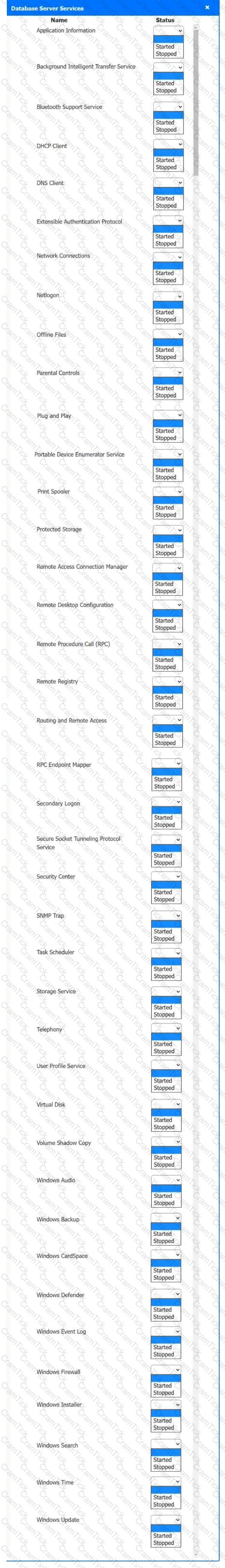
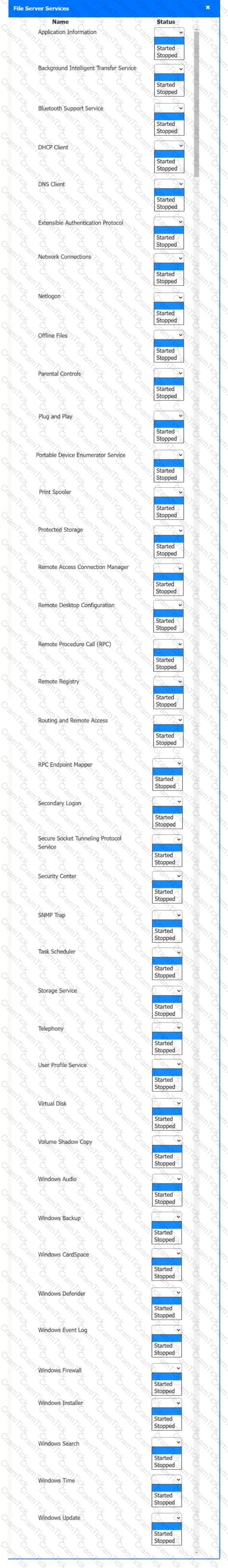
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
