

Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
Last Update Apr 27, 2026
Total Questions : 131 With Methodical Explanation
Why Choose CramTick

Last Update Apr 27, 2026
Total Questions : 131

Last Update Apr 27, 2026
Total Questions : 131
Customers Passed
Cisco 300-215
Average Score In Real
Exam At Testing Centre
Questions came word by
word from this dump

Try a free demo of our Cisco 300-215 PDF and practice exam software before the purchase to get a closer look at practice questions and answers.

We provide up to 3 months of free after-purchase updates so that you get Cisco 300-215 practice questions of today and not yesterday.

We have a long list of satisfied customers from multiple countries. Our Cisco 300-215 practice questions will certainly assist you to get passing marks on the first attempt.

CramTick offers Cisco 300-215 PDF questions, and web-based and desktop practice tests that are consistently updated.

CramTick has a support team to answer your queries 24/7. Contact us if you face login issues, payment, and download issues. We will entertain you as soon as possible.

Thousands of customers passed the Cisco Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR) exam by using our product. We ensure that upon using our exam products, you are satisfied.
Refer to the exhibit.
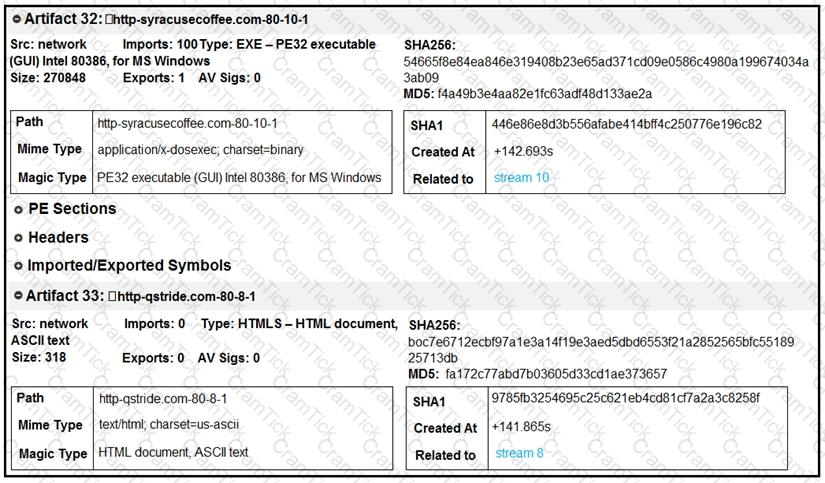
What do these artifacts indicate?
An engineer received a call to assist with an ongoing DDoS attack. The Apache server is being targeted, and availability is compromised. Which step should be taken to identify the origin of the threat?
An organization experienced a ransomware attack that resulted in the successful infection of their workstations within their network. As part of the incident response process, the organization's cybersecurity team must prepare a comprehensive root cause analysis report. This report aims to identify the primary factor or factors responsible for the successful ransomware attack and to formulate effective strategies to prevent similar incidents in the future. In this context, what should the cybersecurity engineer emphasize in the root cause analysis report to demonstrate the underlying cause of the incident?