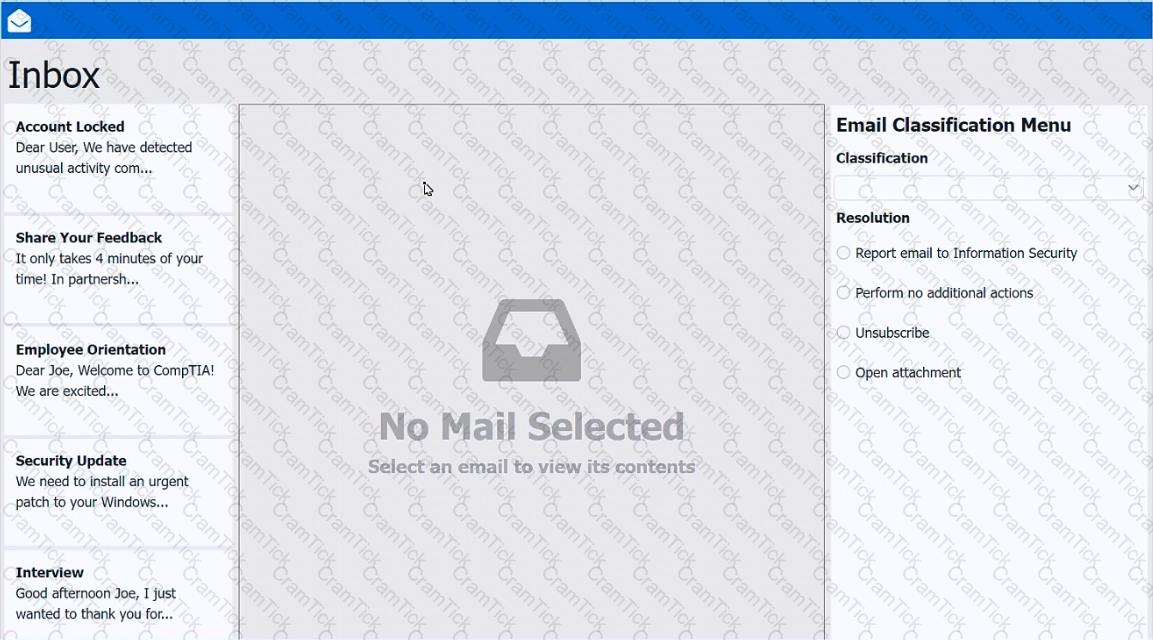
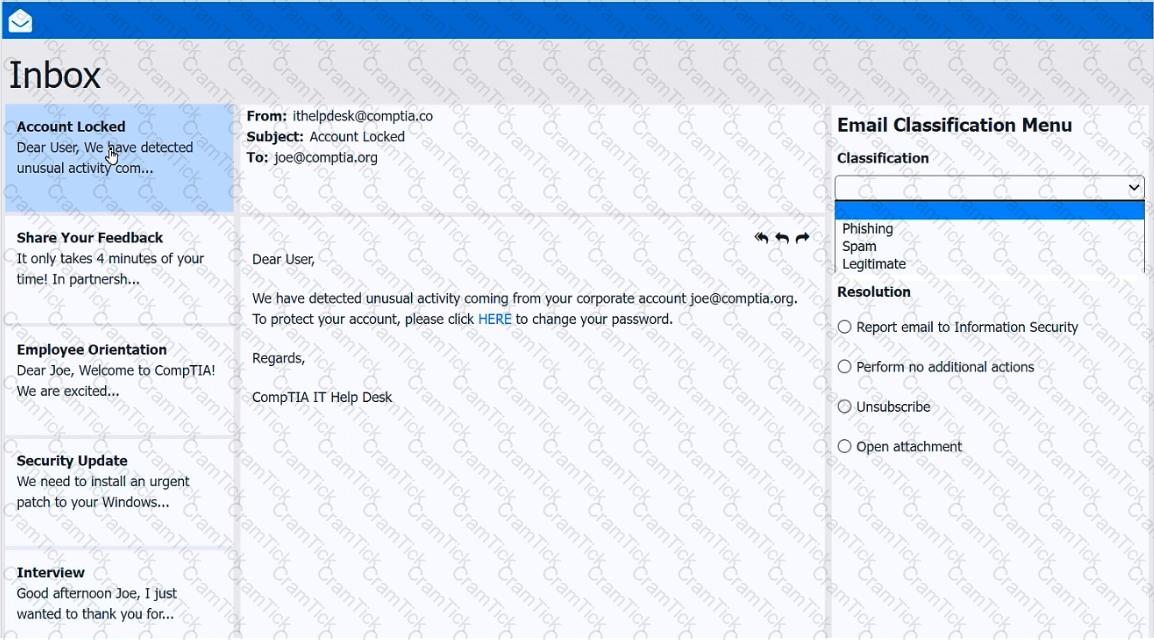
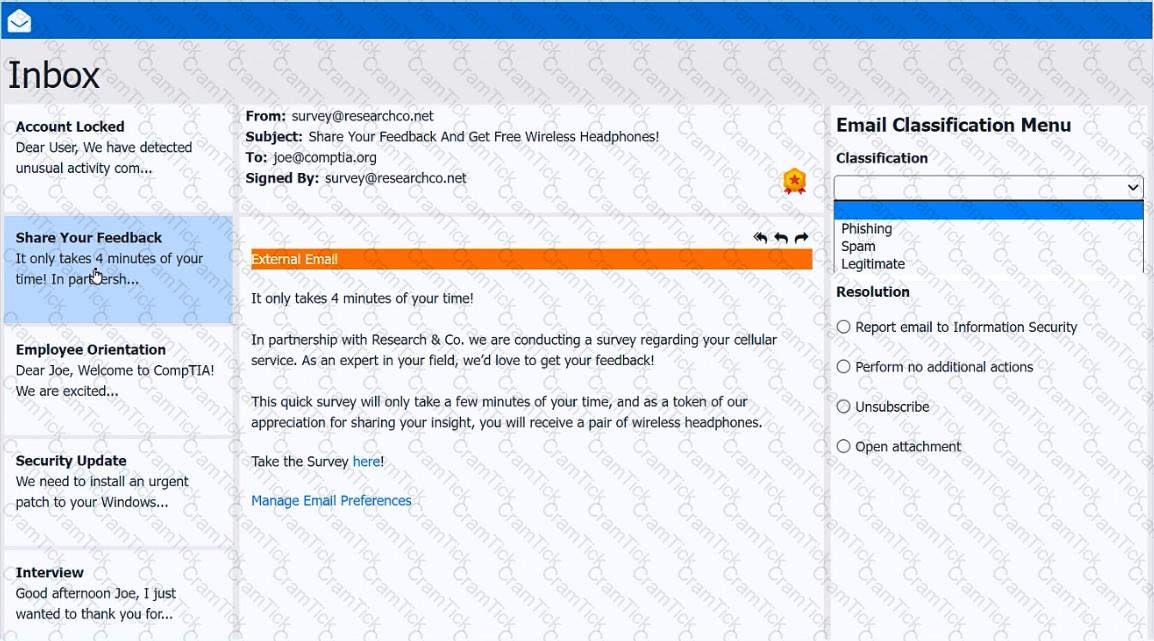
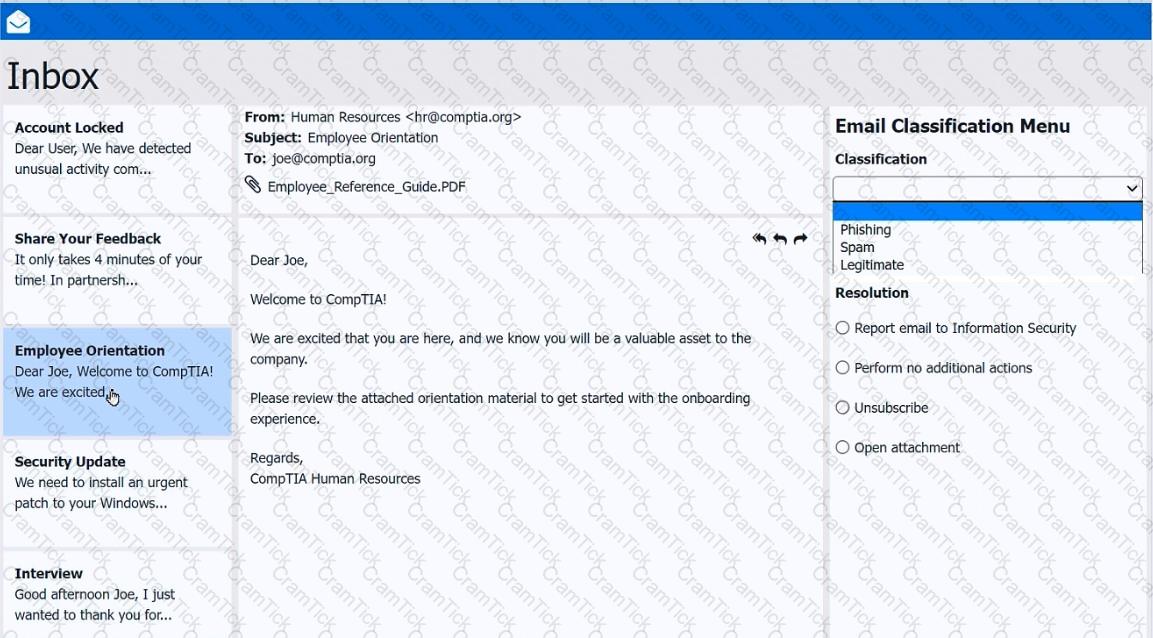
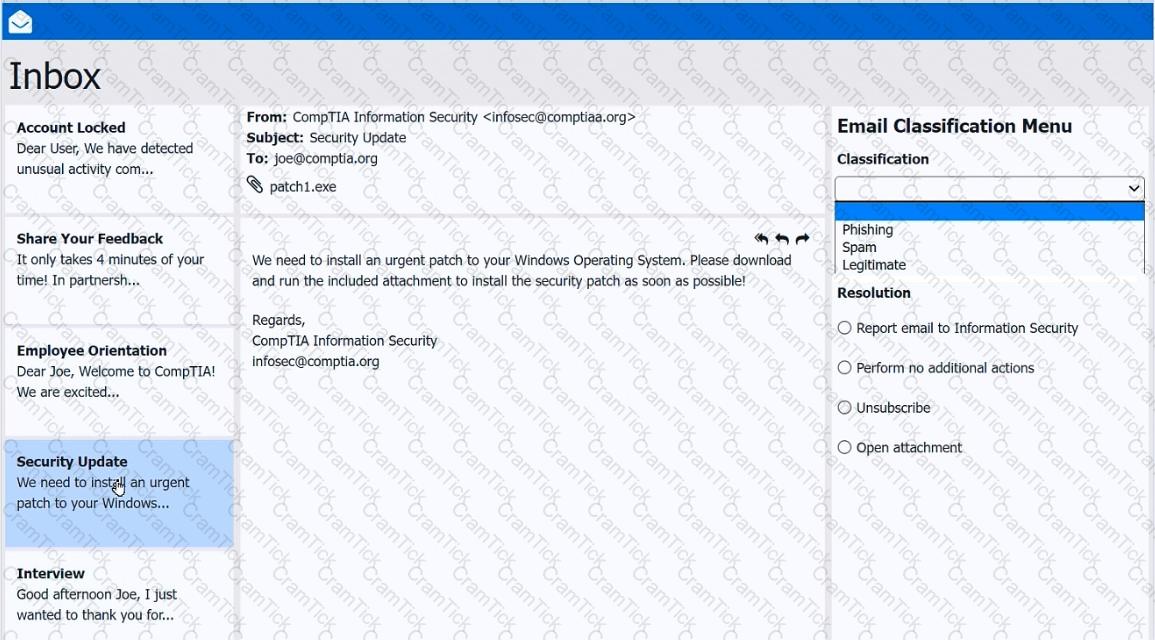
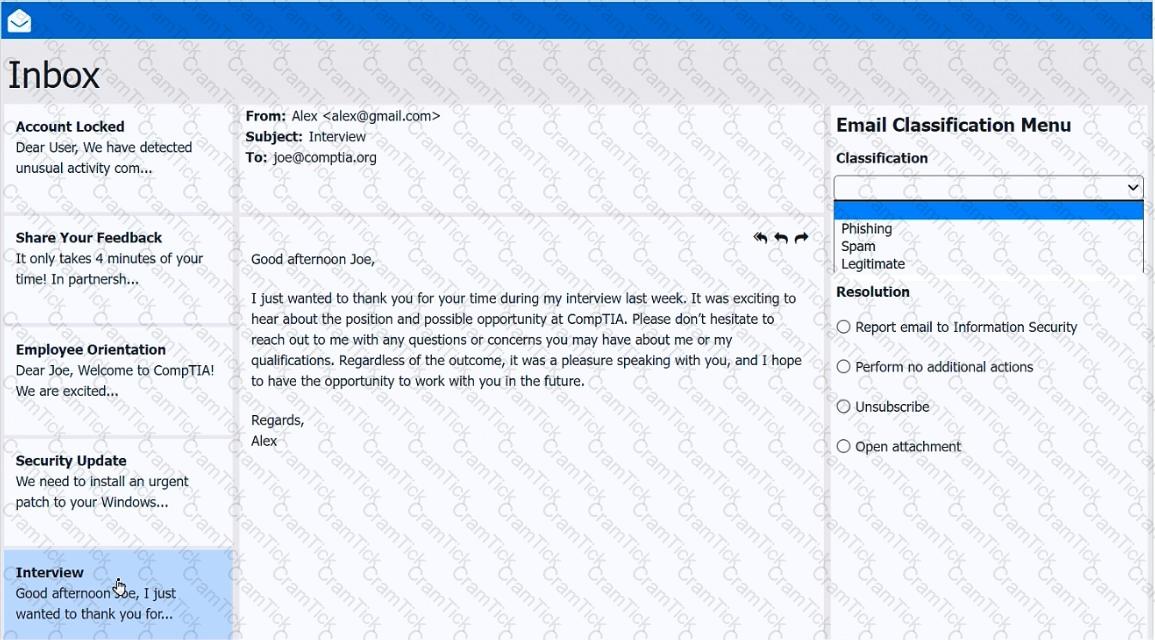
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
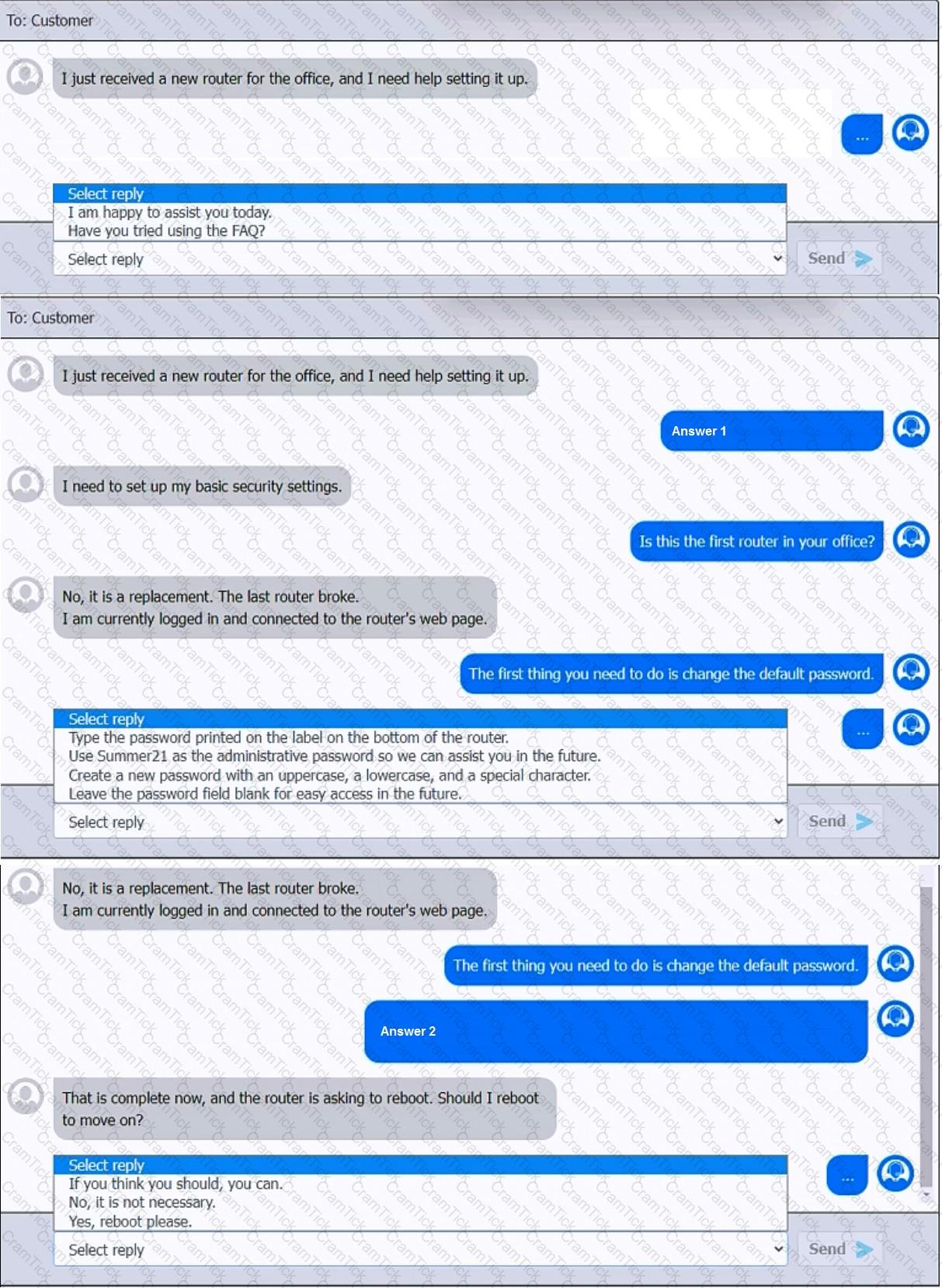
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the send button after each response to continue the chat.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A+ |